SOLUTIONS MANUAL
CRYPTOGRAPHY AND
NETWORK SECURITY
PRINCIPLES AND PRACTICE
FIFTH EDITION
WILLIAM STALLINGS
Copyright 2010: William Stallings
�
© 2010 by William Stallings
All rights reserved. No part
of this document may be
reproduced, in any form or
by any means, or posted on
the Internet, without
permission in writing from
the author. Selected
solutions may be shared
with students, provided that
they are not available,
unsecured, on the Web.
-2-
�
NOTICE
This manual contains solutions to the review questions and
homework problems in Cryptography and Network Security, Fifth
Edition. If you spot an error in a solution or in the wording of
a problem, I would greatly appreciate it if you would
forward the information via email to ws@shore.net. An errata
sheet for this manual, if needed, is available at
http://www.box.net/shared/nh8hti5167 . File name is
S-Crypto5e-mmyy
W.S.
-3-
�
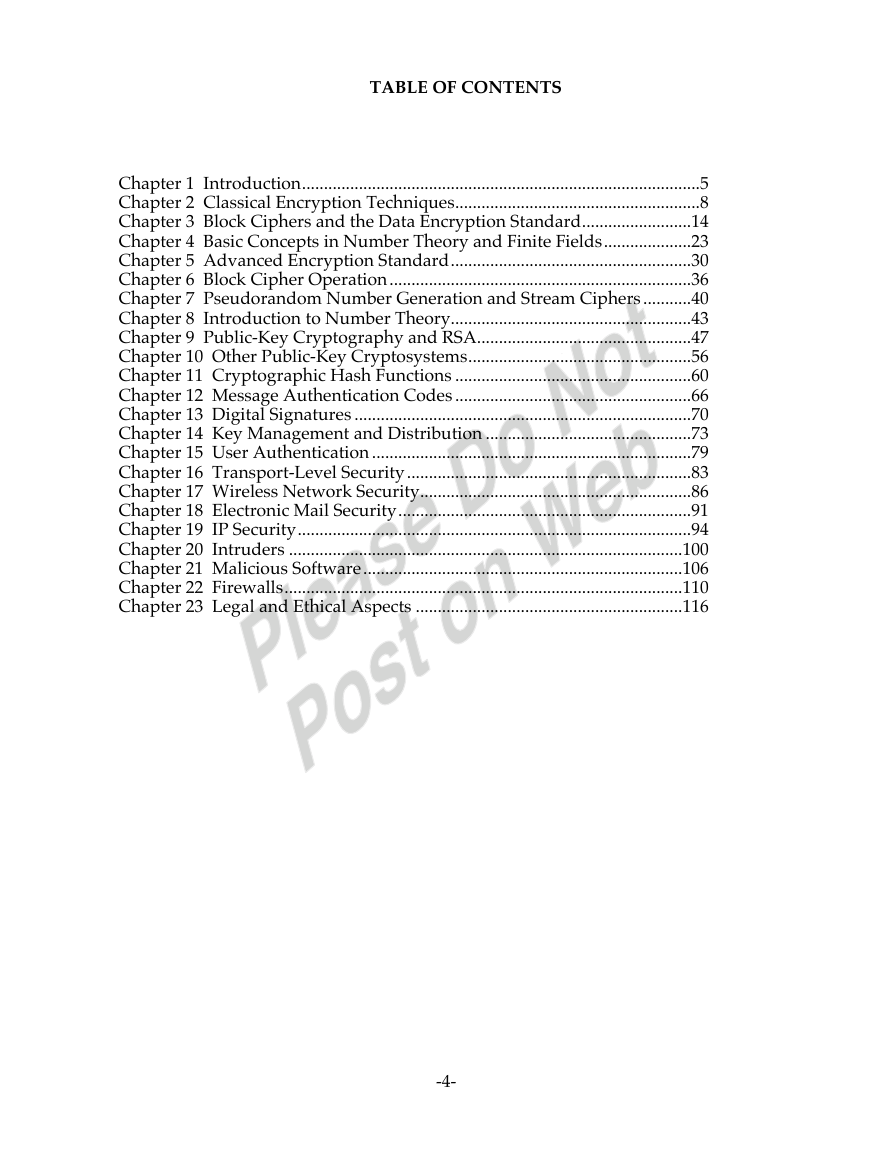
TABLE OF CONTENTS
Chapter 1 Introduction...........................................................................................5
Chapter 2 Classical Encryption Techniques........................................................8
Chapter 3 Block Ciphers and the Data Encryption Standard.........................14
Chapter 4 Basic Concepts in Number Theory and Finite Fields....................23
Chapter 5 Advanced Encryption Standard.......................................................30
Chapter 6 Block Cipher Operation.....................................................................36
Chapter 7 Pseudorandom Number Generation and Stream Ciphers...........40
Chapter 8 Introduction to Number Theory.......................................................43
Chapter 9 Public-Key Cryptography and RSA.................................................47
Chapter 10 Other Public-Key Cryptosystems...................................................56
Chapter 11 Cryptographic Hash Functions ......................................................60
Chapter 12 Message Authentication Codes......................................................66
Chapter 13 Digital Signatures .............................................................................70
Chapter 14 Key Management and Distribution ...............................................73
Chapter 15 User Authentication.........................................................................79
Chapter 16 Transport-Level Security.................................................................83
Chapter 17 Wireless Network Security..............................................................86
Chapter 18 Electronic Mail Security...................................................................91
Chapter 19 IP Security..........................................................................................94
Chapter 20 Intruders ..........................................................................................100
Chapter 21 Malicious Software.........................................................................106
Chapter 22 Firewalls...........................................................................................110
Chapter 23 Legal and Ethical Aspects .............................................................116
-4-
�
CHAPTER 1 INTRODUCTION
AA NSWERS TO
NSWERS TO QQ UESTIONS
UESTIONS
1.1 The OSI Security Architecture is a framework that provides a systematic way of
defining the requirements for security and characterizing the approaches to
satisfying those requirements. The document defines security attacks, mechanisms,
and services, and the relationships among these categories.
masquerade, replay, modification of messages, and denial of service.
1.2 Passive attacks have to do with eavesdropping on, or monitoring, transmissions.
Electronic mail, file transfers, and client/server exchanges are examples of
transmissions that can be monitored. Active attacks include the modification of
transmitted data and attempts to gain unauthorized access to computer systems.
1.3 Passive attacks: release of message contents and traffic analysis. Active attacks:
1.4 Authentication: The assurance that the communicating entity is the one that it
claims to be.
Access control: The prevention of unauthorized use of a resource (i.e., this service
controls who can have access to a resource, under what conditions access can
occur, and what those accessing the resource are allowed to do).
Data confidentiality: The protection of data from unauthorized disclosure.
Data integrity: The assurance that data received are exactly as sent by an
authorized entity (i.e., contain no modification, insertion, deletion, or replay).
Nonrepudiation: Provides protection against denial by one of the entities involved
in a communication of having participated in all or part of the communication.
Availability service: The property of a system or a system resource being
accessible and usable upon demand by an authorized system entity, according to
performance specifications for the system (i.e., a system is available if it provides
services according to the system design whenever users request them).
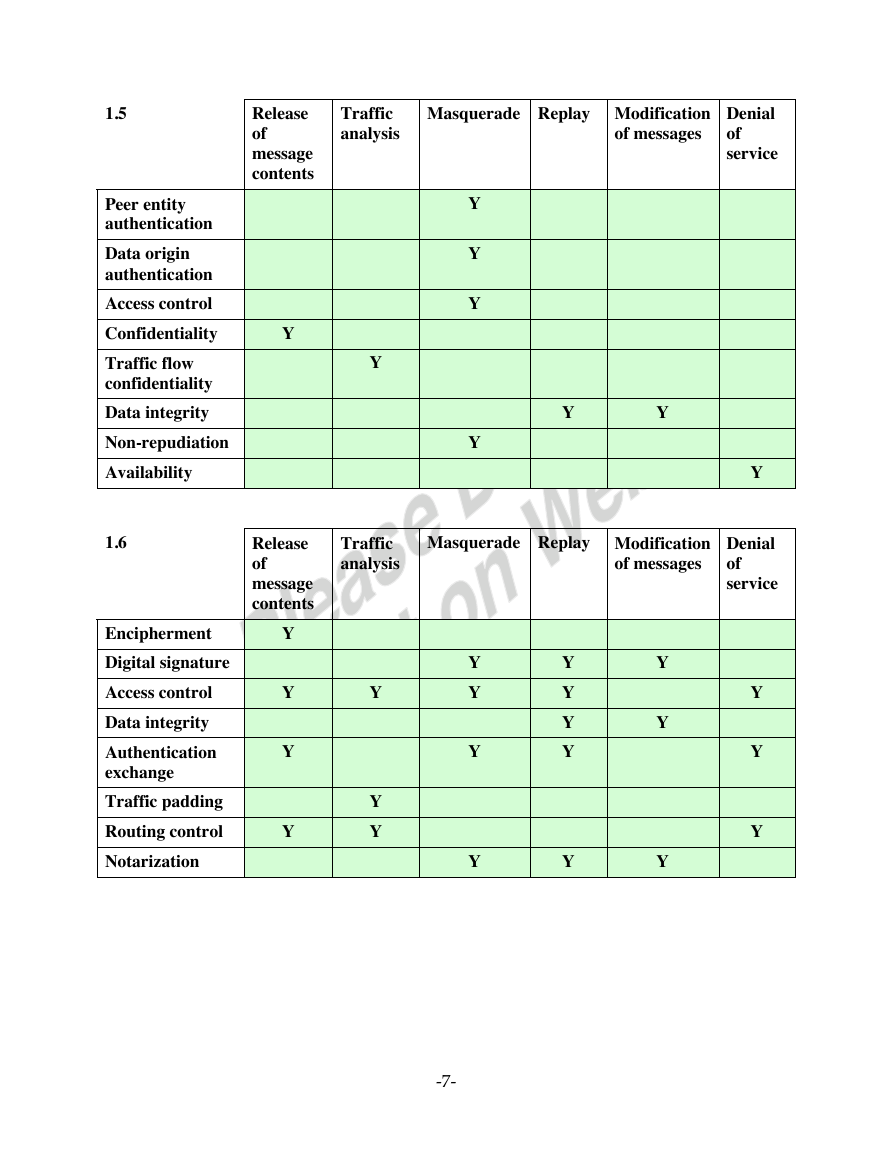
1.5 See Table 1.3.
AA NSWERS TO
NSWERS TO PP ROBLEMS
ROBLEMS
1.1 The system must keep personal identification numbers confidential, both in the
host system and during transmission for a transaction. It must protect the integrity
of account records and of individual transactions. Availability of the host system is
important to the economic well being of the bank, but not to its fiduciary
responsibility. The availability of individual teller machines is of less concern.
-5-
�
1.2 The system does not have high requirements for integrity on individual
transactions, as lasting damage will not be incurred by occasionally losing a call or
billing record. The integrity of control programs and configuration records,
however, is critical. Without these, the switching function would be defeated and
the most important attribute of all - availability - would be compromised. A
telephone switching system must also preserve the confidentiality of individual
calls, preventing one caller from overhearing another.
corporate proprietary material.
1.3 a. The system will have to assure confidentiality if it is being used to publish
1.4 a. An organization managing public information on its web server determines that
b. The system will have to assure integrity if it is being used to laws or regulations.
c. The system will have to assure availability if it is being used to publish a daily
paper.
c. A financial organization managing routine administrative information (not
there is no potential impact from a loss of confidentiality (i.e., confidentiality
requirements are not applicable), a moderate potential impact from a loss of
integrity, and a moderate potential impact from a loss of availability.
b. A law enforcement organization managing extremely sensitive investigative
information determines that the potential impact from a loss of confidentiality is
high, the potential impact from a loss of integrity is moderate, and the potential
impact from a loss of availability is moderate.
privacy-related information) determines that the potential impact from a loss of
confidentiality is low, the potential impact from a loss of integrity is low, and
the potential impact from a loss of availability is low.
d. The management within the contracting organization determines that: (i) for the
sensitive contract information, the potential impact from a loss of confidentiality
is moderate, the potential impact from a loss of integrity is moderate, and the
potential impact from a loss of availability is low; and (ii) for the routine
administrative information (non-privacy-related information), the potential
impact from a loss of confidentiality is low, the potential impact from a loss of
integrity is low, and the potential impact from a loss of availability is low.
e. The management at the power plant determines that: (i) for the sensor data
being acquired by the SCADA system, there is no potential impact from a loss of
confidentiality, a high potential impact from a loss of integrity, and a high
potential impact from a loss of availability; and (ii) for the administrative
information being processed by the system, there is a low potential impact from
a loss of confidentiality, a low potential impact from a loss of integrity, and a
low potential impact from a loss of availability. Examples from FIPS 199.
-6-
�
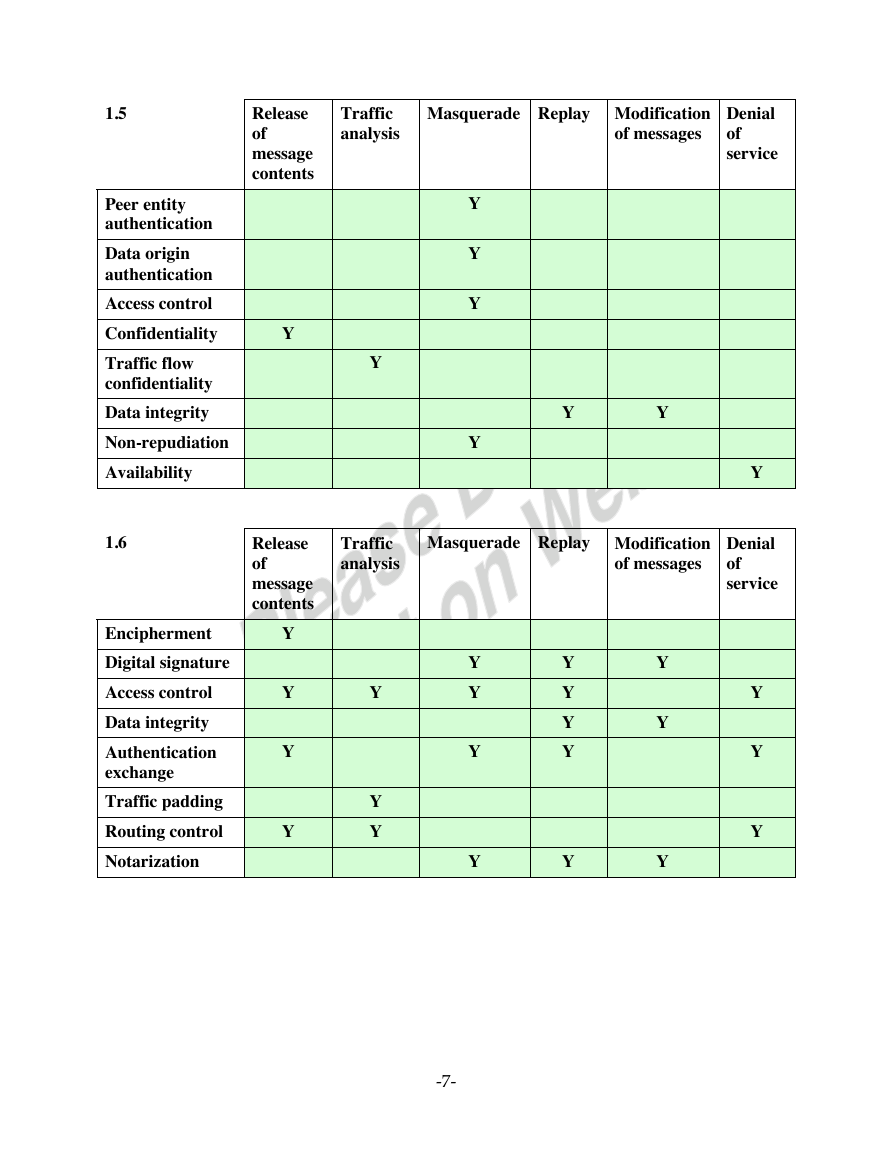
1.5
Peer entity
authentication
Data origin
authentication
Access control
Confidentiality
Traffic flow
confidentiality
Data integrity
Non-repudiation
Availability
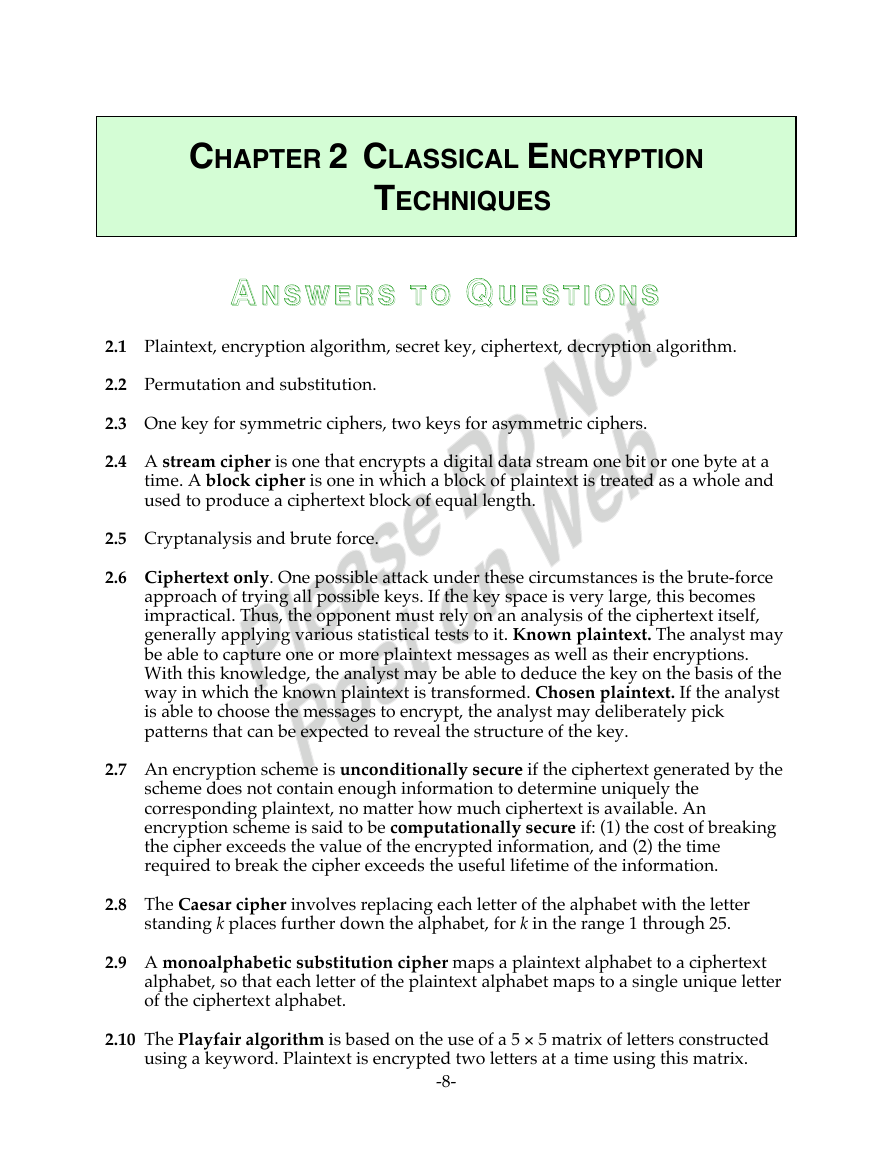
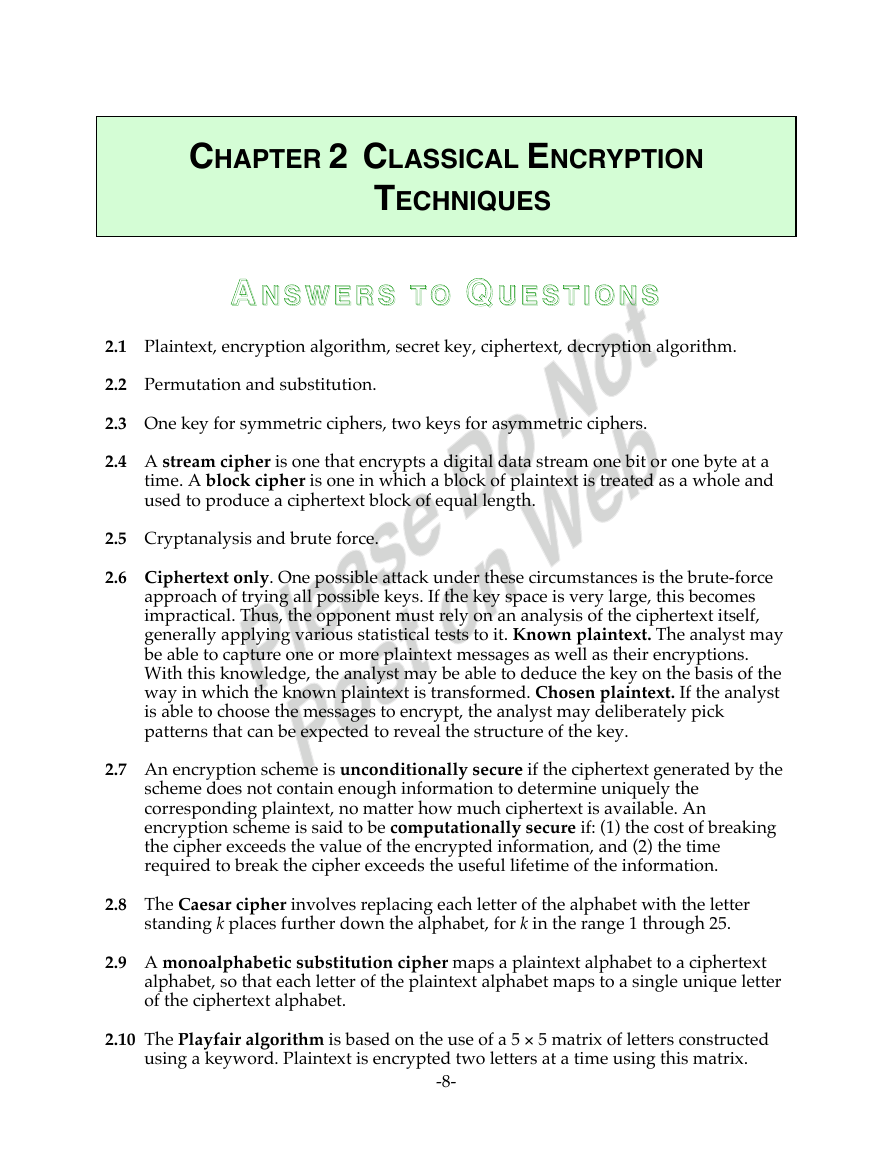
1.6
Encipherment
Digital signature
Access control
Data integrity
Authentication
exchange
Traffic padding
Routing control
Notarization
Release
of
message
contents
Y
Release
of
message
contents
Y
Y
Y
Y
Traffic
analysis
Masquerade Replay Modification
of messages
Y
Y
Y
Y
Y
Y
Y
Denial
of
service
Y
Traffic
analysis
Masquerade Replay Modification
of messages
Denial
of
service
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
Y
-7-
�
CHAPTER 2 CLASSICAL ENCRYPTION
TECHNIQUES
AA NSWERS TO
NSWERS TO QQ UESTIONS
UESTIONS
2.1 Plaintext, encryption algorithm, secret key, ciphertext, decryption algorithm.
2.2 Permutation and substitution.
2.3 One key for symmetric ciphers, two keys for asymmetric ciphers.
2.4 A stream cipher is one that encrypts a digital data stream one bit or one byte at a
time. A block cipher is one in which a block of plaintext is treated as a whole and
used to produce a ciphertext block of equal length.
2.5 Cryptanalysis and brute force.
2.6 Ciphertext only. One possible attack under these circumstances is the brute-force
approach of trying all possible keys. If the key space is very large, this becomes
impractical. Thus, the opponent must rely on an analysis of the ciphertext itself,
generally applying various statistical tests to it. Known plaintext. The analyst may
be able to capture one or more plaintext messages as well as their encryptions.
With this knowledge, the analyst may be able to deduce the key on the basis of the
way in which the known plaintext is transformed. Chosen plaintext. If the analyst
is able to choose the messages to encrypt, the analyst may deliberately pick
patterns that can be expected to reveal the structure of the key.
2.7 An encryption scheme is unconditionally secure if the ciphertext generated by the
scheme does not contain enough information to determine uniquely the
corresponding plaintext, no matter how much ciphertext is available. An
encryption scheme is said to be computationally secure if: (1) the cost of breaking
the cipher exceeds the value of the encrypted information, and (2) the time
required to break the cipher exceeds the useful lifetime of the information.
2.8 The Caesar cipher involves replacing each letter of the alphabet with the letter
2.9 A monoalphabetic substitution cipher maps a plaintext alphabet to a ciphertext
standing k places further down the alphabet, for k in the range 1 through 25.
alphabet, so that each letter of the plaintext alphabet maps to a single unique letter
of the ciphertext alphabet.
2.10 The Playfair algorithm is based on the use of a 5 × 5 matrix of letters constructed
using a keyword. Plaintext is encrypted two letters at a time using this matrix.
-8-
�


 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc