1 Terminology
Figure 1. Block diagram of a common cipher
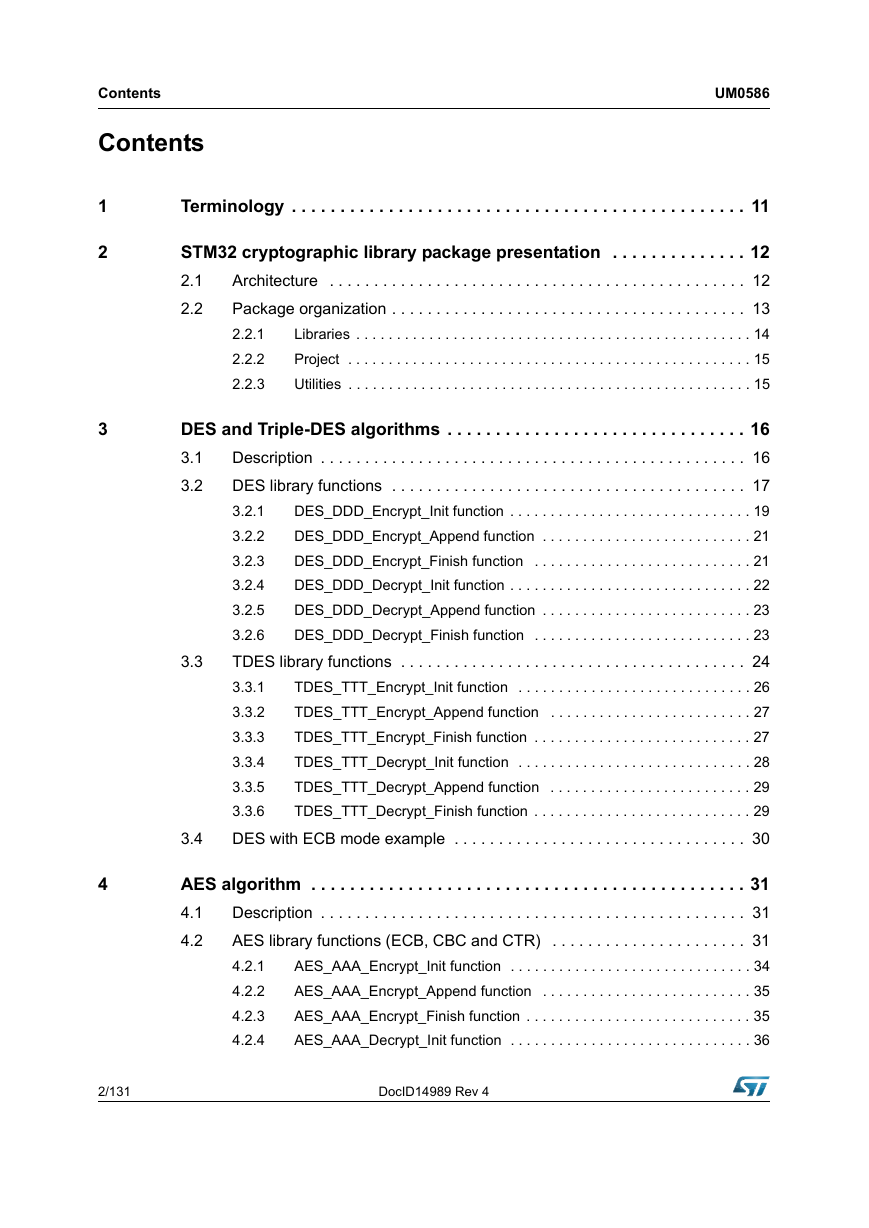
2 STM32 cryptographic library package presentation
2.1 Architecture
Figure 2. STM32 cryptographic library architecture
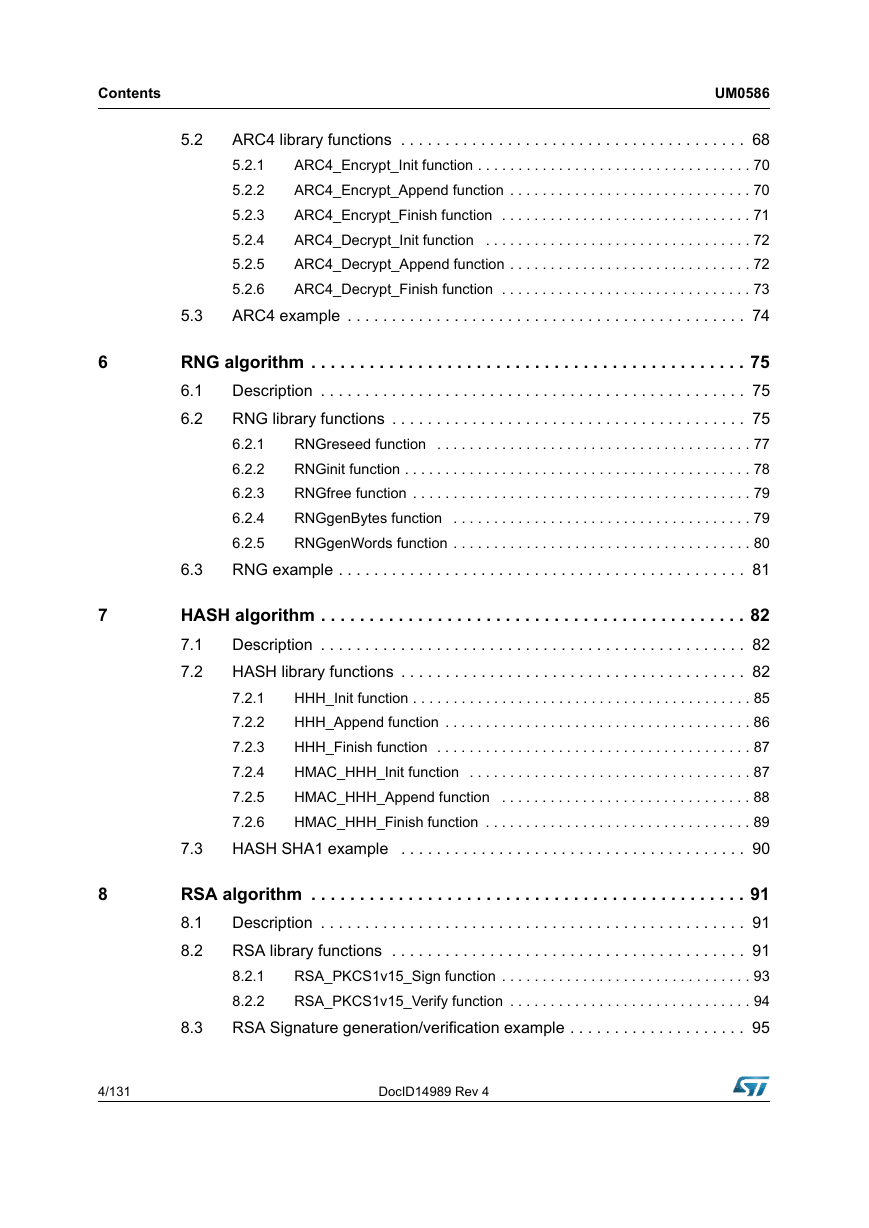
2.2 Package organization
Figure 3. STM32 cryptographic library package organization
2.2.1 Libraries
2.2.2 Project
Figure 4. Project folder organization
2.2.3 Utilities
3 DES and Triple-DES algorithms
3.1 Description
3.2 DES library functions
Table 1. DES algorithm functions (DDD = ECB or CBC)
Table 2. DES ECB algorithm functions
Figure 5. DES DDD(*) flowchart
3.2.1 DES_DDD_Encrypt_Init function
Table 3. DES_DDD_Encrypt_Init
Table 4. DESDDDctx_stt data structure
Table 5. SKflags_et mFlags
3.2.2 DES_DDD_Encrypt_Append function
Table 6. DES_DDD_Encrypt_Append
3.2.3 DES_DDD_Encrypt_Finish function
Table 7. DES_DDD_Encrypt_Finish
3.2.4 DES_DDD_Decrypt_Init function
Table 8. DES_DDD_Decrypt_Init
3.2.5 DES_DDD_Decrypt_Append function
Table 9. DES_DDD_Decrypt_Append
3.2.6 DES_DDD_Decrypt_Finish function
Table 10. DES_DDD_Decrypt_Finish
3.3 TDES library functions
Table 11. TDES algorithm functions (TTT = ECB or CBC)
Table 12. TDES ECB algorithm functions
Figure 6. TDES TTT(*) flowchart
3.3.1 TDES_TTT_Encrypt_Init function
Table 13. TDES_TTT_Encrypt_Init
Table 14. TDESTTTctx_stt data structure
3.3.2 TDES_TTT_Encrypt_Append function
Table 15. TDES_TTT_Encrypt_Append
3.3.3 TDES_TTT_Encrypt_Finish function
Table 16. TDES_TTT_Encrypt_Finish
3.3.4 TDES_TTT_Decrypt_Init function
Table 17. TDES_TTT_Decrypt_Init
3.3.5 TDES_TTT_Decrypt_Append function
Table 18. TDES_TTT_Decrypt_Append
3.3.6 TDES_TTT_Decrypt_Finish function
Table 19. TDES_TTT_Decrypt_Finish
3.4 DES with ECB mode example
4 AES algorithm
4.1 Description
4.2 AES library functions (ECB, CBC and CTR)
Table 20. AES algorithm functions (AAA = ECB, CBC or CTR)
Table 21. AES ECB algorithm functions
Figure 7. AES AAA(*) flowchart
4.2.1 AES_AAA_Encrypt_Init function
Table 22. AES_AAA_Encrypt_Init
Table 23. AESAAActx_stt data structure
4.2.2 AES_AAA_Encrypt_Append function
Table 24. AES_AAA_Encrypt_Append
4.2.3 AES_AAA_Encrypt_Finish function
Table 25. AES_AAA_Encrypt_Finish
4.2.4 AES_AAA_Decrypt_Init function
Table 26. AES_AAA_Decrypt_Init
4.2.5 AES_AAA_Decrypt_Append function
Table 27. AES_AAA_Decrypt_Append
4.2.6 AES_AAA_Decrypt_Finish function
Table 28. AES_AAA_Decrypt_Finish
4.3 AES GCM library functions
Table 29. AES GCM algorithm functions
Figure 8. AES GCM flowchart
4.3.1 AES_GCM_Encrypt_Init function
Table 30. AES_GCM_Encrypt_Init
Table 31. AESGCMctx_stt data structure
4.3.2 AES_GCM_Header_Append function
Table 32. AES_GCM_Header_Append
4.3.3 AES_GCM_Encrypt_Append function
Table 33. AES_GCM_Encrypt_Append
4.3.4 AES_GCM_Encrypt_Finish function
Table 34. AES_GCM_Encrypt_Finish
4.3.5 AES_GCM_Decrypt_Init function
Table 35. AES_GCM_Decrypt_Init
4.3.6 AES_GCM_Decrypt_Append function
Table 36. AES_GCM_Decrypt_Append
4.3.7 AES_GCM_Decrypt_Finish function
Table 37. AES_GCM_Decrypt_Finish
4.4 AES KeyWrap library functions
Table 38. AES KeyWrap algorithm functions
Figure 9. AES_KeyWrap flowchart
4.4.1 AES_KeyWrap_Encrypt_Init function
Table 39. AES_KeyWrap_Encrypt_Init
4.4.2 AES_KeyWrap_Encrypt_Append function
Table 40. AES_KeyWrap_Encrypt_Append
4.4.3 AES_KeyWrap_Encrypt_Finish function
Table 41. AES_KeyWrap_Encrypt_Finish
4.4.4 AES_KeyWrap_Decrypt_Init function
Table 42. AES_KeyWrap_Decrypt_Init
4.4.5 AES_KeyWrap_Decrypt_Append function
Table 43. AES_KeyWrap_Decrypt_Append
4.4.6 AES_KeyWrap_Decrypt_Finish function
Table 44. AES_KeyWrap_Decrypt_Finish
4.5 AES CMAC library functions
Table 45. AES CMAC algorithm functions
Figure 10. AES_CMAC flowchart
4.5.1 AES_CMAC_Encrypt_Init function
Table 46. AES_CMAC_Encrypt_Init
Table 47. AESCMACctx_stt data structure
4.5.2 AES_CMAC_Encrypt_Append function
Table 48. AES_CMAC_Encrypt_Append
4.5.3 AES_CMAC_Encrypt_Finish function
Table 49. AES_CMAC_Encrypt_Finish
4.5.4 AES_CMAC_Decrypt_Init function
Table 50. AES_CMAC_Decrypt_Init
4.5.5 AES_CMAC_Decrypt_Append function
Table 51. AES_CMAC_Decrypt_Append
4.5.6 AES_CMAC_Decrypt_Finish function
Table 52. AES_CMAC_Decrypt_Finish
4.6 AES CCM library functions
Table 53. AES CCM algorithm functions
Figure 11. AES_CCM flowchart
4.6.1 AES_CCM_Encrypt_Init function
Table 54. AES_CCM_Encrypt_Init
Table 55. AESCCMctx_stt data structure
4.6.2 AES_CCM_Header_Append function
Table 56. AES_CCM_Header_Append
4.6.3 AES_CCM_Encrypt_Append function
Table 57. AES_CCM_Encrypt_Append
4.6.4 AES_CCM_Encrypt_Finish function
Table 58. AES_CCM_Encrypt_Finish
4.6.5 AES_CCM_Decrypt_Init function
Table 59. AES_CCM_Decrypt_Init
4.6.6 AES_CCM_Decrypt_Append function
Table 60. AES_CCM_Decrypt_Append
4.6.7 AES_CCM_Decrypt_Finish function
Table 61. AES_CCM_Decrypt_Finish
4.7 AES CBC enciphering and deciphering example
5 ARC4 algorithm
5.1 Description
5.2 ARC4 library functions
Table 62. ARC4 algorithm functions
Figure 12. ARC4 flowchart
5.2.1 ARC4_Encrypt_Init function
Table 63. ARC4_Encrypt_Init
5.2.2 ARC4_Encrypt_Append function
Table 64. ARC4_Encrypt_Append
Table 65. ARC4ctx_stt data structure
5.2.3 ARC4_Encrypt_Finish function
Table 66. ARC4_Encrypt_Finish
5.2.4 ARC4_Decrypt_Init function
Table 67. ARC4_Decrypt_Init
5.2.5 ARC4_Decrypt_Append function
Table 68. ARC4_Decrypt_Append
5.2.6 ARC4_Decrypt_Finish function
Table 69. ARC4_Decrypt_Finish
5.3 ARC4 example
6 RNG algorithm
6.1 Description
6.2 RNG library functions
Table 70. RNG algorithm functions
Figure 13. RNG flowchart
6.2.1 RNGreseed function
Table 71. RNGreseed
Table 72. RNGreInput_stt struct reference
Table 73. RNGstate_stt struct reference
6.2.2 RNGinit function
Table 74. RNGinit
Table 75. RNGstate_stt struct reference
6.2.3 RNGfree function
Table 76. RNGfree
6.2.4 RNGgenBytes function
Table 77. RNGgenBytes
6.2.5 RNGgenWords function
Table 78. RNGgenWords
6.3 RNG example
7 HASH algorithm
7.1 Description
7.2 HASH library functions
Table 79. HASH algorithm functions (HHH = MD5, SHA1, SHA224 or SHA256)
Table 80. HASH SHA1 algorithm functions
Figure 14. Hash HHH flowchart
7.2.1 HHH_Init function
Table 81. HHH_Init
Table 82. HASHctx_stt struct reference
Table 83. HashFlags_et mFlags
7.2.2 HHH_Append function
Table 84. HHH_Append
7.2.3 HHH_Finish function
Table 85. HHH_Finish
7.2.4 HMAC_HHH_Init function
Table 86. HMAC_HHH_Init
Table 87. HMACctx_stt struct reference
7.2.5 HMAC_HHH_Append function
Table 88. HMAC_HHH_Append
7.2.6 HMAC_HHH_Finish function
Table 89. HMAC_HHH_Finish
7.3 HASH SHA1 example
8 RSA algorithm
8.1 Description
8.2 RSA library functions
Table 90. RSA algorithm functions
Figure 15. RSA flowchart
8.2.1 RSA_PKCS1v15_Sign function
Table 91. RSA_PKCS1v15_Sign function
Table 92. RSAprivKey_stt data structure
Table 93. membuf_stt data structure
8.2.2 RSA_PKCS1v15_Verify function
Table 94. RSA_PKCS1v15_Verify function
Table 95. RSApubKey_stt data structure
8.3 RSA Signature generation/verification example
9 ECC algorithm
9.1 Description
9.2 ECC library functions
Table 96. ECC algorithm functions
Figure 16. ECC Sign flowchart
Figure 17. ECC Verify flowchart
Figure 18. ECC key generator flowchart
9.2.1 ECCinitEC function
Table 97. ECCinitEC function
Table 98. EC_stt data structure
9.2.2 ECCfreeEC function
Table 99. ECCfreeEC function
9.2.3 ECCinitPoint function
Table 100. ECCinitPoint function
Table 101. ECpoint_stt data structure
9.2.4 ECCfreePoint function
Table 102. ECCfreePoint function
9.2.5 ECCsetPointCoordinate function
Table 103. ECCsetPointCoordinate function
9.2.6 ECCgetPointCoordinate function
Table 104. ECCgetPointCoordinate function
9.2.7 ECCgetPointFlag function
Table 105. ECCgetPointFlag function
9.2.8 ECCsetPointFlag function
Table 106. ECCsetPointFlag function
9.2.9 ECCcopyPoint function
Table 107. ECCcopyPoint function
9.2.10 ECCinitPrivKey function
Table 108. ECCinitPrivKey function
Table 109. ECCprivKey_stt data structure
9.2.11 ECCfreePrivKey function
Table 110. ECCfreePrivKey function
9.2.12 ECCsetPrivKeyValue function
Table 111. ECCsetPrivKeyValue function
9.2.13 ECCgetPrivKeyValue function
Table 112. ECCgetPrivKeyValue function
9.2.14 ECCscalarMul function
Table 113. ECCscalarMul function
9.2.15 ECCsetPointGenerator function
Table 114. ECCsetPointGenerator function
9.2.16 ECDSAinitSign function
Table 115. ECDSAinitSign function
9.2.17 ECDSAfreeSign function
Table 116. ECDSAfreeSign function
9.2.18 ECDSAsetSignature function
Table 117. ECDSAsetSignature function
9.2.19 ECDSAgetSignature function
Table 118. ECDSAgetSignature function
9.2.20 ECDSAverify function
Table 119. ECDSAverify function
9.2.21 ECCvalidatePubKey function
Table 120. ECCvalidatePubKey function
9.2.22 ECCkeyGen function
Table 121. ECCkeyGen function
9.2.23 ECDSAsign function
Table 122. ECDSAsign function
9.3 ECC example
10 STM32 encryption library settings
10.1 Configuration parameters
Table 123. Library build options
10.2 STM32_CryptoLibraryVersion
Table 124. STM32_CryptoLibraryVersion
11 Cryptographic library performance and memory requirements
11.1 Symmetric key algorithms performance results
11.1.1 Software optimized for speed
Table 125. Performance of symmetric key encryption algo. optimized for speed
Table 126. Code size required by symmetric key encryption algo
11.1.2 Hardware enhanced
Table 127. Symmetric key encrypt. algo. performance with HW acceleration
Table 128. Code size for symmetric key encryption algo. with HW acceleration
11.2 Authenticated encryption algorithms performance results
11.2.1 Software optimized for speed
Table 129. Clock cycles for authenticated encryption algorithms optimized for speed
Table 130. Code size for authenticated encryption algorithms optimized for speed
11.2.2 Hardware enhanced
Table 131. Clock cycles for authenticated encryption algorithms & HW acceleration
Table 132. Code size for authenticated encryption algorithm & HW acceleration
11.3 AES key wrap results
11.3.1 Software optimized for speed
Table 133. AES Key Wrap/Unwrap in software
Table 134. Code size for AES key wrap/unwrap in software
11.3.2 Hardware enhanced
Table 135. AES key wrap/unwrap with HW acceleration
Table 136. Code size for AES key wrap/unwrap with HW acceleration
11.4 HASH and HMAC algorithm results
11.4.1 Software optimized for speed
Table 137. Clock cycles for HASH and HMAC algorithms optimized for speed
Table 138. Clock cycles for HASH and HMAC algorithms with SW acceleration
11.4.2 Hardware enhanced
Table 139. Clock cycles required by HASH/HMAC algorithms with HW acceleration
Table 140. Code size required by HASH/HMAC algorithms
11.5 RSA results
Table 141. RSA performance with optimization for speed
Table 142. Code size required by RSA algorithms
11.6 ECC results
Table 143. Number of cycles for ECC operations with for speed optimization
Table 144. Code size for ECC operations with speed optimization
12 Revision history
Table 145. Document revision history


 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc