iOS Penetration
Testing
A Definitive Guide to iOS Security
—
First Edition
—
Kunal Relan
�
iOS Penetration Testing A Definitive Guide to iOS Security First Edition Kunal Relan �
iOS Penetration Testing: A Definitive Guide to iOS SecurityKunal Relan Noida, Uttar Pradesh India ISBN-13 (pbk): 978-1-4842-2354-3 ISBN-13 (electronic): 978-1-4842-2355-0DOI 10.1007/978-1-4842-2355-0 Library of Congress Control Number: 2016960329Copyright © 2016 by Kunal RelanThis work is subject to copyright. All rights are reserved by the Publisher, whether the whole or part of the material is concerned, specifically the rights of translation, reprinting, reuse of illustrations, recitation, broadcasting, reproduction on microfilms or in any other physical way, and transmission or information storage and retrieval, electronic adaptation, computer software, or by similar or dissimilar methodology now known or hereafter developed.Trademarked names, logos, and images may appear in this book. Rather than use a trademark symbol with every occurrence of a trademarked name, logo, or image we use the names, logos, and images only in an editorial fashion and to the benefit of the trademark owner, with no intention of infringement of the trademark.The use in this publication of trade names, trademarks, service marks, and similar terms, even if they are not identified as such, is not to be taken as an expression of opinion as to whether or not they are subject to proprietary rights.While the advice and information in this book are believed to be true and accurate at the date of publication, neither the authors nor the editors nor the publisher can accept any legal responsibility for any errors or omissions that may be made. The publisher makes no warranty, express or implied, with respect to the material contained herein.Managing Director: Welmoed SpahrLead Editor: Nikhil KarkalTechnical Reviewer: Nishant Das PatnaikEditorial Board: Steve Anglin, Pramila Balan, Laura Berendson, Aaron Black, Louise Corrigan, Jonathan Gennick, Robert Hutchinson, Celestin Suresh John, Nikhil Karkal, James Markham, Susan McDermott, Matthew Moodie, Natalie Pao, Gwenan SpearingCoordinating Editor: Prachi MehtaCopy Editor: Kezia EndsleyCompositor: SPi GlobalIndexer: SPi GlobalArtist: SPi GlobalDistributed to the book trade worldwide by Springer Science+Business Media New York, 233 Spring Street, 6th Floor, New York, NY 10013. Phone 1-800-SPRINGER, fax (201) 348-4505, e-mail orders-ny@springer-sbm.com , or visit www.springeronline.com . Apress Media, LLC is a California LLC and the sole member (owner) is Springer Science + Business Media Finance Inc (SSBM Finance Inc). SSBM Finance Inc is a Delaware corporation. For information on translations, please e-mail rights@apress.com , or visit www.apress.com . Apress and friends of ED books may be purchased in bulk for academic, corporate, or promotional use. eBook versions and licenses are also available for most titles. For more information, reference our Special Bulk Sales–eBook Licensing web page at www.apress.com/bulk-sales . Any source code or other supplementary materials referenced by the author in this text are available to readers at www.apress.com . For detailed information about how to locate your book’s source code, go to www.apress.com/source-code/ . Readers can also access source code at SpringerLink in the Supplementary Material section for each chapter. Printed on acid-free paper�
Th is book is dedicated to my mom, my spiritual guru for inspiring me to live, my mentor who always supported me in this journey, and to all the weirdoes like me; I love you all. �
vContents at a GlanceAbout the Author ............................................................................xiiiAbout the Technical Reviewer .........................................................xvAcknowledgments .........................................................................xviiIntroduction ....................................................................................xix ■Chapter 1: Introduction to iOS ........................................................1 ■Chapter 2: iOS App Development Basics ......................................13 ■Chapter 3: iOS App Vulnerabilities and Jailbreaking ....................31 ■Chapter 4: Blackbox Testing iOS Apps ..........................................47 ■Chapter 5: iOS Security Toolkit .....................................................73 ■Chapter 6: Automating App Testing ..............................................97 ■Chapter 7: iOS App Security Practices .......................................119Index ..............................................................................................131�
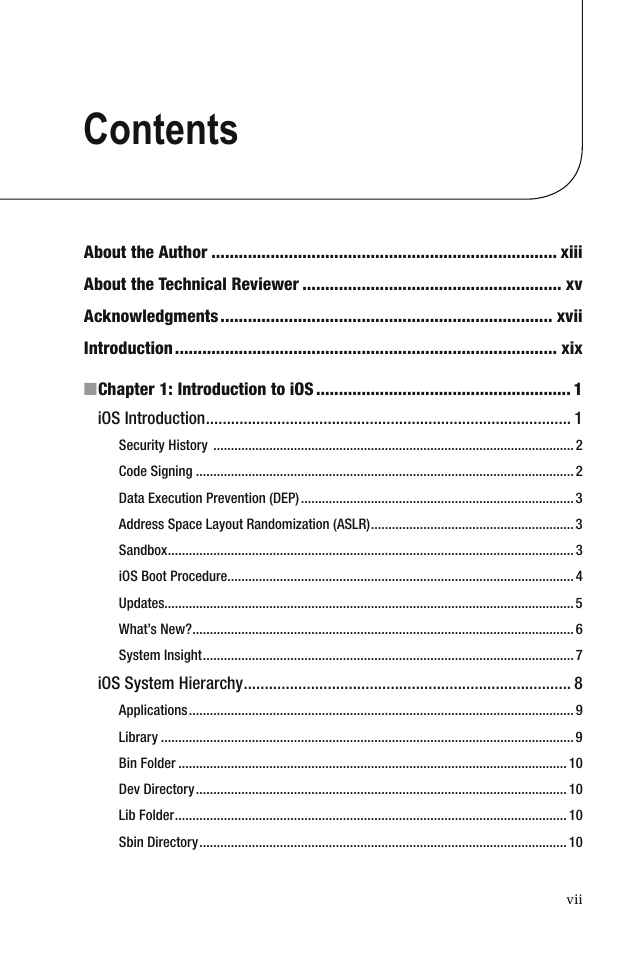
viiContentsAbout the Author ............................................................................xiiiAbout the Technical Reviewer .........................................................xvAcknowledgments .........................................................................xviiIntroduction ....................................................................................xix ■Chapter 1: Introduction to iOS ........................................................1 iOS Introduction .......................................................................................1 Security History .......................................................................................................2 Code Signing ............................................................................................................2 Data Execution Prevention (DEP) ..............................................................................3 Address Space Layout Randomization (ASLR) ..........................................................3 Sandbox ....................................................................................................................3 iOS Boot Procedure ...................................................................................................4 Updates.....................................................................................................................5 What’s New? .............................................................................................................6 System Insight ..........................................................................................................7 iOS System Hierarchy ..............................................................................8 Applications ..............................................................................................................9 Library ......................................................................................................................9 Bin Folder ...............................................................................................................10 Dev Directory ..........................................................................................................10 Lib Folder ................................................................................................................10 Sbin Directory .........................................................................................................10�
■ CONTENTSviii Tmp Directory .........................................................................................................10 Developer Directory ................................................................................................10 System Directory ....................................................................................................10 Boot Directory .........................................................................................................11 Etc Directory ...........................................................................................................11 mnt Directory ..........................................................................................................11 usr Directory ...........................................................................................................11 var Directory ...........................................................................................................11 User Directory .........................................................................................................11 Private Directory .....................................................................................................11 iOS Application Overview ......................................................................11 Summary ...............................................................................................12 ■Chapter 2: iOS App Development Basics ......................................13 Introduction to Objective-C and Swift ...................................................13 Objective-C Runtime ...............................................................................................13 Basic Terminology in Objective-C ...........................................................................14 Object Creation .......................................................................................................15 Data Types ..............................................................................................................15 Methods ................................................................................................16 Instance Methods ...................................................................................................16 Class Methods ........................................................................................................17 Introduction to Swift ..............................................................................17 Swift Runtime .........................................................................................................18 Compatibility with Objective-C ...............................................................................18 Stored Properties ....................................................................................................18 Classes and Methods..............................................................................................19 Structures ...............................................................................................................20�
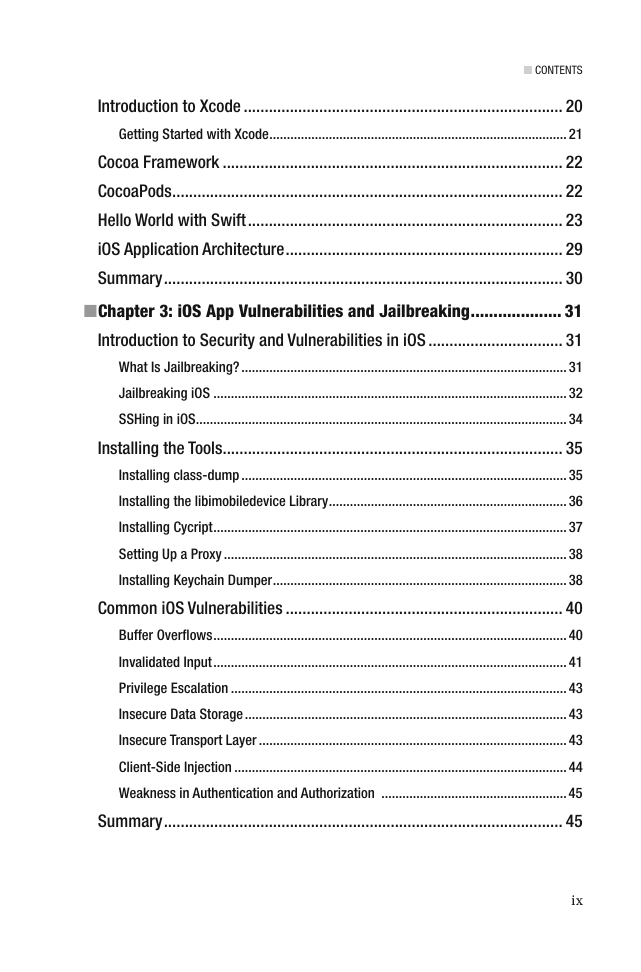
■ CONTENTSix Introduction to Xcode ............................................................................20 Getting Started with Xcode .....................................................................................21 Cocoa Framework .................................................................................22 CocoaPods .............................................................................................22 Hello World with Swift ...........................................................................23 iOS Application Architecture ..................................................................29 Summary ...............................................................................................30 ■Chapter 3: iOS App Vulnerabilities and Jailbreaking ....................31 Introduction to Security and Vulnerabilities in iOS ................................31 What Is Jailbreaking? .............................................................................................31 Jailbreaking iOS .....................................................................................................32 SSHing in iOS ..........................................................................................................34 Installing the Tools .................................................................................35 Installing class-dump .............................................................................................35 Installing the libimobiledevice Library ....................................................................36 Installing Cycript .....................................................................................................37 Setting Up a Proxy ..................................................................................................38 Installing Keychain Dumper ....................................................................................38 Common iOS Vulnerabilities ..................................................................40 Buffer Overfl ows .....................................................................................................40 Invalidated Input .....................................................................................................41 Privilege Escalation ................................................................................................43 Insecure Data Storage ............................................................................................43 Insecure Transport Layer ........................................................................................43 Client-Side Injection ...............................................................................................44 Weakness in Authentication and Authorization .....................................................45 Summary ...............................................................................................45�






 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc