Index of Figures
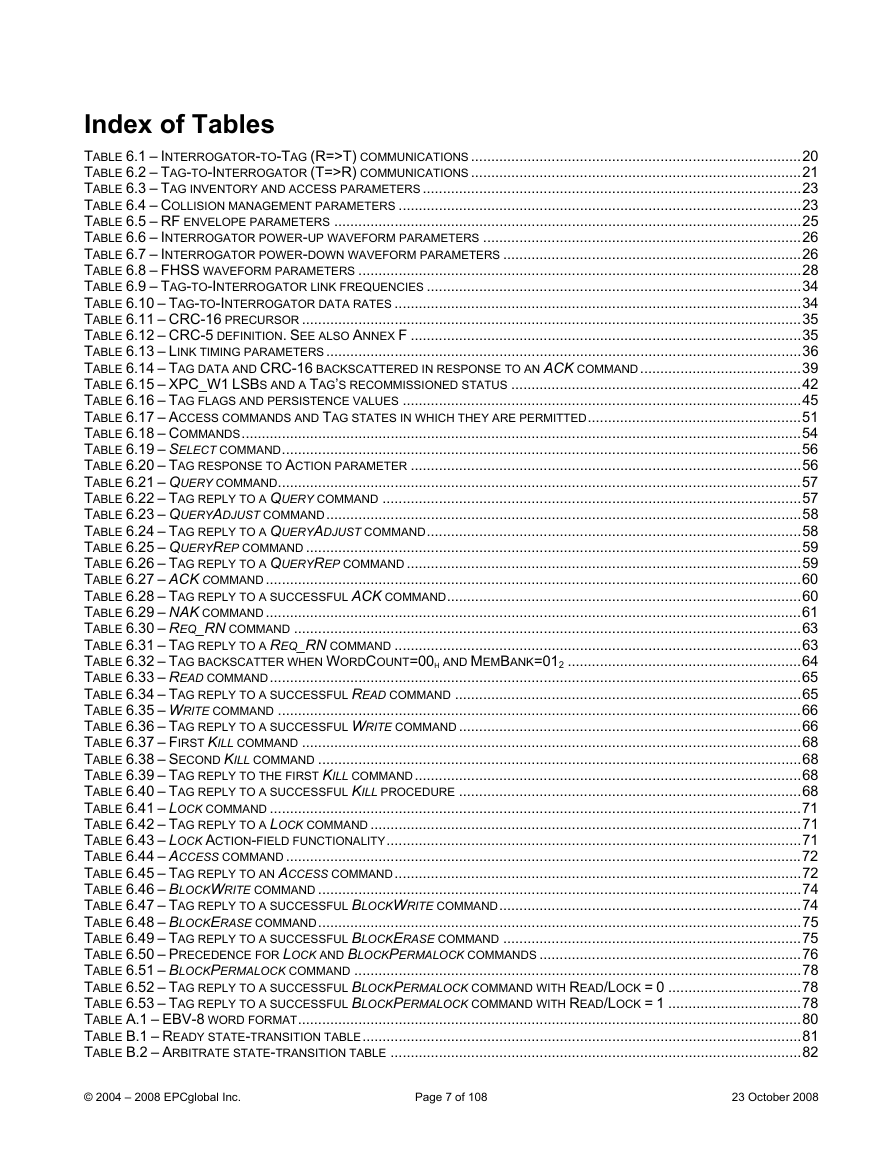
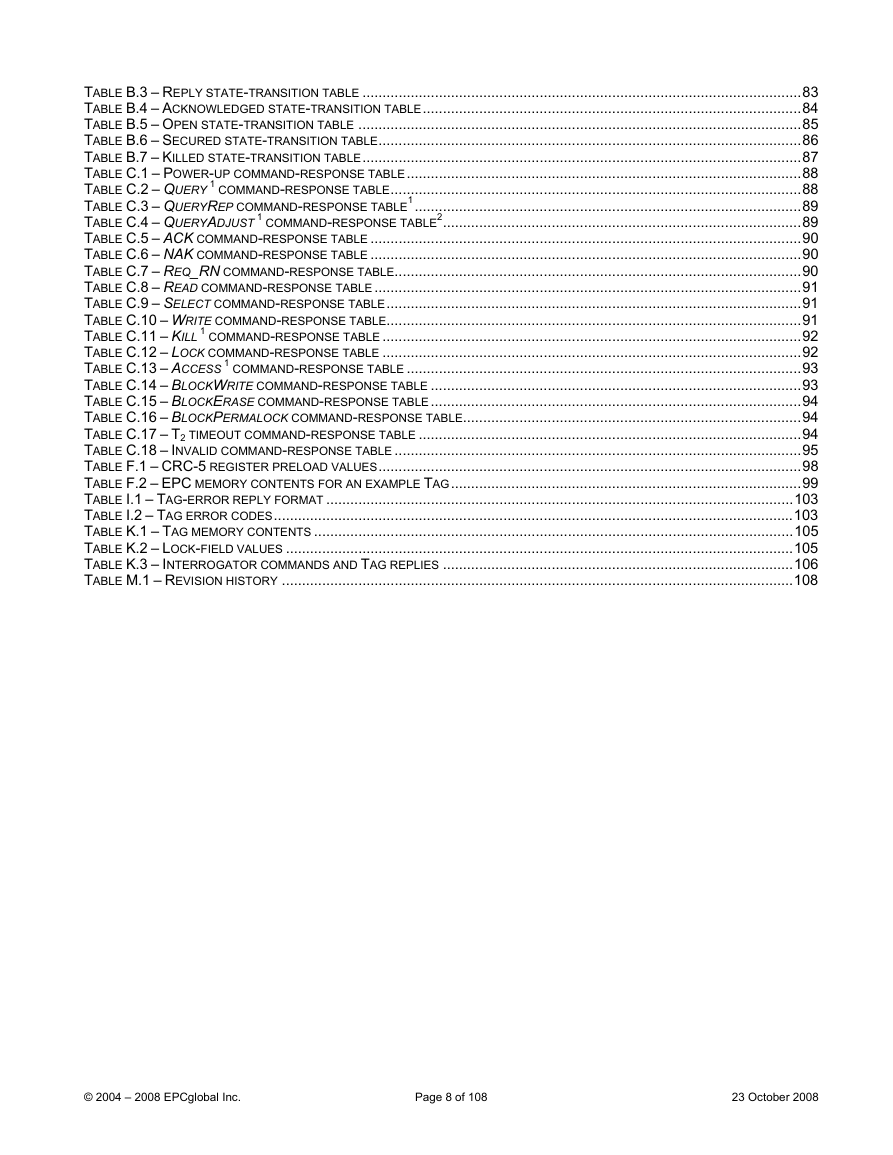
Index of Tables
Foreword
Introduction
1. Scope
2. Conformance
2.1 Claiming conformance
2.2 General conformance requirements
2.2.1 Interrogators
2.2.2 Tags
2.3 Command structure and extensibility
2.3.1 Mandatory commands
2.3.2 Optional commands
2.3.3 Proprietary commands
2.3.4 Custom commands
2.4 Reserved for Future Use (RFU)
3. Normative references
4. Terms and definitions
4.1 Additional terms and definitions
5. Symbols, abbreviated terms, and notation
5.1 Symbols
5.2 Abbreviated terms
5.3 Notation
6. Protocol requirements
6.1 Protocol overview
6.1.1 Physical layer
6.1.2 Tag-identification layer
6.2 Protocol parameters
6.2.1 Signaling – Physical and media access control (MAC) parameters
6.2.2 Logical – Operating procedure parameters
6.3 Description of operating procedure
6.3.1 Signaling
6.3.1.1 Operational frequencies
6.3.1.2 Interrogator-to-Tag (R=>T) communications
6.3.1.2.1 Interrogator frequency accuracy
6.3.1.2.2 Modulation
6.3.1.2.3 Data encoding
6.3.1.2.4 Tari values
6.3.1.2.5 R=>T RF envelope
6.3.1.2.6 Interrogator power-up waveform
6.3.1.2.7 Interrogator power-down waveform
6.3.1.2.8 R=>T preamble and frame-sync
6.3.1.2.9 Frequency-hopping spread-spectrum waveform
6.3.1.2.10 Frequency-hopping spread-spectrum channelization
6.3.1.2.11 Transmit mask
6.3.1.3 Tag-to-Interrogator (T=>R) communications
6.3.1.3.1 Modulation
6.3.1.3.2 Data encoding
6.3.1.3.2.1 FM0 baseband
6.3.1.3.2.2 FM0 preamble
6.3.1.3.2.3 Miller-modulated subcarrier
6.3.1.3.2.4 Miller subcarrier preamble
6.3.1.3.3 Tag supported Tari values and backscatter link rates
6.3.1.3.4 Tag power-up timing
6.3.1.3.5 Minimum operating field strength and backscatter strength
6.3.1.4 Transmission order
6.3.1.5 Cyclic-redundancy check (CRC)
6.3.1.6 Link timing
6.3.2 Tag selection, inventory, and access
6.3.2.1 Tag memory
6.3.2.1.1 Reserved Memory
6.3.2.1.1.1 Kill password
6.3.2.1.1.2 Access password
6.3.2.1.2 EPC Memory
6.3.2.1.2.1 CRC-16 (StoredCRC and PacketCRC)
6.3.2.1.2.2 Protocol-control (PC) word (StoredPC and PacketPC)
6.3.2.1.2.3 EPC for an EPCglobal™ Application
6.3.2.1.2.4 EPC for a non-EPCglobal™ Application
6.3.2.1.2.5 Extended Protocol Control (XPC) word or words (optional)
6.3.2.1.3 TID Memory
6.3.2.1.4 User Memory
6.3.2.1.4.1 User memory for an EPCglobal™ Application
6.3.2.1.4.2 User memory for a non-EPCglobal™ Application
6.3.2.2 Sessions and inventoried flags
6.3.2.3 Selected flag
6.3.2.4 Tag states and slot counter
6.3.2.4.1 Ready state
6.3.2.4.2 Arbitrate state
6.3.2.4.3 Reply state
6.3.2.4.4 Acknowledged state
6.3.2.4.5 Open state
6.3.2.4.6 Secured state
6.3.2.4.7 Killed state
6.3.2.4.8 Slot counter
6.3.2.5 Tag random or pseudo-random number generator
6.3.2.6 Managing Tag populations
6.3.2.7 Selecting Tag populations
6.3.2.8 Inventorying Tag populations
6.3.2.9 Accessing individual Tags
6.3.2.10 Killing or recommissioning a Tag
6.3.2.11 Interrogator commands and Tag replies
6.3.2.11.1 Select commands
6.3.2.11.1.1 Select (mandatory)
6.3.2.11.2 Inventory commands
6.3.2.11.2.1 Query (mandatory)
6.3.2.11.2.2 QueryAdjust (mandatory)
6.3.2.11.2.3 QueryRep (mandatory)
6.3.2.11.2.4 ACK (mandatory)
6.3.2.11.2.5 NAK (mandatory)
6.3.2.11.3 Access commands
6.3.2.11.3.1 Req_RN (mandatory)
6.3.2.11.3.2 Read (mandatory)
6.3.2.11.3.3 Write (mandatory)
6.3.2.11.3.4 Kill (mandatory)
6.3.2.11.3.5 Lock (mandatory)
6.3.2.11.3.6 Access (optional)
6.3.2.11.3.7 BlockWrite (optional)
6.3.2.11.3.8 BlockErase (optional)
6.3.2.11.3.9 BlockPermalock (optional)
7. Intellectual property rights intrinsic to this specification
Annex A(normative)Extensible bit vectors (EBV)
Annex B(normative)State-transition tables
B.1 Present state: Ready
B.2 Present state: Arbitrate
B.3 Present state: Reply
B.4 Present state: Acknowledged
B.5 Present state: Open
B.6 Present state: Secured
B.7 Present state: Killed
Annex C(normative)Command-Response Tables
C.1 Command response: Power-up
C.2 Command response: Query
C.3 Command response: QueryRep
C.4 Command response: QueryAdjust
C.5 Command response: ACK
C.6 Command response: NAK
C.7 Command response: Req_RN
C.8 Command response: Select
C.9 Command response: Read
C.10 Command response: Write
C.11 Command response: Kill
C.12 Command response: Lock
C.13 Command response: Access
C.14 Command response: BlockWrite
C.15 Command response: BlockErase
C.16 Command response: BlockPermalock
C.17 Command response: T2 timeout
C.18 Command response: Invalid command
Annex D(informative)Example slot-count (Q) selection algorithm
D.1 Example algorithm an Interrogator might use to choose Q
Annex E(informative)Example of Tag inventory and access
E.1 Example inventory and access of a single Tag
Annex F(informative)Calculation of 5-bit and 16-bit cyclic redundancy checks
F.1 Example CRC-5 encoder/decoder
F.2 Example CRC-16 encoder/decoder
F.3 Example CRC-16 calculations
Annex G(Normative)Multiple- and dense-Interrogator channelized signaling
G.1 Overview of dense-interrogator channelized signaling (informative)
Annex H(informative)Interrogator-to-Tag link modulation
H.1 Baseband waveforms, modulated RF, and detected waveforms
Annex I(Normative)Error codes
I.1 Tag error codes and their usage
Annex J(normative)Slot counter
J.1 Slot-counter operation
Annex K(informative)Example data-flow exchange
K.1 Overview of the data-flow exchange
K.2 Tag memory contents and lock-field values
K.3 Data-flow exchange and command sequence
Annex L(informative)Optional Tag Features
L.1 Optional Tag passwords
L.2 Optional Tag memory banks and memory-bank sizes
L.3 Optional Tag commands
L.4 Optional Tag error-code reporting format
L.5 Optional Tag backscatter modulation format
L.6 Optional Tag functionality
Annex M(informative)Revision History


 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc