2
Solutions
Patterson-1610874 978-0-12-407726-3
PII
�
Chapter 2 Solutions
S-3
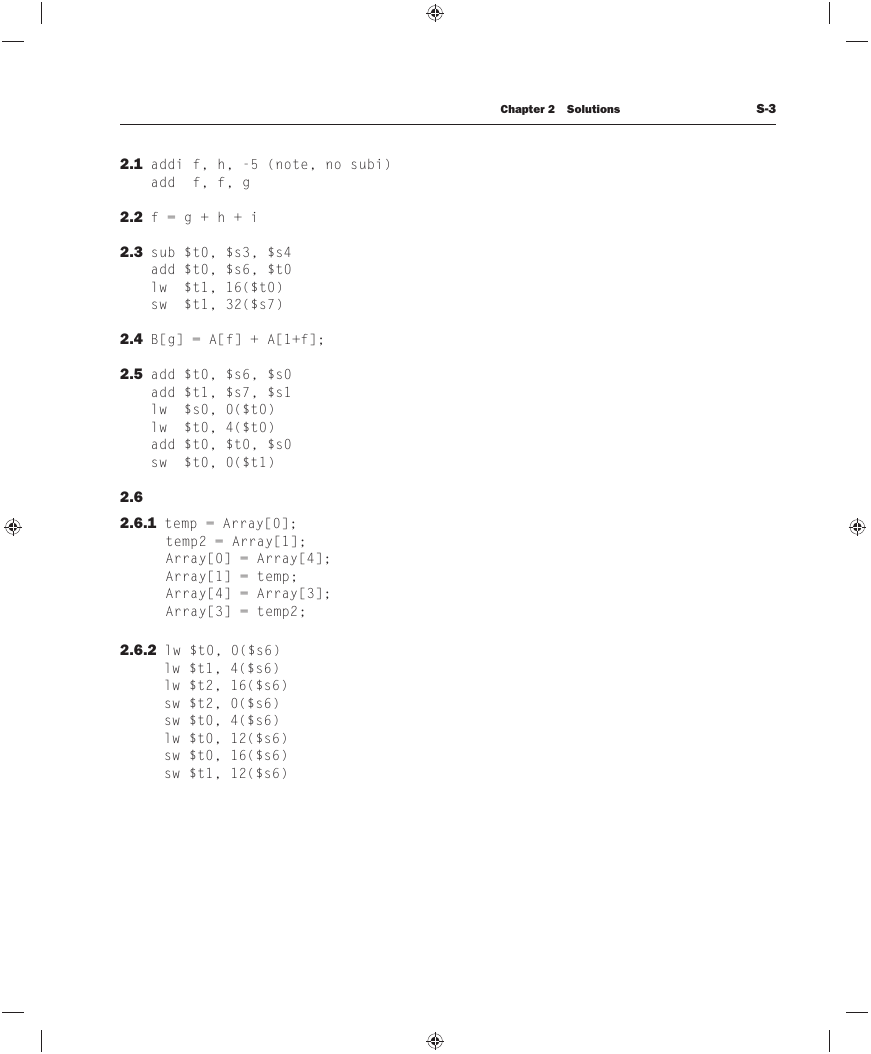
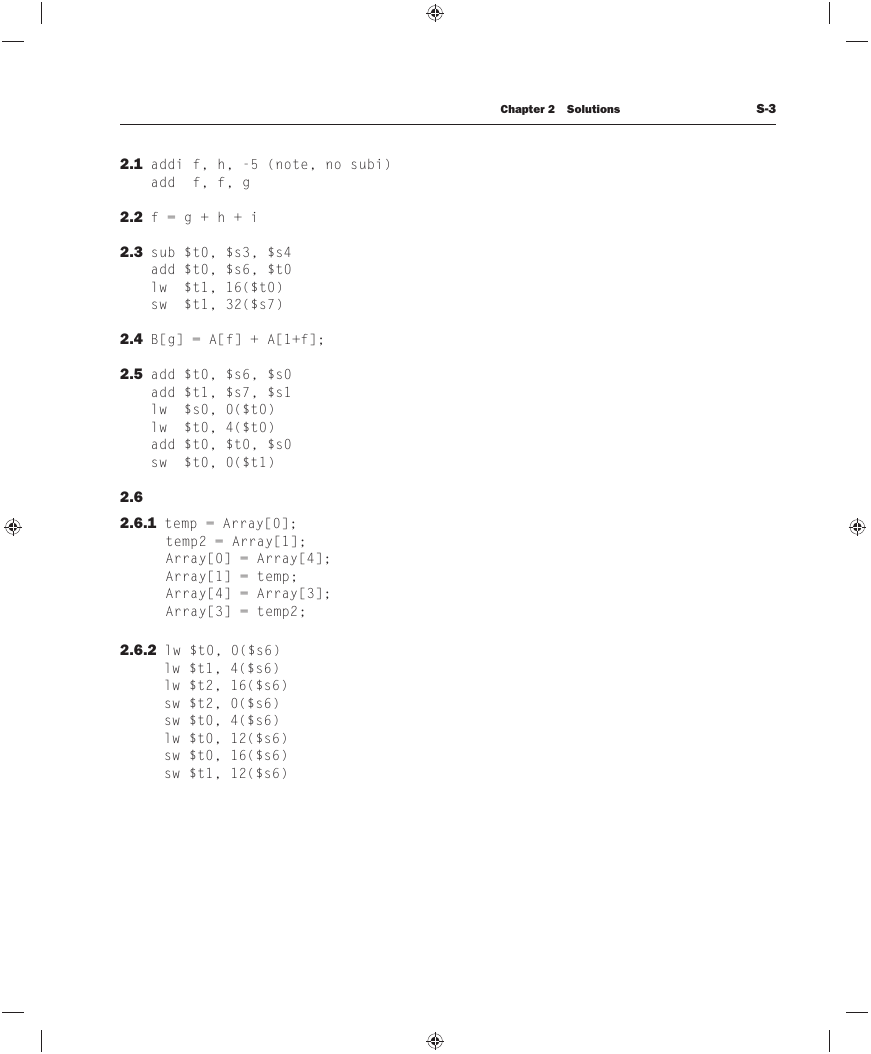
2.1 addi f, h, -5 (note, no subi)
add f, f, g
2.2 f = g + h + i
2.3 sub $t0, $s3, $s4
add $t0, $s6, $t0
lw $t1, 16($t0)
sw $t1, 32($s7)
2.4 B[g] = A[f] + A[1+f];
2.5 add $t0, $s6, $s0
add $t1, $s7, $s1
lw $s0, 0($t0)
lw $t0, 4($t0)
add $t0, $t0, $s0
sw $t0, 0($t1)
2.6
2.6.1 temp = Array[0];
temp2 = Array[1];
Array[0] = Array[4];
Array[1] = temp;
Array[4] = Array[3];
Array[3] = temp2;
2.6.2 lw $t0, 0($s6)
lw $t1, 4($s6)
lw $t2, 16($s6)
sw $t2, 0($s6)
sw $t0, 4($s6)
lw $t0, 12($s6)
sw $t0, 16($s6)
sw $t1, 12($s6)
�
S-4
Chapter 2 Solutions
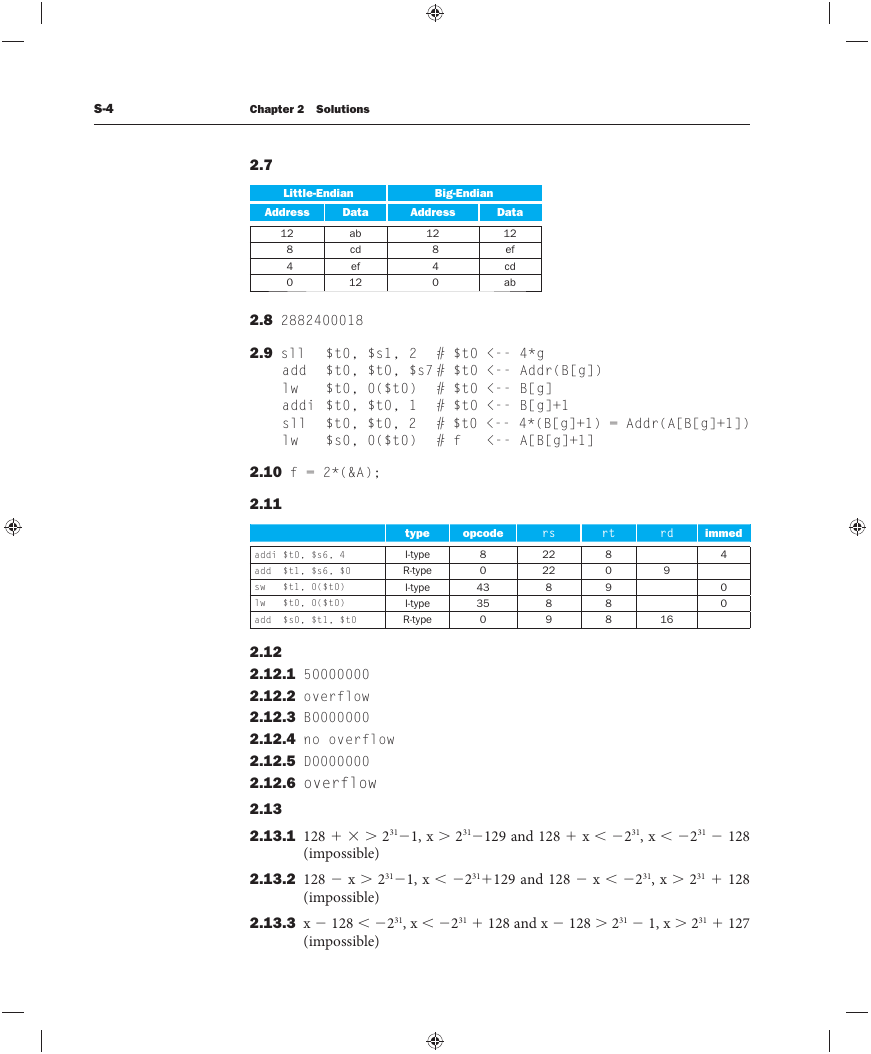
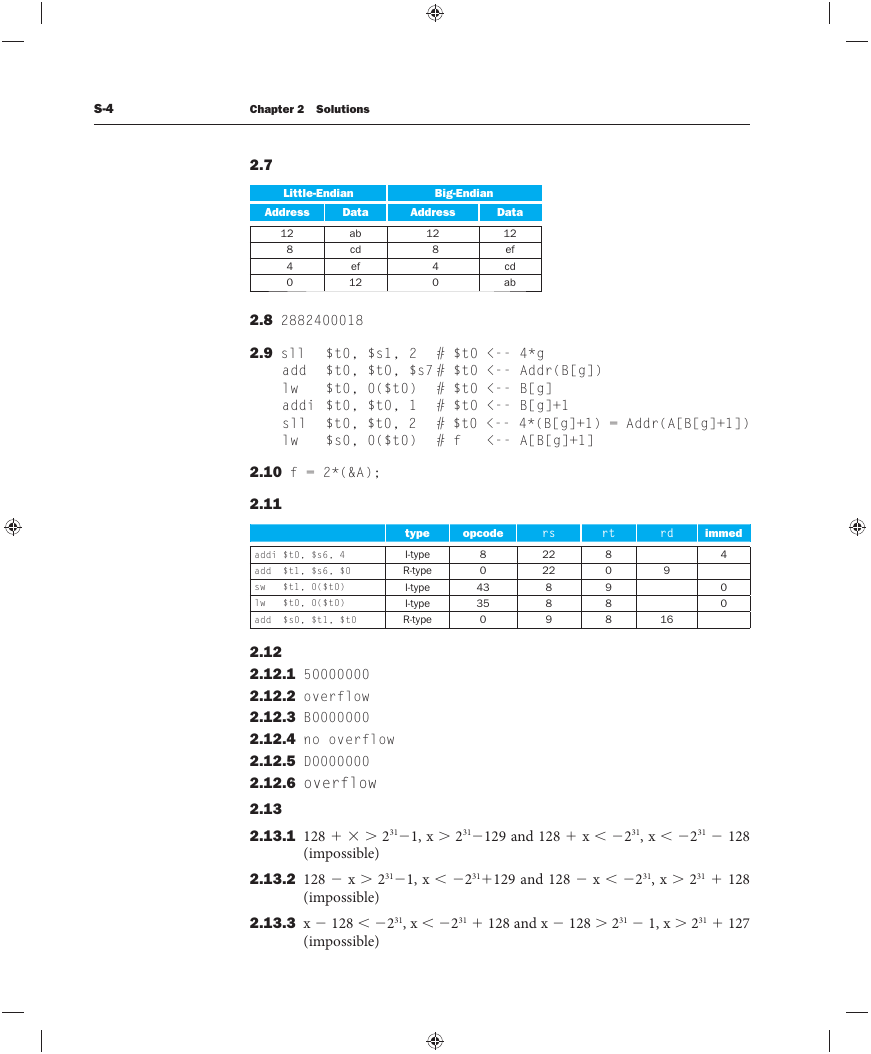
2.7
Little-Endian
Big-Endian
Address
Data
Address
Data
12
8
4
0
ab
cd
ef
12
12
8
4
0
12
ef
cd
ab
2.8 2882400018
2.9 sll $t0, $s1, 2 # $t0 <-- 4*g
add $t0, $t0, $s7 # $t0 <-- Addr(B[g])
lw
addi $t0, $t0, 1 # $t0 <-- B[g]+1
sll $t0, $t0, 2 # $t0 <-- 4*(B[g]+1) = Addr(A[B[g]+1])
lw
$t0, 0($t0) # $t0 <-- B[g]
$s0, 0($t0) # f <-- A[B[g]+1]
2.10 f = 2*(&A);
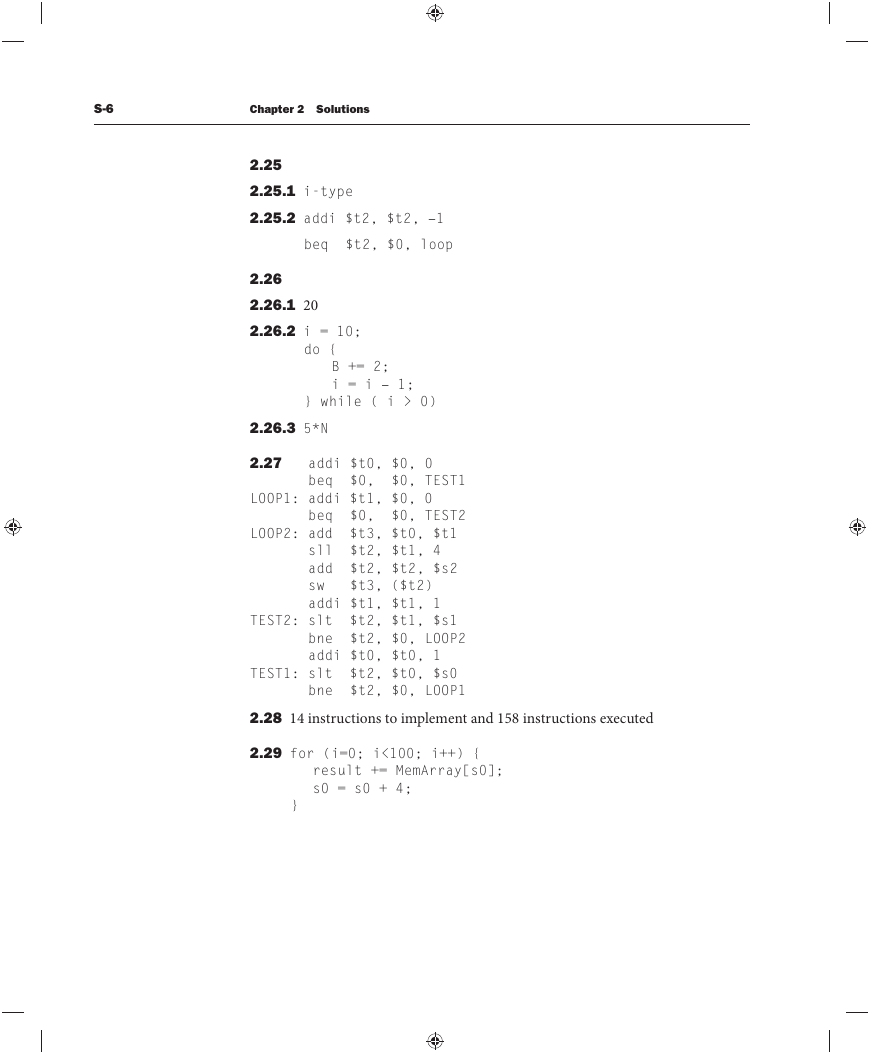
2.11
addi $t0, $s6, 4
add $t1, $s6, $0
sw $t1, 0($t0)
lw $t0, 0($t0)
add $s0, $t1, $t0
type
I-type
R-type
I-type
I-type
R-type
opcode
8
0
43
35
0
rs
22
22
8
8
9
rt
8
0
9
8
8
rd
9
16
immed
4
0
0
2.12
2.12.1 50000000
2.12.2 overflow
2.12.3 B0000000
2.12.4 no overflow
2.12.5 D0000000
2.12.6 overflow
2.13
2.13.1 128 ⫹ ⫻ ⬎ 231⫺1, x ⬎ 231⫺129 and 128 ⫹ x ⬍ ⫺231, x ⬍ ⫺231 ⫺ 128
(impossible)
2.13.2 128 ⫺ x ⬎ 231⫺1, x ⬍ ⫺231⫹129 and 128 ⫺ x ⬍ ⫺231, x ⬎ 231 ⫹ 128
(impossible)
2.13.3 x ⫺ 128 ⬍ ⫺231, x ⬍ ⫺231 ⫹ 128 and x ⫺ 128 ⬎ 231 ⫺ 1, x ⬎ 231 ⫹ 127
(impossible)
�
Chapter 2 Solutions
S-5
2.14 r-type, add $s0, $s0, $s0
2.15 i-type, 0xAD490020
2.16 r-type, sub $v1, $v1, $v0, 0x00621822
2.17 i-type, lw $v0, 4($at), 0x8C220004
2.18
2.18.1 opcode would be 8 bits, rs, rt, rd fi elds would be 7 bits each
2.18.2 opcode would be 8 bits, rs and rt fi elds would be 7 bits each
2.18.3 more registers → more bits per instruction → could increase code size
more registers → less register spills → less instructions
more instructions → more appropriate instruction → decrease code size
more instructions → larger opcodes → larger code size
2.19
2.19.1 0xBABEFEF8
2.19.2 0xAAAAAAA0
2.19.3 0x00005545
2.20 srl $t0, $t0, 11
sll $t0, $t0, 26
ori $t2, $0, 0x03ff
sll $t2, $t2, 16
ori $t2, $t2, 0xffff
and $t1, $t1, $t2
or $t1, $t1, $t0
2.21 nor $t1, $t2, $t2
2.22 lw $t3, 0($s1)
sll $t1, $t3, 4
2.23 $t2 = 3
2.24 jump: no, beq: no
�
S-6
Chapter 2 Solutions
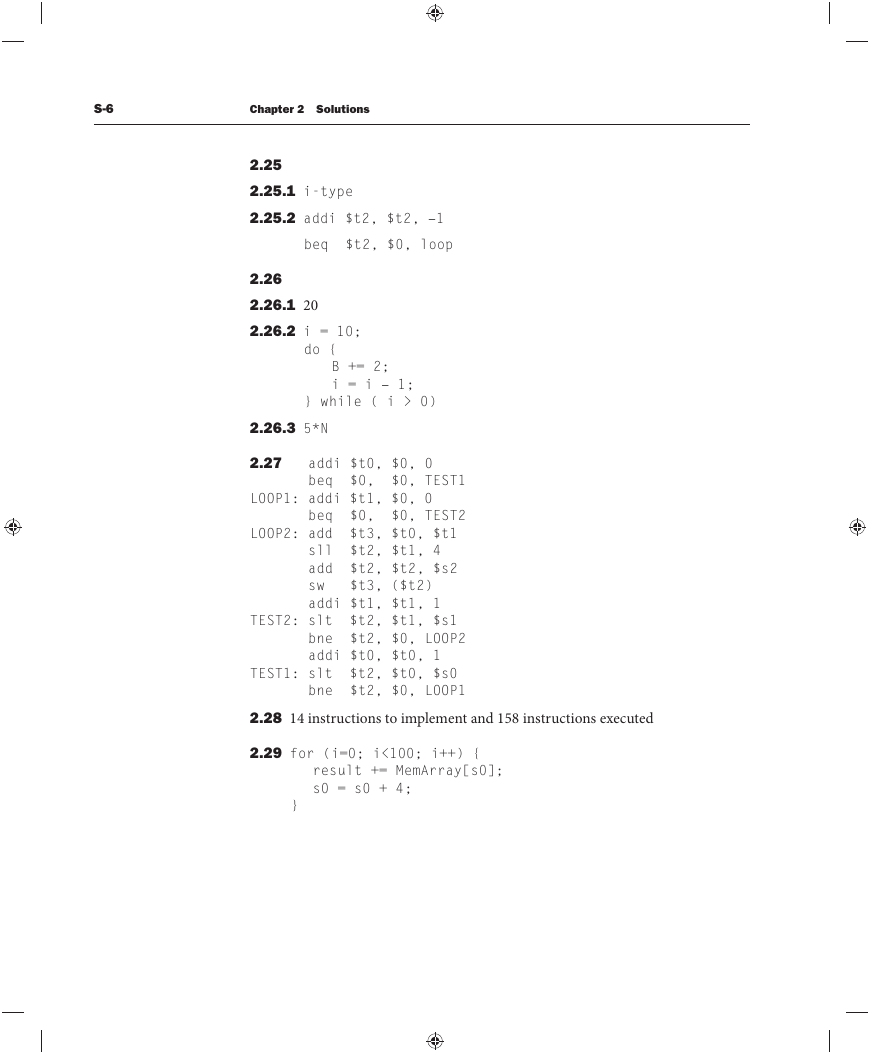
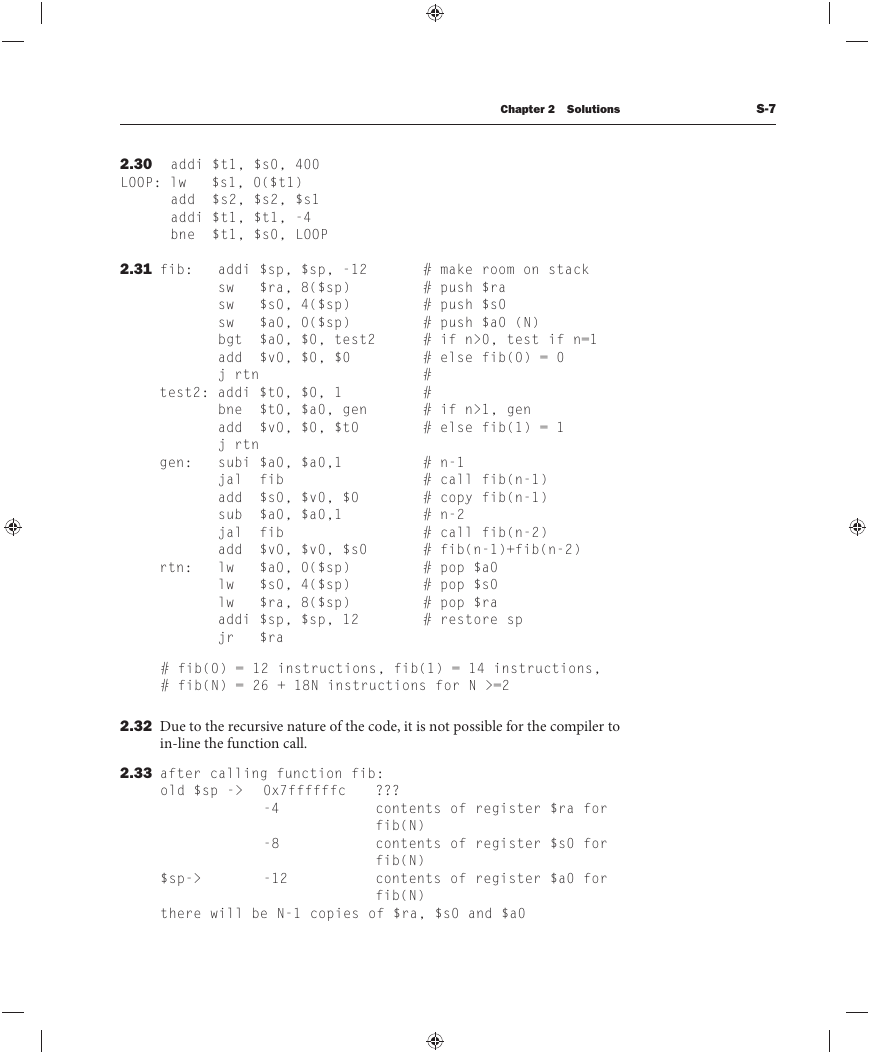
2.25
2.25.1 i-type
2.25.2 addi $t2, $t2, –1
beq $t2, $0, loop
2.26
2.26.1 20
2.26.2 i = 10;
do {
B += 2;
i = i – 1;
} while ( i > 0)
2.26.3 5*N
2.27
addi $t0, $0, 0
beq $0, $0, TEST1
LOOP1: addi $t1, $0, 0
beq $0, $0, TEST2
LOOP2: add $t3, $t0, $t1
sll $t2, $t1, 4
add $t2, $t2, $s2
sw $t3, ($t2)
addi $t1, $t1, 1
TEST2: slt $t2, $t1, $s1
bne $t2, $0, LOOP2
addi $t0, $t0, 1
TEST1: slt $t2, $t0, $s0
bne $t2, $0, LOOP1
2.28 14 instructions to implement and 158 instructions executed
2.29 for (i=0; i<100; i++) {
result += MemArray[s0];
s0 = s0 + 4;
}
�
Chapter 2 Solutions
S-7
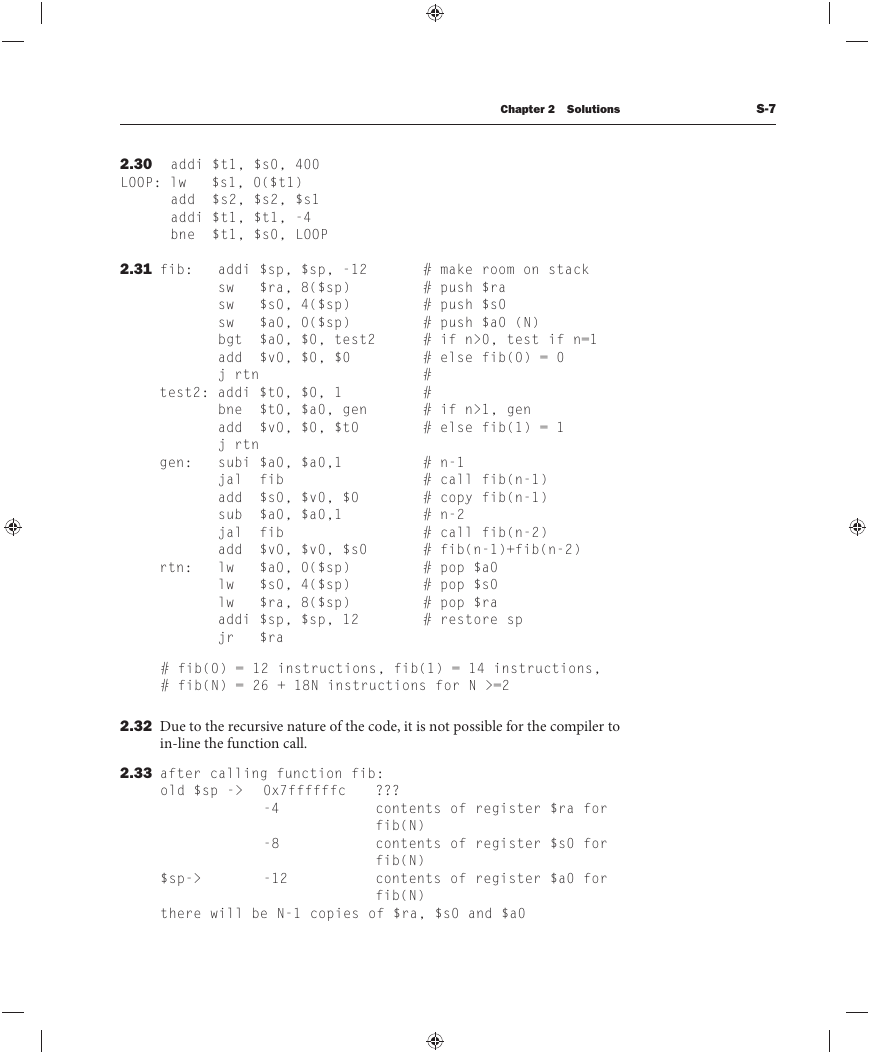
2.30 addi $t1, $s0, 400
LOOP: lw $s1, 0($t1)
add $s2, $s2, $s1
addi $t1, $t1, -4
bne $t1, $s0, LOOP
2.31 fib: addi $sp, $sp, -12
sw $ra, 8($sp)
sw $s0, 4($sp)
sw $a0, 0($sp)
bgt $a0, $0, test2
add $v0, $0, $0
j rtn
test2: addi $t0, $0, 1
gen:
rtn:
bne $t0, $a0, gen
add $v0, $0, $t0
j rtn
subi $a0, $a0,1
jal fib
add $s0, $v0, $0
sub $a0, $a0,1
jal fib
add $v0, $v0, $s0
lw $a0, 0($sp)
lw $s0, 4($sp)
lw $ra, 8($sp)
addi $sp, $sp, 12
jr $ra
# make room on stack
# push $ra
# push $s0
# push $a0 (N)
# if n>0, test if n=1
# else fib(0) = 0
#
#
# if n>1, gen
# else fib(1) = 1
# n-1
# call fib(n-1)
# copy fib(n-1)
# n-2
# call fib(n-2)
# fib(n-1)+fib(n-2)
# pop $a0
# pop $s0
# pop $ra
# restore sp
# fib(0) = 12 instructions, fib(1) = 14 instructions,
# fib(N) = 26 + 18N instructions for N >=2
2.32 Due to the recursive nature of the code, it is not possible for the compiler to
in-line the function call.
2.33 after calling function fib:
old $sp -> 0x7ffffffc
-4
-8
$sp->
-12
???
contents of register $ra for
fib(N)
contents of register $s0 for
fib(N)
contents of register $a0 for
fib(N)
there will be N-1 copies of $ra, $s0 and $a0
�
S-8
Chapter 2 Solutions
sw
sw
sw
move
move
jal
move
add
jal
lw
lw
lw
addi
jr
$ra,8($sp)
$s1,4($sp)
$s0,0($sp)
$s1,$a2
$s0,$a3
func
$a0,$v0
$a1,$s0,$s1
func
$ra,8($sp)
$s1,4($sp)
$s0,0($sp)
$sp,$sp,12
$ra
2.34 f: addi $sp,$sp,-12
2.35 We can use the tail-call optimization for the second call to func, but then
we must restore $ra, $s0, $s1, and $sp before that call. We save only one
instruction (jr $ra).
2.36 Register $ra is equal to the return address in the caller function, registers
$sp and $s3 have the same values they had when function f was called, and
register $t5 can have an arbitrary value. For register $t5, note that although
our function f does not modify it, function func is allowed to modify it so
we cannot assume anything about the of $t5 aft er function func has been
called.
2.37 MAIN: addi $sp, $sp, -4
sw $ra, ($sp)
add $t6, $0, 0x30 # ‘0’
add $t7, $0, 0x39 # ‘9’
add $s0, $0, $0
add $t0, $a0, $0
LOOP: lb $t1, ($t0)
slt $t2, $t1, $t6
bne $t2, $0, DONE
slt $t2, $t7, $t1
bne $t2, $0, DONE
sub $t1, $t1, $t6
beq $s0, $0, FIRST
mul $s0, $s0, 10
FIRST: add $s0, $s0, $t1
addi $t0, $t0, 1
j LOOP
�
Chapter 2 Solutions
S-9
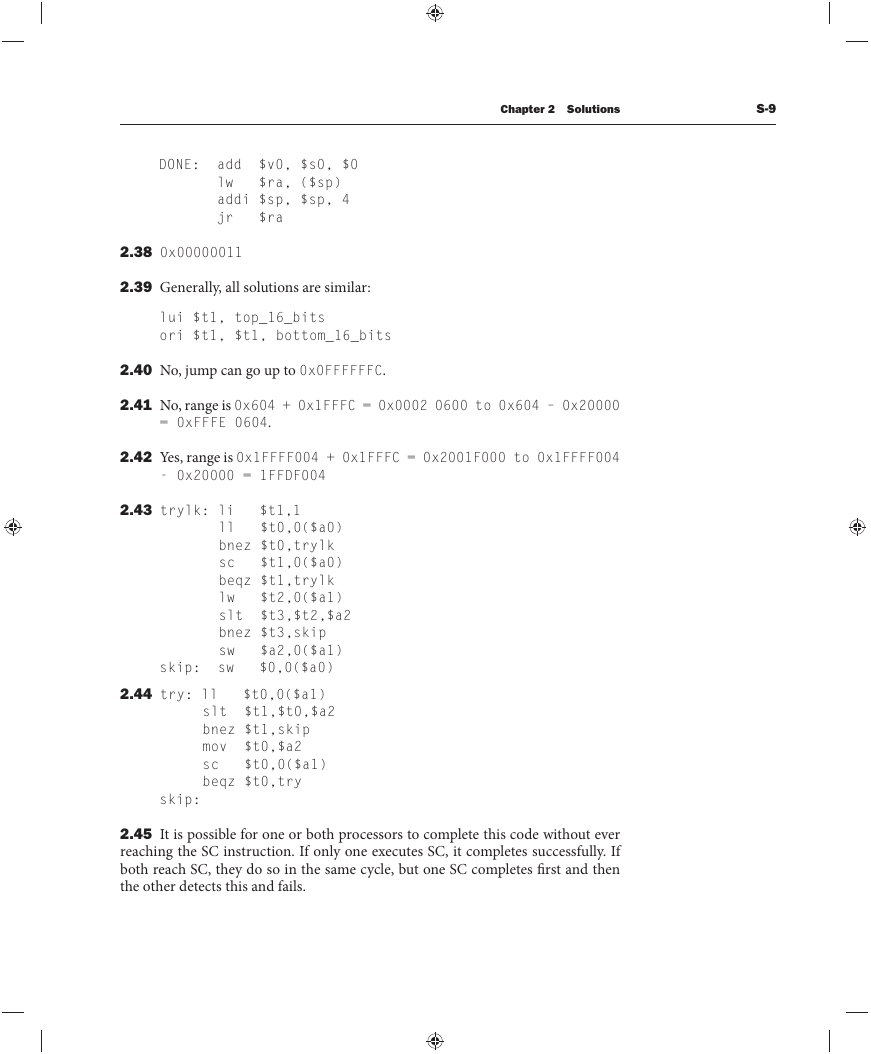
DONE: add $v0, $s0, $0
lw $ra, ($sp)
addi $sp, $sp, 4
jr $ra
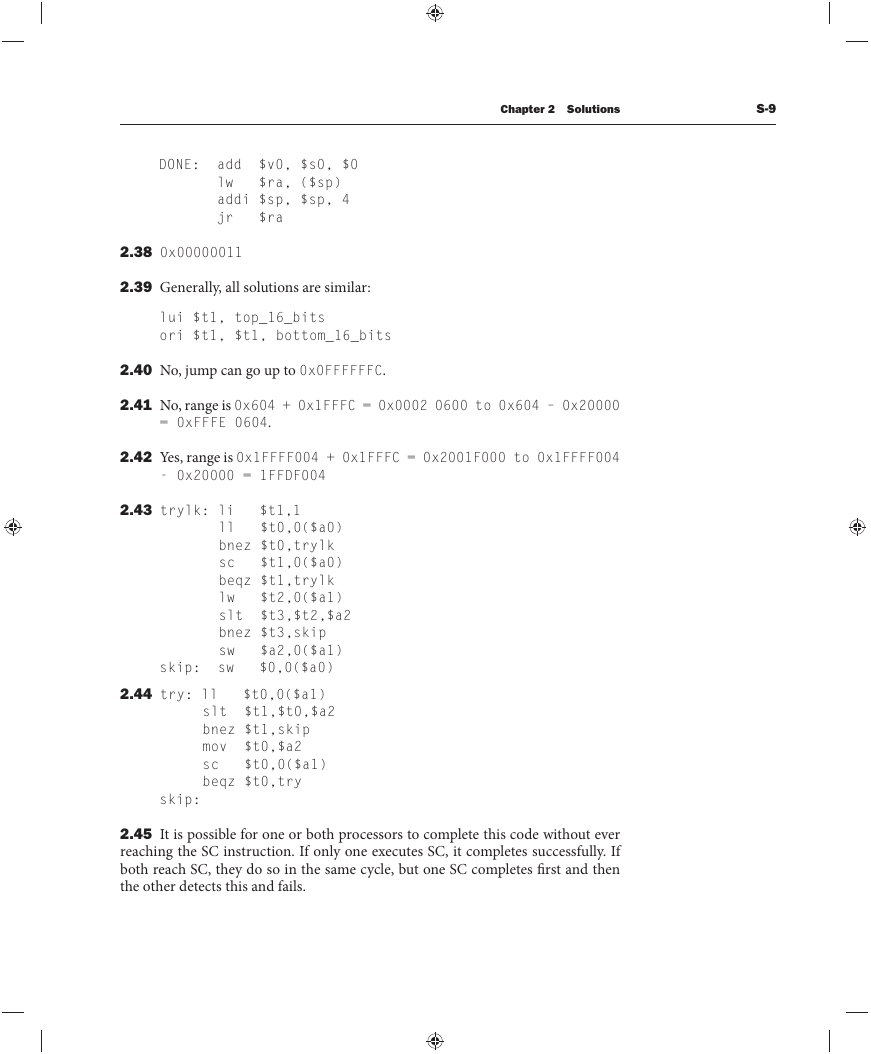
2.38 0x00000011
2.39 Generally, all solutions are similar:
lui $t1, top_16_bits
ori $t1, $t1, bottom_16_bits
2.40 No, jump can go up to 0x0FFFFFFC.
2.41 No, range is 0x604 + 0x1FFFC = 0x0002 0600 to 0x604 – 0x20000
= 0xFFFE 0604.
2.42 Yes, range is 0x1FFFF004 + 0x1FFFC = 0x2001F000 to 0x1FFFF004
- 0x20000 = 1FFDF004
2.43 trylk: li $t1,1
ll $t0,0($a0)
bnez $t0,trylk
sc $t1,0($a0)
beqz $t1,trylk
lw $t2,0($a1)
slt $t3,$t2,$a2
bnez $t3,skip
sw $a2,0($a1)
skip: sw $0,0($a0)
2.44 try: ll $t0,0($a1)
slt $t1,$t0,$a2
bnez $t1,skip
mov $t0,$a2
sc $t0,0($a1)
beqz $t0,try
skip:
2.45 It is possible for one or both processors to complete this code without ever
reaching the SC instruction. If only one executes SC, it completes successfully. If
both reach SC, they do so in the same cycle, but one SC completes fi rst and then
the other detects this and fails.
�




 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc