�
NETWORK SECURITY
ESSENTIALS:
APPLICATIONS AND STANDARDS
FOURTH EDITION
William Stallings
Boston Columbus
Prentice Hall
Indianapolis New York San Francisco Upper Saddle River
Amsterdam Cape Town Dubai London Madrid Milan Munich Paris Montreal Toronto
Delhi Mexico City Sao Paulo Sydney Hong Kong Seoul Singapore Taipei Tokyo
Vice President and Editorial Director, ECS:
Marcia J. Horton
Editor in Chief, Computer Science: Michael
Hirsch
Executive Editor: Tracy Dunkelberger
Assistant Editor: Melinda Haggerty
Editorial Assistant: Allison Michael
Managing Editor: Scott Disanno
Production Manager: Wanda Rockwell
Art Director: Jayne Conte
Cover Designer: Bruce Kenselaar
Cover Art: Shutterstock
Art Editor: Greg Dulles
Copyright © 2011 Pearson Education, Inc., publishing as [Prentice Hall, 1 Lake Street, Upper Saddle
River, NJ 07458].All rights reserved. Manufactured in the United States of America.This publication is protected
by Copyright, and permission should be obtained from the publisher prior to any prohibited reproduction, storage
in a retrieval system, or transmission in any form or by any means, electronic, mechanical, photocopying,
recording, or likewise.To obtain permission(s) to use material from this work, please submit a written request to
Pearson Education, Inc., Permissions Department, [imprint permissions address].
Many of the designations by manufacturers and seller to distinguish their products are claimed as trademarks.
Where those designations appear in this book, and the publisher was aware of a trademark claim, the
designations have been printed in initial caps or all caps.
Library of Congress Cataloging-in-Publication Data
10 9 8 7 6 5 4 3 2 1
ISBN 10:
0-13-610805-9
ISBN 13: 978-0-13-610805-4
�
To Antigone
never dull
never boring
always a Sage
�
This page intentionally left blank
�
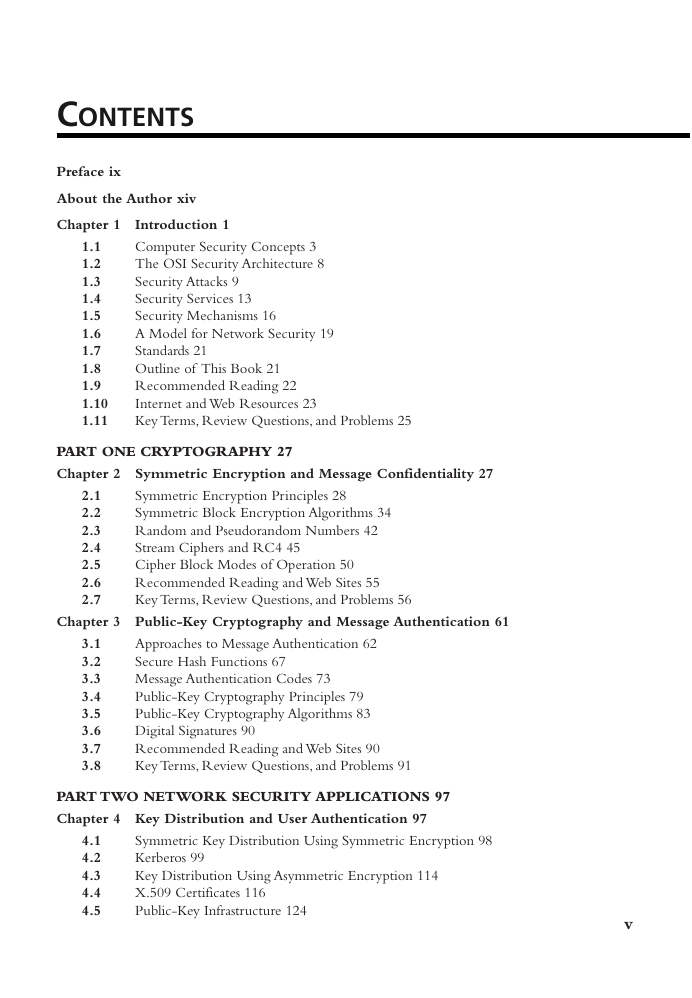
CONTENTS
Preface ix
About the Author xiv
Chapter 1 Introduction 1
1.1
1.2
1.3
1.4
1.5
1.6
1.7
1.8
1.9
1.10
1.11
Computer Security Concepts 3
The OSI Security Architecture 8
Security Attacks 9
Security Services 13
Security Mechanisms 16
A Model for Network Security 19
Standards 21
Outline of This Book 21
Recommended Reading 22
Internet and Web Resources 23
Key Terms, Review Questions, and Problems 25
PART ONE CRYPTOGRAPHY 27
Chapter 2 Symmetric Encryption and Message Confidentiality 27
2.1
2.2
2.3
2.4
2.5
2.6
2.7
Symmetric Encryption Principles 28
Symmetric Block Encryption Algorithms 34
Random and Pseudorandom Numbers 42
Stream Ciphers and RC4 45
Cipher Block Modes of Operation 50
Recommended Reading and Web Sites 55
Key Terms, Review Questions, and Problems 56
Chapter 3 Public-Key Cryptography and Message Authentication 61
3.1
3.2
3.3
3.4
3.5
3.6
3.7
3.8
Approaches to Message Authentication 62
Secure Hash Functions 67
Message Authentication Codes 73
Public-Key Cryptography Principles 79
Public-Key Cryptography Algorithms 83
Digital Signatures 90
Recommended Reading and Web Sites 90
Key Terms, Review Questions, and Problems 91
PART TWO NETWORK SECURITY APPLICATIONS 97
Chapter 4 Key Distribution and User Authentication 97
4.1
4.2
4.3
4.4
4.5
Symmetric Key Distribution Using Symmetric Encryption 98
Kerberos 99
Key Distribution Using Asymmetric Encryption 114
X.509 Certificates 116
Public-Key Infrastructure 124
v
�
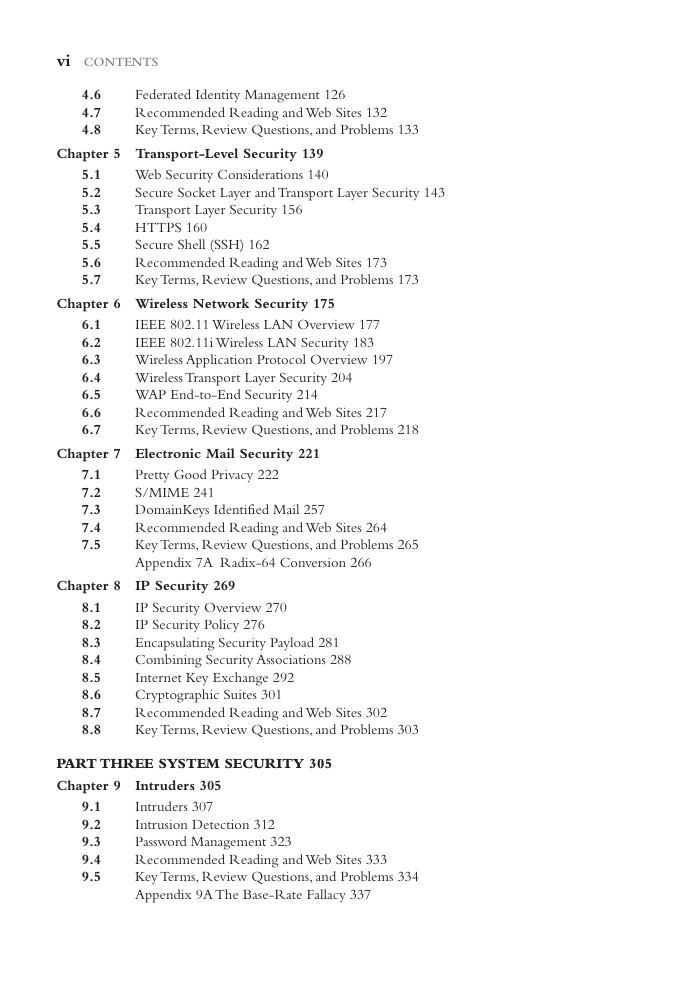
vi CONTENTS
4.6
4.7
4.8
Federated Identity Management 126
Recommended Reading and Web Sites 132
Key Terms, Review Questions, and Problems 133
Chapter 5 Transport-Level Security 139
Web Security Considerations 140
Secure Socket Layer and Transport Layer Security 143
Transport Layer Security 156
HTTPS 160
Secure Shell (SSH) 162
Recommended Reading and Web Sites 173
Key Terms, Review Questions, and Problems 173
5.1
5.2
5.3
5.4
5.5
5.6
5.7
Chapter 6 Wireless Network Security 175
6.1
6.2
6.3
6.4
6.5
6.6
6.7
IEEE 802.11 Wireless LAN Overview 177
IEEE 802.11i Wireless LAN Security 183
Wireless Application Protocol Overview 197
Wireless Transport Layer Security 204
WAP End-to-End Security 214
Recommended Reading and Web Sites 217
Key Terms, Review Questions, and Problems 218
Chapter 7 Electronic Mail Security 221
7.1
7.2
7.3
7.4
7.5
Pretty Good Privacy 222
S/MIME 241
DomainKeys Identified Mail 257
Recommended Reading and Web Sites 264
Key Terms, Review Questions, and Problems 265
Appendix 7A Radix-64 Conversion 266
Chapter 8 IP Security 269
8.1
8.2
8.3
8.4
8.5
8.6
8.7
8.8
IP Security Overview 270
IP Security Policy 276
Encapsulating Security Payload 281
Combining Security Associations 288
Internet Key Exchange 292
Cryptographic Suites 301
Recommended Reading and Web Sites 302
Key Terms, Review Questions, and Problems 303
PART THREE SYSTEM SECURITY 305
Chapter 9 Intruders 305
Intruders 307
Intrusion Detection 312
Password Management 323
Recommended Reading and Web Sites 333
Key Terms, Review Questions, and Problems 334
Appendix 9A The Base-Rate Fallacy 337
9.1
9.2
9.3
9.4
9.5
�
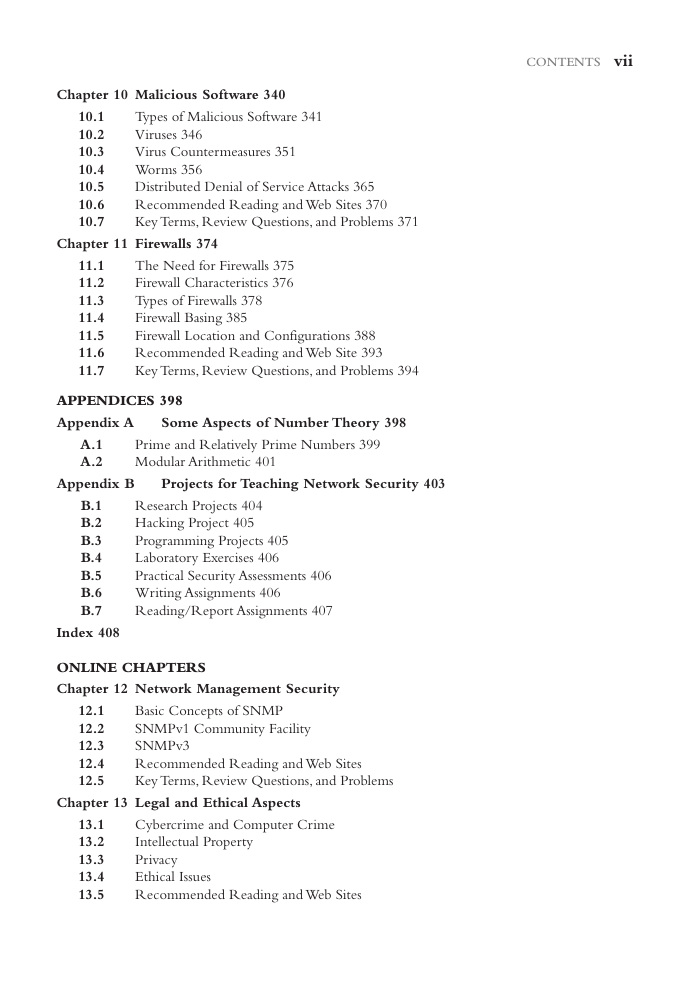
CONTENTS vii
Chapter 10 Malicious Software 340
10.1
10.2
10.3
10.4
10.5
10.6
10.7
Types of Malicious Software 341
Viruses 346
Virus Countermeasures 351
Worms 356
Distributed Denial of Service Attacks 365
Recommended Reading and Web Sites 370
Key Terms, Review Questions, and Problems 371
Chapter 11 Firewalls 374
11.1
11.2
11.3
11.4
11.5
11.6
11.7
The Need for Firewalls 375
Firewall Characteristics 376
Types of Firewalls 378
Firewall Basing 385
Firewall Location and Configurations 388
Recommended Reading and Web Site 393
Key Terms, Review Questions, and Problems 394
APPENDICES 398
Appendix A
Some Aspects of Number Theory 398
A.1
A.2
Prime and Relatively Prime Numbers 399
Modular Arithmetic 401
Appendix B
Projects for Teaching Network Security 403
B.1
B.2
B.3
B.4
B.5
B.6
B.7
Research Projects 404
Hacking Project 405
Programming Projects 405
Laboratory Exercises 406
Practical Security Assessments 406
Writing Assignments 406
Reading/Report Assignments 407
Index 408
ONLINE CHAPTERS
Chapter 12 Network Management Security
12.1
12.2
12.3
12.4
12.5
Basic Concepts of SNMP
SNMPv1 Community Facility
SNMPv3
Recommended Reading and Web Sites
Key Terms, Review Questions, and Problems
Chapter 13 Legal and Ethical Aspects
13.1
13.2
13.3
13.4
13.5
Cybercrime and Computer Crime
Intellectual Property
Privacy
Ethical Issues
Recommended Reading and Web Sites
�


 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc