SECOND
EDITION
MODSECURITY
HANDBOOK
The Complete Guide to the Popular
Open Source Web Application Firewall
Free edition: Getting Started
Christian Folini
Ivan Ristić
Last update: Mon May 07 15:46:04 BST 2018 (build 10)
�
Everything you need to know
about ModSecurity, in one place
SECOND
EDITION
MODSECURITY
HANDBOOK
The Complete Guide to the Popular
Open Source Web Application Firewall
Christian Folini
Ivan Ristić
To purchase the full book, go to:
https://www.feistyduck.com
FINE TECHNOLOGY BOOKS
�
ModSecurity Handbook
Christian Folini, Ivan Ristić
�
ModSecurity Handbook: Getting Started
by Christian Folini, Ivan Ristić
Copyright © 2017 Feisty Duck Limited. All rights reserved.
ISBN: 978-1-90711708-4
Published in July 2017 (build 10). First edition published in March 2010.
Feisty Duck Limited
www.feistyduck.com
contact@feistyduck.com
Address:
6 Acantha Court
Montpelier Road
London W5 2QP
United Kingdom
Production editor: Jelena Girić-Ristić
Copyeditor: Melinda Rankin
Cover design: Peter Jovanović
Cover illustration: Maja Veselinović
All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or
by any means, without the prior permission in writing of the publisher.
The author and publisher have taken care in preparation of this book, but make no expressed or implied warranty of any kind and
assume no responsibility for errors or omissions. No liability is assumed for incidental or consequential damages in connection
with or arising out of the use of the information or programs contained herein.
ModSecurity is a registered trademark of Trustwave Holdings, Inc. All other trademarks and copyrights are the property of their
respective owners.
Licensed for the exclusive use of:
clay tang
Feisty Duck DigitalBook Distributionwww.feistyduck.com�
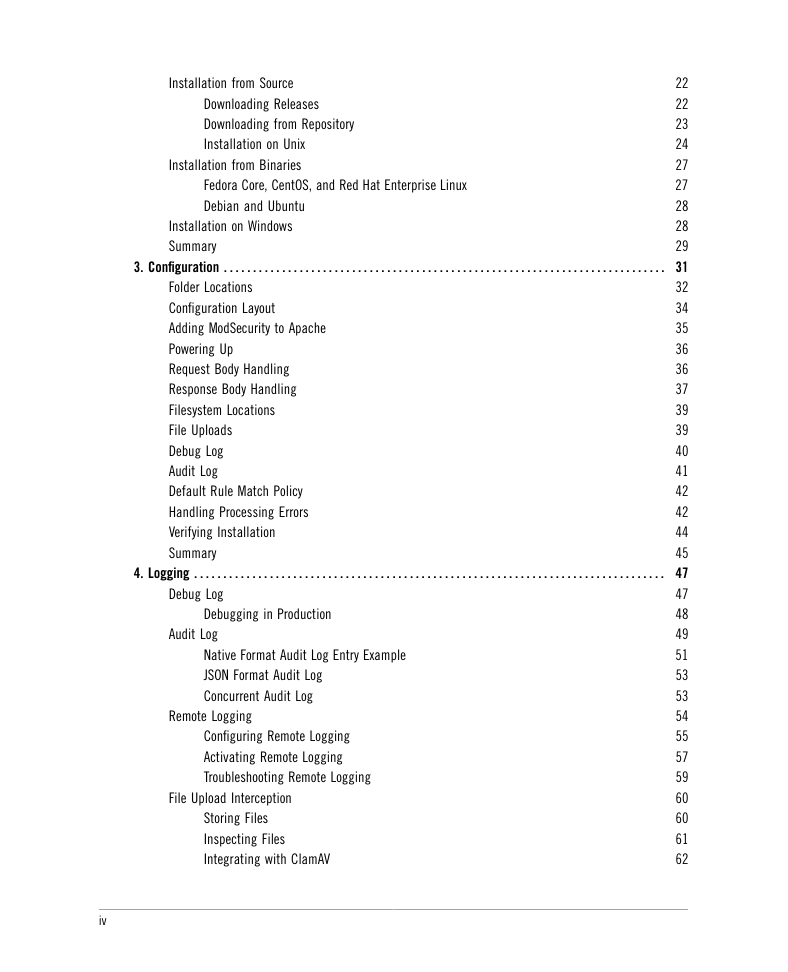
Table of Contents
I. User Guide
1. Introduction . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Scope and Audience
Contents
Updates
Feedback
About the Author
About the Technical Reviewer
Acknowledgments
Preface to the Free Edition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . vii
Preface to the Second Edition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ix
Preface to the First Edition . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi
xi
xii
xv
xv
xv
xvi
xvi
1
3
3
5
7
7
8
8
9
10
11
16
17
18
18
19
19
19
2. Installation . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 21
Hybrid Nature of ModSecurity
Main Areas of Functionality
What Rules Look Like
Transaction Lifecycle
Impact on Web Server
What’s Next?
Brief History of ModSecurity
What Can ModSecurity Do?
Guiding Principles
Deployment Options
Getting Started
Resources
Summary
General Resources
Developer Resources
AuditConsole
iii
�
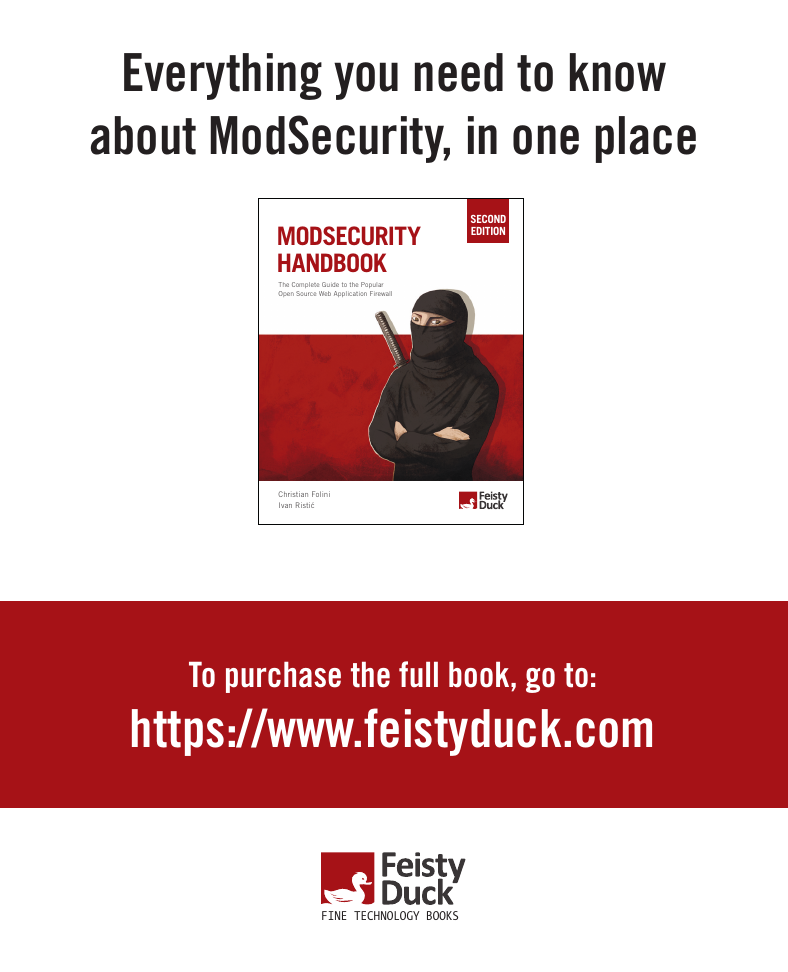
Installation from Source
Installation on Windows
Summary
Fedora Core, CentOS, and Red Hat Enterprise Linux
Debian and Ubuntu
Downloading Releases
Downloading from Repository
Installation on Unix
Installation from Binaries
Folder Locations
Configuration Layout
Adding ModSecurity to Apache
Powering Up
Request Body Handling
Response Body Handling
Filesystem Locations
File Uploads
Debug Log
Audit Log
Default Rule Match Policy
Handling Processing Errors
Verifying Installation
Summary
22
22
23
24
27
27
28
28
29
3. Configuration . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 31
32
34
35
36
36
37
39
39
40
41
42
42
44
45
47
47
48
49
51
53
53
54
55
57
59
60
60
61
62
Native Format Audit Log Entry Example
JSON Format Audit Log
Concurrent Audit Log
File Upload Interception
Storing Files
Inspecting Files
Integrating with ClamAV
4. Logging . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Debug Log
Audit Log
Debugging in Production
Remote Logging
Configuring Remote Logging
Activating Remote Logging
Troubleshooting Remote Logging
iv
�
64
65
65
65
67
67
Index . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 69
Increasing Logging from a Rule
Dynamically Altering Logging Configuration
Removing Sensitive Data from Audit Logs
Selective Audit Logging
Advanced Logging Configuration
Summary
v
�
Preface to the Free Edition
Welcome to ModSecurity Handbook: Getting Started. This is a special free version that consists
of the first four chapters of the full book. Since ModSecurity Handbook went into print, we re-
alized that there were many new users of ModSecurity who were not yet interested in master-
ing this tool (and wouldn’t consider buying a book) but who could benefit from having access
to better documentation. This version offers exactly that, with an introduction to ModSecuri-
ty in Chapter 1, and coverage of installation and configuration in Chapters 2, 3, and 4. Enjoy!
vii
�




 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc