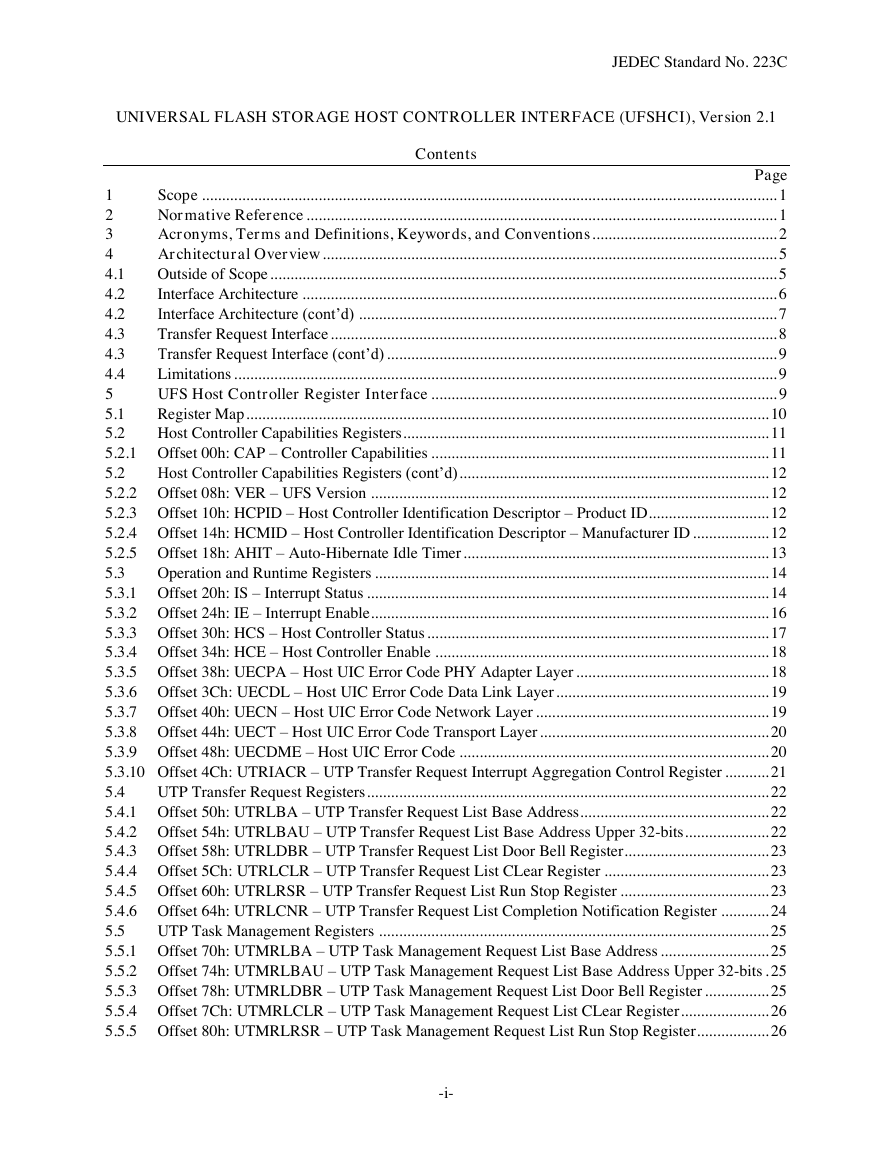
1 Scope
2 Normative Reference
3 Acronyms, Terms and Definitions, Keywords, and Conventions
4 Architectural Overview
4.1 Outside of Scope
4.2 Interface Architecture
4.2 Interface Architecture (cont’d)
4.3 Transfer Request Interface
4.3 Transfer Request Interface (cont’d)
4.4 Limitations
5 UFS Host Controller Register Interface
5.1 Register Map
5.2 Host Controller Capabilities Registers
5.2.1 Offset 00h: CAP – Controller Capabilities
5.2 Host Controller Capabilities Registers (cont’d)
5.2.2 Offset 08h: VER – UFS Version
5.2.3 Offset 10h: HCPID – Host Controller Identification Descriptor – Product ID
5.2.4 Offset 14h: HCMID – Host Controller Identification Descriptor – Manufacturer ID
5.2.5 Offset 18h: AHIT – Auto-Hibernate Idle Timer
5.3 Operation and Runtime Registers
5.3.1 Offset 20h: IS – Interrupt Status
5.3 Operation and Runtime Registers (cont’d)
5.3.2 Offset 24h: IE – Interrupt Enable
5.3 Operation and Runtime Registers (cont’d)
5.3.3 Offset 30h: HCS – Host Controller Status
5.3 Operation and Runtime Registers (cont’d)
5.3.4 Offset 34h: HCE – Host Controller Enable
5.3.5 Offset 38h: UECPA – Host UIC Error Code PHY Adapter Layer
5.3 Operation and Runtime Registers (cont’d)
5.3.6 Offset 3Ch: UECDL – Host UIC Error Code Data Link Layer
5.3.7 Offset 40h: UECN – Host UIC Error Code Network Layer
5.3 Operation and Runtime Registers (cont’d)
5.3.8 Offset 44h: UECT – Host UIC Error Code Transport Layer
5.3.9 Offset 48h: UECDME – Host UIC Error Code
5.3 Operation and Runtime Registers (cont’d)
5.3.10 Offset 4Ch: UTRIACR – UTP Transfer Request Interrupt Aggregation Control Register
5.3 Operation and Runtime Registers (cont’d)
5.3.10 Offset 4Ch: UTRIACR – UTP Transfer Request Interrupt Aggregation Control Register (cont’d)
5.4 UTP Transfer Request Registers
5.4.1 Offset 50h: UTRLBA – UTP Transfer Request List Base Address
5.4.2 Offset 54h: UTRLBAU – UTP Transfer Request List Base Address Upper 32-bits
5.4.3 Offset 58h: UTRLDBR – UTP Transfer Request List Door Bell Register
5.4.4 Offset 5Ch: UTRLCLR – UTP Transfer Request List CLear Register
5.4.5 Offset 60h: UTRLRSR – UTP Transfer Request List Run Stop Register
5.4.6 Offset 64h: UTRLCNR – UTP Transfer Request List Completion Notification Register
5.5 UTP Task Management Registers
5.5.1 Offset 70h: UTMRLBA – UTP Task Management Request List Base Address
5.5.2 Offset 74h: UTMRLBAU – UTP Task Management Request List Base Address Upper 32-bits
5.5.3 Offset 78h: UTMRLDBR – UTP Task Management Request List Door Bell Register
5.5.4 Offset 7Ch: UTMRLCLR – UTP Task Management Request List CLear Register
5.5.5 Offset 80h: UTMRLRSR – UTP Task Management Request List Run Stop Register
5.6 UIC Command Registers
5.6.1 Offset 90h: UICCMD – UIC Command
5.6.2 Offset 94h: UICCMDARG1 – UIC Command Argument 1
5.6.3 Offset 98h: UICCMDARG2 – UIC Command Argument 2
5.6.4 Offset 9Ch: UICCMDARG3 – UIC Command Argument 3
5.6.5 Attributes for Local L2 Timers
5.7 Vendor Specific Registers
5.7.1 Offset C0h to FFh: VS – Vendor Specific
5.8 Crypto Registers
5.8.1 Offset 100h: CCAP – Crypto Capability
5.8.2 x-CRYPTOCAP – Crypto Capability X
5.8.3 x-CRYPTOCFG – Crypto Configuration X
6 Data structures
6.1 UTP Transfer Request List
6.1.1 UTP Transfer Request Descriptor
6.1.2 UTP Command Descriptor
6.2 UTP Task Management Request List
6.2.1 UTP Task Management Request Descriptor
6.3 Key Organization for Cryptographic Algorithms
6.3.1 AES-XTS
6.3.2 Bitlocker-AES-CBC
6.3.3 AES-ECB
6.3.4 ESSIV-AES-CBC
7 Theory of Operation
7.1 Host Controller Configuration and Control
7.1.1 Host Controller Initialization
7.1.2 Configuration and control
7.1.3 CRYPTOCFG Configuration Procedure
7.2 Data Transfer Operation
7.2.1 Basic Steps when Building a UTP Transfer Request
7.2.2 UPIU Processing
7.2.2.1 Outbound UPIUs generated by Software
7.2.2.2 Outbound UPIU generated by Host Controller/UTP Engine
7.2.2.3 Inbound UPIUs interpreted by Software
7.2.2.4 Inbound UPIUs interpreted by Host Controller/UTP Engine
7.2.3 Processing UTP Transfer Request Completion
7.3 Task Management Function
7.3.1 Basic Steps when Building a UTP Task Management Request
7.3.2 Processing UTP Task Management Completion
7.4 UIC Power Mode Change
7.5 UFSHCI Internal Rules
7.5.1 Command Processing Order
7.5.2 RTT Processing Rules
7.5.3 Data Unit Processing Order for Cryptographic operations
8 error reporting and handling
8.1 Error Types
8.1.1 System Bus Error
8.1.2 UIC Error
8.1.3 UIC Command Error
8.1.4 UTP Error
8.1.5 Host controller Fatal Error
8.1.6 Device Error
8.1.7 Hibernate Enter/Exit Error
8.2 Error Handling
8.2.1 System Bus Error Handling
8.2.2 UIC Error Handling
8.2.3 UIC Command Error Handling
8.2.4 UTP Error Handling
8.2.4.1 UTP Transfer Request Error Handling
8.2.4.2 UTP Task Management Request Error Handling
8.2.5 Host Controller Error Handling
8.2.6 Device Error Handling
8.2.7 Hibernate Enter/Exit Error Handling
9 Encryption Engine Details (Informative)
9.1 AES-XTS
9.1.1 Overview
9.1.2 Data Unit Size
9.1 AES-XTS (cont’d)
9.1.3 Tweak
9.2 Bitlocker AES-CBC
9.2.1 Background
9.2.2 Overview
9.2.3 Sector (Data Unit) Size S
9.2.4 Sector Offset O
9.2.5 Sector Initialization Vector (IV)
9.2.6 Encryption / Decryption
9.3 AES-ECB
9.3.1 Overview
9.4 ESSIV-AES-CBC
9.4.1 Background
9.4.2 Data Unit Size
9.4.3 Sector Number (SN)
9.4.4 Initialization Vector (IV)
9.4.5 Encryption / Decryption
Standard Improvement Form JEDEC JESD223C




 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc