2014 IEEE 12th International Conference on Dependable, Autonomic and Secure Computing
Provably Secure Anonymous Multi-Receiver Identity-Based Encryption with
Shorter Ciphertext
School of Information Engineering, Dalian Ocean University, Dalian, China
Huaqun Wang
wanghuaqun@aliyun.com
Abstract—Anonymous multi-receiver identity-based encryp-
tion (ID-MRE) can protect the receiver identity besides message
confidentiality. It can be applied in many fields, such as VoIP
(Voice over Internet Protocol) and pay-TV systems. Based
on the bilinear pairings, this paper proposes an anonymous
ID-MRE scheme. The proposed scheme satisfies the indis-
tinguishability of encryptions under selective multi-identity,
adaptive chosen ciphertext attacks (IND-sMID- CCA2). On the
other hand, it also satisfies the anonymous indistinguishability
of encryptions under selective multi-identity, adaptive chosen
ciphertext attacks (ANON-sMID-CCA2). The security analysis
and performance analysis show that our scheme is provably
secure and efficient.
Keywords-anonymity; multi-receiver; identity-based encryp-
tion; provable security;
I. INTRODUCTION
Public key encryption scheme must satisfy two basic
security requirements: security and efficiency. The standard
security notion for a encryption scheme is indistinguisha-
bility against adaptive chosen ciphertext attacks, i.e., IND-
CCA2 for short. With respect to efficiency, there are two
main aspects to consider: computational efficiency and com-
munication efficiency. As a special public key encryption
system, multi-receiver encryption can broadcasts a message
with a high-level of computational efficiency while retaining
security. This encryption system can be used in the real
world where there are many users, each with a public
key. The service provider sends them the encrypted data.
Although multi-receiver encryption can solve some problems
in the real world, it cannot protect the privacy of receivers.
On the other hand, it is very important to protect receiver
privacy in some fields, such as VoIP, pay-TV, et al. Thus,
anonymous ID-MRE attracted attentions of some experts
from different fields. It is meaningful to design the anony-
mous ID-MRE security model and the concrete anonymous
ID-MRE scheme.
A. Motivation
In the pay-TV or streaming audio/video services,
the
service provider will encrypt the audio/video and sends the
ciphertext to all the receivers who have ordered the program.
Upon receiving the ciphertext, the receiver decrypts the
ciphertext by using his/her personal private key. When the
client orders the sensitive program, he/she usually expects
to hide his/her identity even to other receivers. Thus, it is
important and necessary to study anonymous multi-receiver
encryption scheme.
B. Related works
The concept of multi-receiver public key encryption was
independently formalized by Bellare et al. [1] and Baudron,
et al. [2]. It can be used in many fields, for example,
underwater sensor networks [3], large-scale RFID system-
s [4], etc. After that, many multi-receiver identity-based
encryption schemes are designed [5], [6]. These schemes
do not protect receivers privacy. Until 2012, Fan et al.
presented an anonymous multi-receiver identity-based en-
cryption scheme by taking use of Lagrange interpolating
polynomial mechanisms [7]. It’s regretful that their scheme
does not satisfy the property of anonymity [8], [9]. After
that, Hur et al. proposed a novel privacy-preserving identity-
based broadcast encryption scheme by taking use of key
encapsulation mechanism [10]. In some situations, such as
ordering sensitive TV programmes, a receiver or customer
usually expects that any other receiver or customer does
not know her/his ID when ordering the TV programmes.
Anonymous multi-receiver IBE has a lot of applications. It
is necessary to study this type of cryptographic system.
In an identity-based public key cryptography system,
every user has his/her own identity (ID). These ID may
be some meaningful or easily memorized strings. ID-based
cryptography has attracted a lot of researchers and has
gained some results [11], [12], [13], [14]. Since elliptic curve
public key cryptography is more secure than RSA based on
the same security level, this cryptography system develops
faster. After bilinear pairings were proposed, they are used
to design public key cryptographic schemes [15], [16], [17],
[18]. Bilinear pairings can also be used to study anonymous
ID-MRE cryptographic system.
C. Our contributions
In this paper, we propose a provably secure anonymous
multi-receiver identity-based encryption scheme. The secu-
rity analysis and performance analysis show that our scheme
is provably secure and highly efficient.
978-1-4799-5079-9/14 $31.00 © 2014 IEEE
DOI 10.1109/DASC.2014.24
85
�
D. Organization
The rest of the paper is organized as follows. Section II
introduces preliminaries and Section III gives our proposed
anonymous ID-MRE scheme. In Section IV, we give formal
security proof and efficiency analysis on our scheme. Finally,
Section V gives the conclusions.
II. PRELIMINARIES
Anonymous ID-MRE system model and security model
are given in this section. At the same time, bilinear pairings
and some corresponding difficult problems are also depicted
as follows.
A. System model and security model
In anonymous ID-MRE protocol, there must exist three
different entities: KGC (key generation center), Sender and
Decrypter. We start with the precise definition of anonymous
ID-MRE scheme, then we give the corresponding security
model.
Definition 1 (Anonymous ID-MRE): An
anonymous
multi-receiver identity-based encryption (anonymous ID-
MRE) scheme is a collection of four polynomial
time
algorithms: Setup, Extract, Encrypt, and Decrypt.
1) Setup: KGC generates the master key s and the other
public parameters which include the corresponding
master public key Ppub and we denote the public
parameter set as params. The parameter set params
are publicly known and s is kept secret.
2) Extract: When KGC receives a private key query from
a client IDi, KGC runs this algorithm to generate the
private key di, i.e., di = Extract(params, s, IDi).
Finally, KGC sends di to the client IDi.
3) Encrypt: The encrypter chooses multiple identities
S = (ID1, · · · , IDt) of the receivers. Input
the
system public parameters params and a plaintext
message M, the encrypter runs this algorithm to gen-
erate the ciphertext C = Encrypt(params, S, M ).
4) Decrypt: When the decrypter IDi receives a cipher-
text C, it decrypts C by using the public parameters
params and its private key di. Finally, it gets the
plaintext M = Decrypt(params, C, di).
A secure anonymous ID-MRE scheme must satisfy the
two properties: ANON-sMID-CCA2 and IND-sMID-CCA2.
ANON-sMID-CCA2 is the abbreviation of selective identity
receiver anonymity under the condition of adaptive chosen
ciphertext attack.
Definition 2 (ANON-sMID-CCA2): Let A be
a
polynomial-time adversary and C be a challenger. Let
be an anonymous ID-MRE scheme. A interacts with C
in the following game:
1) Setup: C runs (params, mpk, msk) ← KeyGen(1ˆk),
sends (params, mpk) to the adversary A and keeps
confidential the master secret key msk. A outputs the
target identity set S = {ID0, ID1}.
2) First-Phase Queries: A adaptively makes a number of
different queries to C. Each query can be one of the
following.
• Extract
can
adversary
queries. The
the private key of
ask
any identity ID.
for
the private key skID by running
C gets
Extract(params, mpk, msk, ID) and forwards
it to the adversary. Denote the extracted identity
set by S1. The restriction is S
S1 = φ.
• Hash queries. The adversary makes Hash func-
tion queries adaptively. C responds the Hash val-
ues to the adversary.
• Decrypt queries. The adversary makes decrypt
queries adaptively. For a query (C ∗, IDi) queried
by the adversary, C returns the plaintext M.
3) Challenge:
These queries may be asked adaptively, that is, each
query may depend on the answers obtained to the
previous queries.
A
set
{IDi1, · · · , IDir} and message M. Upon receiving
{IDi1, · · · , IDir} and M, C randomly chooses
{0, 1} and creates a target ciphertext
β ∈R
C ∗ = Encrypt(params, IDi1, · · · , IDir, IDβ, M ).
Then C returns C ∗ to A.
identity
outputs
the
4) Second-Phase Queries: A issues Extract queries,
Hash queries and Decrypt queries similar to First-
Phase Queries. In Extract queries, denote the extracted
identity set by S2, the restriction is S
S2) = φ.
In Decrypt queries, the restriction is C = C ∗.
(S1
Guess: Finally, A outputs its guess β ∈ {0, 1} and wins the
game if β = β.
Such an adversary A is referred to an ANON-sMID-
CCA2 adversary. We define A’s guessing advantage as the
following:
1
2
|
AN ON −sM ID−CCA2
Adv
(A) = |P r[β = β] −
The scheme
is said to be (τ, �)-ANON-sMID-CCA2
secure if for any ANON-sMID-CCA2 adversary A, with-
in polynomial running time τ, A’s guessing advantage
Adv
(A) is less than �.
AN ON −sM ID−CCA2
Definition 3 (IND-sMID-CCA2): Let
a
polynomial-time adversary and C be a Challenger. Let
be an anonymous ID-MRE scheme. A interacts with C
be
A
in the following game:
1) Setup: C runs (params, mpk, msk) ← KeyGen(1ˆk),
sends (params, mpk) to the adversary and keeps confi-
dential the master secret key msk. A outputs the target
multiple identity set S = {ID1, · · · , IDt} where t is
a positive integer.
2) First-Phase Queries: The adversary adaptively makes
a number of different queries to C. Each query can be
one of the following.
86
�
• Extract
can
adversary
queries. The
the private key of
ask
any identity ID.
for
the private key skID by running
C gets
Extract(params, mpk, msk, ID) and forwards
it to the adversary. Denote the extracted identity
set by S1. The constraint is S
S1 = φ.
• Hash queries. The adversary makes Hash func-
tion queries adaptively. C responds the Hash val-
ues to the adversary.
• Decrypt queries. The adversary makes decrypt
queries adaptively. For a query (C ∗, IDi) queried
by the adversary, C returns the plaintext M.
These queries may be asked adaptively, that is, each
query may depend on the answers obtained to the
previous queries.
3) Challenge: A outputs a target plaintext pair (M0, M1).
Upon receiving (M0, M1), C randomly chooses
β ∈R {0, 1} and creates a target ciphertext C ∗ =
Encrypt(params, ID1, · · · , IDt, Mβ). Then C re-
turns C ∗ to A.
4) Second-Phase Queries: A issues Extract queries,
Hash queries and Decrypt queries similar to First-
Phase Queries. In Extract queries, denote the extracted
identity set by S2, the restriction is S
S2) = φ.
In Decrypt queries, the restriction is C = C ∗.
(S1
Guess: Finally, A outputs its guess β ∈ {0, 1} and wins the
game if β = β.
Such an adversary A is referred to an IND-sMID-CCA2
adversary. We define A’s guessing advantage as the follow-
ing:
1
2
|
IN D−sM ID−CCA2
Adv
(A) = |P r[β = β] −
The scheme
is said to be (τ, �)-IND-sMID-CCA2 se-
cure if for any IND-sMID- CCA2 adversary A, with-
in polynomial running time τ, A’s guessing advantage
Adv
(A) is less than �.
IN D−sM ID−CCA2
Thus, we present the three definitions which characterize
the concept of anonymous ID-MRE, ANON-sMID-CCA2
and IND-sMID-CCA2.
B. Bilinear Pairings and Difficult Problems
The pairing-based cryptographic scheme can offer lower
transmission cost compared with the RSA-based schemes
due to the smaller security parameter ˆk . We briefly introduce
the bilinear pairings as follows.
Let G1 and G2 be two cyclic groups with the same prime
order q, i.e., |G1| = |G2| = q. G1 is an additive group and
G2 is a multiplicative group. Let P be a generator of G1.
Let e : G1 × G1 → G2 be a bilinear map which satisfies the
following properties:
1) Bilinearity: ∀Q, R, S ∈ G1 and a, b ∈ Z ∗
q ,
e(aR, bQ) = e(R, Q)ab
87
2) Non-degeneracy: ∃Q, R ∈ G1 such that e(Q, R) =
1G2.
3) Computability: ∀Q, R ∈ G1,
algorithm to calculate e(Q, R).
there is an efficient
Such a bilinear map e can be constructed by the modified
Weil [19] or Tate pairings [20] on elliptic curves. Then, we
give the difficult problems on G1 and G2 as follows [18].
Computational BDH. We say that an algorithm A has
= � in solving the computational
the advantage AdvCBDH
BDH problem in (G1, G2) if
A
P r[A(P, aP, bP, cP ) = e(P, P )abc] ≥ �
where the probability is over the random choice of exponents
a, b, c in Zq, the random choice of generator P of G1, and
the random bits used by A.
Decisional BDH. We say that an algorithm A has the
= � in solving the decisional BDH
advantage AdvDBDH
problem (DBDHP) in (G1, G2) if
A
|P r[A(P, aP, bP, cP, e(P, P )abc ) = 0]−
A(P, aP, bP, cP, T ) = 0]| ≥ �
where the probability is over the random choice of generator
P of G1, the random choice of exponents a, b, c in Zq, the
random choice T ∈R G2 and the random bits used by A.
Definition 4: We say that the (t, �)-Computational BDH
assumption holds in (G1, G2) if no t-time algorithm has
advantage at least � in solving Computational BDH problem
in (G1, G2).
Definition 5: We say that the (t, �)-Decisional BDH as-
sumption holds in (G1, G2) if no t-time algorithm has
advantage at least � in solving Decisional BDH problem
in (G1, G2).
III. OUR PROPOSED ANONYMOUS ID-MRE SCHEME
Our proposed CCA2-secure anonymous multi-receiver
identity-based encryption scheme consists of four algorithm-
s: Setup, Extract, Encrypt and Decrypt.
Setup: The system initializes the global parameters as
follows.
1) Pick up an integer s ∈R Z ∗
2) Choose five cryptographic hash functions
q and set Ppub = sP .
H : {0, 1}∗ → Z ∗
q
H1 : {0, 1}∗ → G∗
1
H2 : G2 → {0, 1}ω,
H3 : {0, 1}z × {0, 1}ω∗ × G2
H4 : {0, 1}∗ × {0, 1}z × G2
1 → {0, 1}ω
1 → {0, 1}ω−z
where ω, z are integers satisfying that H4 is collision-
resilient and ˆk ≤ z ≤ ω. The symmetric encryption
algorithm and decryption algorithm using a key k are
denoted as Ek() and Dk(), respectively.
3) Publish the system parameters
params = {G1, G2, q, e, n, P, Ppub, H, H1, H2, H3, H4}
�
and keep the master key s secret.
IV. SECURITY ANALYSIS AND EFFICIENCY ANALYSIS
Extract. Input the system parameters params and an entity
identity IDi ∈ {0, 1}∗ for i ∈ [1, n], the system returns the
entity’s private key di = sQi, where Qi = H1(IDi).
Encrypt. The sender chooses the receivers set (ID
1,
i, · · · , ID
t) from the whole client set (ID1, · · · ,
· · · , ID
IDi, · · · , IDn). The sender performs the following proce-
dures.
1) Pick an integer r ∈R Z ∗
q and a random string σ ∈R
{0, 1}z, and set U1 = rP, U2 = H(σ)P .
2) For i = 1, · · · , t, compute
Ri = σ||H4(M, σ, U1, U2)
V = EH3(σ,R1,··· ,Rt,U1,U2)(M )
H2(e(Ppub, Q
i)r)
where Q
i = H1(ID
i).
3) Prepare the ciphertext C and broadcast it where
C = (R1, · · · , Rt, U1, U2, V )
Decrypt. Input C, params and one private key d
i , an
i decrypts the ciphertext
authorized receiver with identity ID
C as follows.
1) For j = 1, · · · , t, compute Rj
Then, it assigns its first z bits to σ
bits to h∗
4.
H2(e(U1, d
i)) .
j and the last ω − z
?= H(σ
2) Verify whether U2
j )P holds or not. If there
¨k that satisfies the equation for some ¨k, 1 ≤
i is not
exists a σ
¨k ≤ t, then go to the next step; otherwise, ID
an authorized receiver.
3) Derive M = DH3(σ
4) Verify whether h∗
4
,R1,··· ,Rt,U1,U2)(V ).
?= H4(M , σ
¨k
¨k, U1, U2) holds or
i accepts the message M ;
not. If so, the receiver ID
otherwise, he rejects the ciphertext.
Correctness of the proposed scheme can be proved as
follows.
Proof: Without
an
authorized
let
IDi
be
ciphertext
C = (R1, · · · , Rt, U1, U2, V ), where 1 ≤ i ≤ t. We
can get
generality,
in
the
loss
of
receiver
= σ holds
Since h∗
because of the collision-resilient hash function H4. Thus,
we can get
¨k, U1, U2) holds, then σ
¨k
M = DH3(σ
,R1,··· ,Rt,U1,U2)(V )
= DH3(σ,R1,··· ,Rt,U1,U2)(V )
= M
¨k
i))
= σ||H4(M, σ, U1, U2)
H2(e(U1, d
Ri
H2(e(U1, d
i))
= σ||H4(M, σ, U1, U2)
H2(e(U1, d
i))
= σ||H4(M, σ, U1, U2)
4 = H4(M , σ
H2(e(Ppub, Q
i)r)
H2(e(rP, sQ
i))
A. Security analysis
We now prove that our anonymous ID-MRE scheme is
ANON-sMID-CCA2 secure and IND-sMID-CCA2 secure
under the DBDH assumption.
2ω ))� and τ = T + (qH1
Theorem 1: Our proposed anonymous ID-MRE scheme
is (τ, qH , qH1 , qH2 , qH3 , qH4 , qe, qd, �)-ANON-sMID-CCA2
secure under the (T, �)-DBDHP assumption, where � ≥
(1 − (1 − 1
2ω−z )(1 − 1
+ qe + qd)τ1 +
+ qe + qd)O(1).
(t + 1)τ2 + (qH + qH1
(qH , qH1 , qH2 , qH3 , qH4 , qe, qd denote the number of queries
to the hash functions
H, H1, H2, H3, H4, Extract queries, Decryption queries. τ1
and τ2 denote the computing time for the scalar multiplica-
tion in G1 and a pairing e, respectively.)
+ qH3
+ qH4
+ qH2
AN ON −sM ID−CCA2
Proof: Let the ANON-sMID-CCA2 adversary A have
(A) ≥ � within the
the advantage Adv
running time τ where
is the our anonymous ID-MRE
scheme. Suppose that A makes at most qe Extract queries, at
most qd Decrypt queries, and at most qH , qH1 , qH2 , qH3 , qH4
queries to the hash functions H, H1, H2, H3, H4, respective-
ly. Let the tables TH, TH1, TH2, TH3, and TH4 store the
results of querying H, H1, H2, H3, and H4, respectively.
Let the challenger be C. Algorithm C works by interacting
with A in the following game :
Setup: C is given as input a tuple (P, P1, P2, P3, T ) that is
either sampled from PBDH (where T = e(g, g)abc) or from
RBDH (where T is uniform and independent in G2), where
P1 = aP, P2 = bP, P3 = cP and a, b, c are unknown. C
sets Ppub = P1 as the system public key. The corresponding
system master key is unknown. A selects two challenged
identities IDd1 and IDd2. We denote the identity set as
Sa = {IDd1, IDd2}.
First-Phase Queries
H query: C is given the input σj ∈ {0, 1}z. C looks for
the table TH for the record (σj, ∗). If there exists such a
record, C retrieves the record (σj, sj) and returns sj to A
as the response. Otherwise, C chooses sj ∈R Z ∗
q and sets
H(σj) = sj. At the same time, C adds the record (σj , sj)
into the table TH and returns sj to A as the response.
H1 query: C is given the input IDi. C looks for the table
TH1 for the record (∗, IDi, ∗). If there exists such a record,
C retrieves the record (ci, IDi, ri) and returns riP to A
if ci = 0 or returns riP3 to A if ci = 1 as the response.
Otherwise, if IDi ∈ Sa, C denotes ci = 0 and chooses ri ∈R
q . C sets H1(IDi) = riP and returns riP as the response.
Z ∗
If IDi ∈ Sa, C denotes ci = 1 and chooses ri ∈R Z ∗
q . C
sets H1(IDi) = riP3 and returns riP3 as the response. C
adds the record (ci, IDi, ri) into the table TH1.
H2 query: C is given the input ei ∈ G2. C looks for
the table TH2 for the record (ei, ∗). If there exists such a
record, C retrieves the record (ei, ti) and returns ti to A as
the response. Otherwise, C chooses ti ∈R {0, 1}ω and sets
88
�
H2(ei) = ti. C returns ti to A as the response. C adds the
record (ei, ti) into the table TH2.
H3 query: C is given the input (σi, R1i, · · · , Rli, U1i,
for
for
the
the
table TH3
U2i). C looks
record
(σi, R1i, · · · , Rli, U1i, U2i, ∗). If there exists such a record,
C retrieves the record (σi, R1i, · · · , Rli, U1i, U2i, li) and
to A as the response. Otherwise, C chooses
returns li
li ∈R {0, 1}ω and sets H3(σi, R1i, · · · , Rli, U1i, U2i) = li.
to A as the response. C adds the record
C returns li
(σi, R1i, · · · , Rli, U1i, U2i, li) into the table TH3.
H4: C is given the input (Mi, σi, U1i, U2i). C looks for the
table TH4 for the record (Mi, σi, U1i, U2i, ∗). If there exists
such a record, C retrieves the record (Mi, σi, U1i, U2i, zi)
and returns zi to A as the response. Otherwise, C chooses
zi ∈R {0, 1}ω−z and sets H4(Mi, σi, U1i, U2i) = zi.
to A as the response. C adds the record
C returns zi
(Mi, σi, U1i, U2i, zi) into the table TH4.
Extract: C is given the input IDi ∈ Sa. C queries H1
oracle for IDi and gets the αi. Then, C compute di = αiP1
as the response. Since
di = αiP1 = αiaP = aH(IDi)
di is the secret key of the user IDi. When IDi ∈ Sa, C
fails. In this phase, A can adaptively query the challenger C
to extract the users’ secret keys.
Decrypt: C is given the ciphertext-receiver pair (C, IDj )
where C = (R1i, · · · , Rti, U1i, U2i). If IDj ∈ Sa, C can
get di and decrypt C to get the plaintext M. If IDj ∈
Sa, C looks for the table TH3. If there exist the records
(∗, R1i, · · · , Rti, U1i, U2i, l∗), where ∗, l∗ are default. If ∗ =
?= U2i holds or not. If it
σj, C checks whether H(σj)P
holds, go to the next step. Otherwise, C checks the next
record until it holds. Suppose the satisfied record is ∗ = σ∗
and the corresponding hash value is ˆl∗. Taking use of ˆl∗ to
decrypt V and get M ∗ = Dˆl∗ (V ). Then C looks for the table
TH4. If there exists the record (M ∗, σ, U1i, U2i, z∗), where
z∗ is default, C returns M ∗ as the palintext. Otherwise, fail.
According to the process of encryption, the probability of
failure is at most 1 − (1 − 1
The
Challenge
sends
{IDj1 , IDj2 , · · · , IDjt , M } and Sa to the challenger.
C chooses β ∈R {d1, d2}. Suppose that the multi-receiver
identity set
is S = {IDj1 , IDj2 , · · · , IDjt , IDβ}. By
using the phase Extract, C can get all
the secret keys
}. We denote
of
the identities {IDj1 , IDj2 , · · · , IDjt
}.
these corresponding secret keys as {dj1 , dj2 , · · · , djt
C queries H1 and gets the record (cβ, IDβ, rβ), where
cβ = 1. C chooses a random string σ ∈R {0, 1}z and sets
U1 = P2, U2 = H(σ)P . For i = j1, j2, · · · , jt, compute
2ω−z )(1 − 1
adversary
2ω ).
A
Ri = σ||H4(M, σ, U1, U2)
Rβ = σ||H4(M, σ, U1, U2)
V = EH3(σ,R1,··· ,Rt,Rβ ,U1,U2)(M )
H2(e(U1, di))
H2(T rβ )
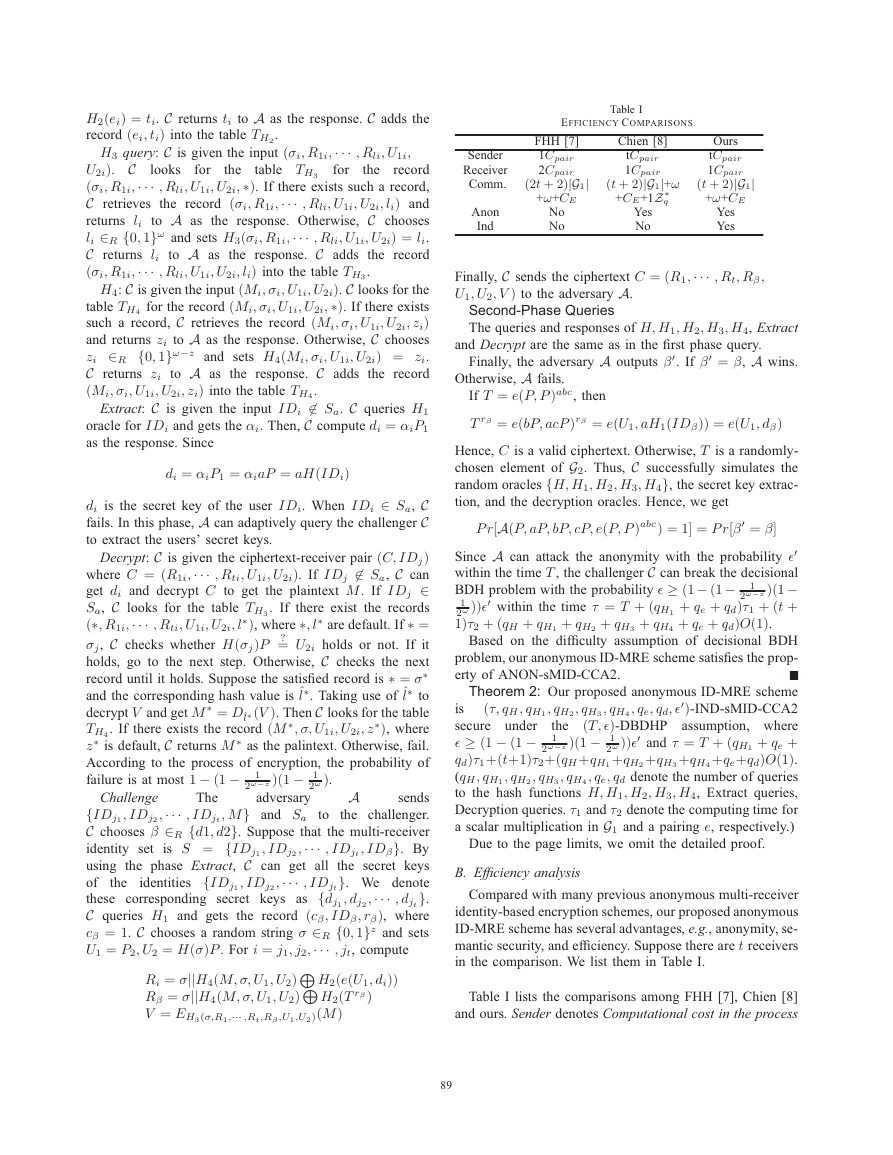
Table I
EFFICIENCY COMPARISONS
FHH [7]
1Cpair
2Cpair
Chien [8]
tCpair
1Cpair
Ours
tCpair
1Cpair
Yes
Yes
(2t + 2)|G1|
+ω+CE
(t + 2)|G1|+ω
+CE+1Z ∗
q
(t + 2)|G1|
+ω+CE
No
No
Yes
No
Sender
Receiver
Comm.
Anon
Ind
Finally, C sends the ciphertext C = (R1, · · · , Rt, Rβ,
U1, U2, V ) to the adversary A.
Second-Phase Queries
The queries and responses of H, H1, H2, H3, H4, Extract
and Decrypt are the same as in the first phase query.
Finally, the adversary A outputs β. If β = β, A wins.
Otherwise, A fails.
If T = e(P, P )abc, then
T rβ = e(bP, acP )rβ = e(U1, aH1(IDβ)) = e(U1, dβ)
Hence, C is a valid ciphertext. Otherwise, T is a randomly-
chosen element of G2. Thus, C successfully simulates the
random oracles {H, H1, H2, H3, H4}, the secret key extrac-
tion, and the decryption oracles. Hence, we get
P r[A(P, aP, bP, cP, e(P, P )abc) = 1] = P r[β = β]
Since A can attack the anonymity with the probability �
within the time T , the challenger C can break the decisional
BDH problem with the probability � ≥ (1 − (1 − 1
2ω−z )(1 −
2ω ))� within the time τ = T + (qH1
1
+ qe + qd)τ1 + (t +
+ qe + qd)O(1).
1)τ2 + (qH + qH1
+ qH4
+ qH3
+ qH2
Based on the difficulty assumption of decisional BDH
problem, our anonymous ID-MRE scheme satisfies the prop-
erty of ANON-sMID-CCA2.
Theorem 2: Our proposed anonymous ID-MRE scheme
(τ, qH , qH1 , qH2 , qH3 , qH4 , qe, qd, �)-IND-sMID-CCA2
is
(T, �)-DBDHP assumption, where
the
secure
� ≥ (1 − (1 − 1
2ω−z )(1 − 1
+ qe +
+qe+qd)O(1).
qd)τ1+(t+1)τ2+(qH +qH1
(qH , qH1 , qH2 , qH3 , qH4 , qe, qd denote the number of queries
to the hash functions H, H1, H2, H3, H4, Extract queries,
Decryption queries. τ1 and τ2 denote the computing time for
a scalar multiplication in G1 and a pairing e, respectively.)
2ω ))� and τ = T + (qH1
+qH2
under
+qH3
+qH4
Due to the page limits, we omit the detailed proof.
B. Efficiency analysis
Compared with many previous anonymous multi-receiver
identity-based encryption schemes, our proposed anonymous
ID-MRE scheme has several advantages, e.g., anonymity, se-
mantic security, and efficiency. Suppose there are t receivers
in the comparison. We list them in Table I.
Table I lists the comparisons among FHH [7], Chien [8]
and ours. Sender denotes Computational cost in the process
89
�
[7] Fan C., Huang L., Ho P. (2010) Anonymous multi-receiver
IEEE Transactions on Computers,
identity-based encryption.
59(9), pp. 1239-1249.
[8] Chien H. (2012) Improved anonymous multi-receiver identity-
based encryption. The Computer Journal. 55(4), pp.439-446.
[9] Wang H., Zhang Y., Xiong H., Qin B. (2012) Cryptanalysis and
improvements of an anonymous multi-receiver identity-based
encryption scheme.
IET Inf. Secur.. 6(1), pp. 20-27.
[10] Hur
J., Park C., Hwang S.
identity-based broadcast
doi:10.1016/j.inffus.2011.03.003.
encryption.
(2012) Privacy-preserving
Informat Fusion,
[11] Shamir A. (1984) Identity-based cryptosystems and signature
schemes. Proc. CRYPTO 84. Santa Barbara, California, USA.
Lecture Notes in Computer Science 196, pp. 47-53. Springer.
[12] Boneh D., and Franklin M. (2003) Identity-based encryption
from the weil pairing. SIAM J. Comput.. 32(3), pp. 586-615.
[13] Boyen X., and Waters B. (2006) Anonymous hierarchical
identity-based encryption (without random oracles). Proc.
CRYPTO 2006. Santa Barbara, California, USA. Lecture Notes
in Computer Science 4117, pp. 290-307. Springer.
[14] Abdalla M., Kiltz E., and Neven G. (2008) Generalised key
IET Inf.
delegation for hierarchical identity-based encryption.
Secur.. 2(3), pp. 67-78.
[15] Boneh D., and Hamburg M. (2008) Generalized identity
based and broadcast encryption schemes. Asiacrypt 2008.
Melbourne, Australia. Lecture Notes in Computer Science
5350, pp. 455-470. Springer.
[16] Boneh D., Boyen X., and Halevi S., Chosen ciphertext secure
public key threshold encryption without random oracles. RSA-
CT’06. San Jose, CA, USA. Lecture Notes in Computer
Science 3860, pp. 226-243. Springer.
[17] Boneh D., and Boyen X. (2008) Short signatures without
random oracles. Journal of Cryptology. 21(2), pp. 149-177.
[18] Boneh D., and Boyen X. (2004) Efficient selective-id secure i-
dentity based encryption without random oracles. EUROCRYP-
T 2004. Interlaken, Switzerland. Lecture Notes in Computer
Science 3027, pp.223-238. Springer.
[19] Boneh D., and Franklin M. (2001) Identity-based encryption
from the weil pairing. Advances in Cryptology-CRYPTO 2001.
Santa Barbara, California, USA. Lecture Notes in Computer
Science 2139, pp. 213-229. Springer.
[20] Miyaji A., Nakabayashi M., and Takano S., (2001) New
explicit conditions of elliptic curve traces for FR-reduction.
IEICE Transactions Fundamentals, 5, pp. 1234-1243.
of encryption. Receiver denotes Computational cost in the
process of decryption. Comm. denotes Communication cost.
Anon denotes ANON-sMID-CCA2. Ind denotes IND-sMID-
CCA2. Cpair denotes Computation cost of pairings. |G1|
denotes “the bit length of a point on G1”. CE denotes “the
bit length of a cipher by the symmetric encryption E”. From
the comparisons, we know that FHH [7], Chien [8] do not
satisfy IND-sMID-CCA2 (i.e., Ind) although they claimed
their schemes are secure. At the same time, FHH [7] can not
also satisfy ANON-sMID-CCA2 (i.e., Anon). Our scheme
is provably secure in the random oracle model. From the
performance comparison, our scheme is also efficient.
V. CONCLUSIONS
In this paper, by taking use of the bilinear pairings,
we propose a provably secure anonymous multi-receiver
identity-based encryption scheme with shorter ciphertext.
Our scheme is provably secure and efficient in the random
oracle model.
ACKNOWLEDGMENT
The author sincerely thanks the Editor for allocating qual-
ified and valu- able referees. The author sincerely thanks the
anonymous referees for their very valuable comments. This
work was partly supported by the Nation- al Natural Science
Foundation of China (No. 61272522), by the Natural Science
Foundation of Liaoning Province (No. 2014020147), and by
the Open Project of Shanghai Key Laboratory of Trustwor-
thy Computing (No. 07dz22304201306).
REFERENCES
[1] Bellare M., Boldyreva A., and Micali S. (2000) Public-key
encryption in a multi-user setting: security proofs and improve-
ments. Advances in Cryptology-EUROCRYPT2000, Bruges
(Brugge), Belgium. Lecture Notes in Computer Science 1807,
pp. 259-274. Springer.
[2] Baudron O., Pointcheval D., and Stern J. (2000) Extended
notions of security for multicast public key cryptosystems.
ICALP 2000. Geneva, Switzerland. Lecture Notes in Computer
Science 1853, pp. 499-511. Springer.
[3] Xu J., Li K., and Min G.(2012) Reliable and energy-efficient
multipath communications in underwater sensor networks.
IEEE Trans. Parallel Distrib. Syst.. 23(7), pp.1326-1335.
[4] Liu X., Li K., Min G., Lin K., Xiao B., Shen Y., and Qu
W.(2013) Efficient unknown tag identification protocols in
large-scale rfid systems, IEEE Trans. Parallel Distrib. Syst..
Accepted, to appear.
[5] Chatterjee S., and Sarkar P.
, Multi-receiver identity-based
Progress in
key encapsulation with shortened ciphertext.
Cryptology-INDOCRYPT 2006. Kolkata, India. Lecture Notes
in Computer Science 4329, pp. 394-408. Springer.
[6] Lu L., and Hu L. (2006) Pairing-based multi-recipient public
key encryption. Proceedings of the 2006 International Con-
ference on Security & Management. Las Vegas, Nevada, USA.
pp. 159-165. 2006. CSREA.
90
�








 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc