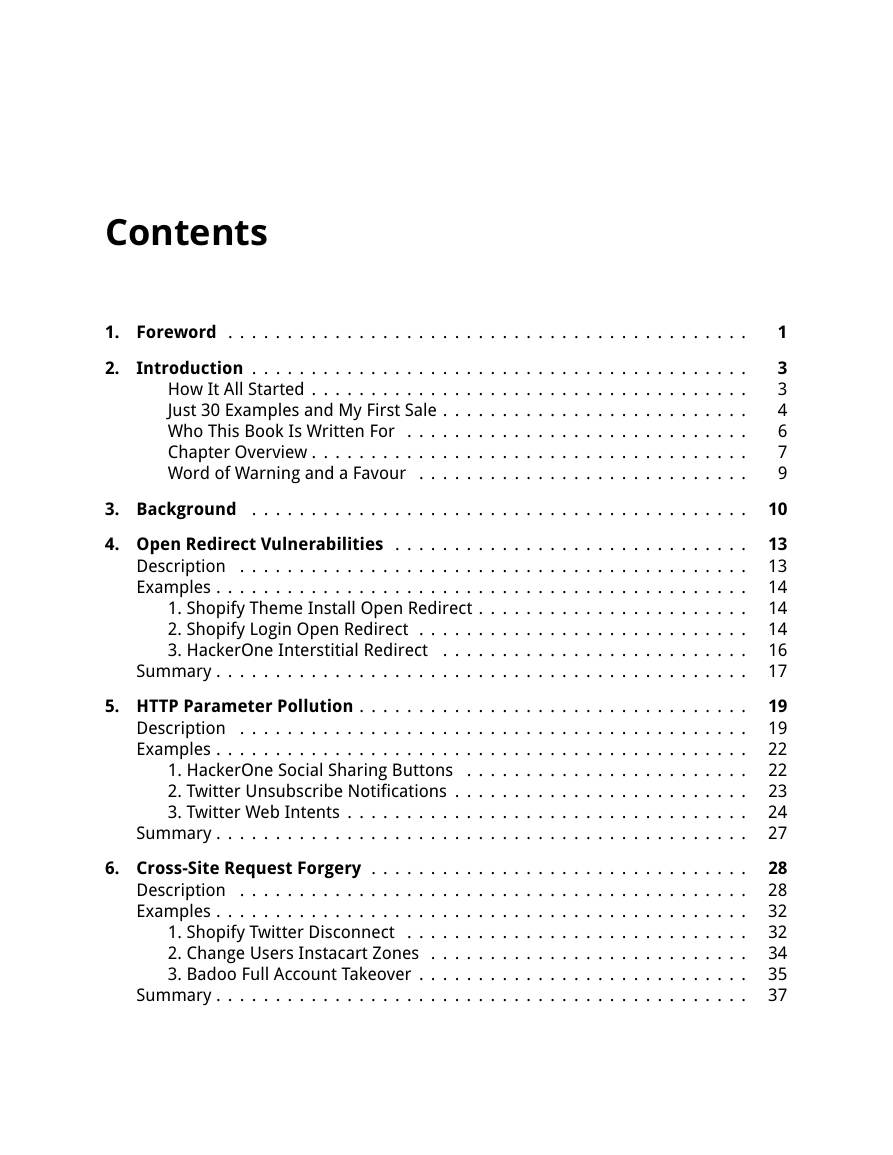
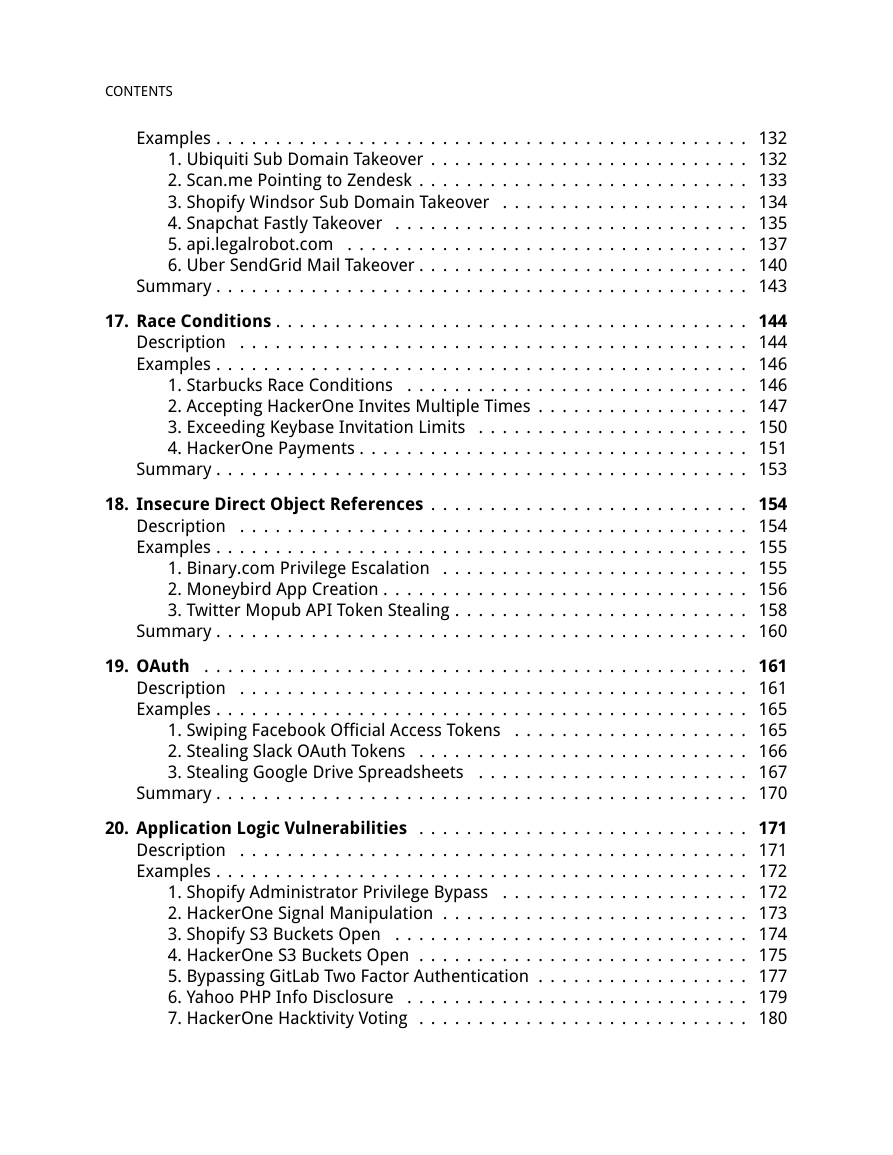
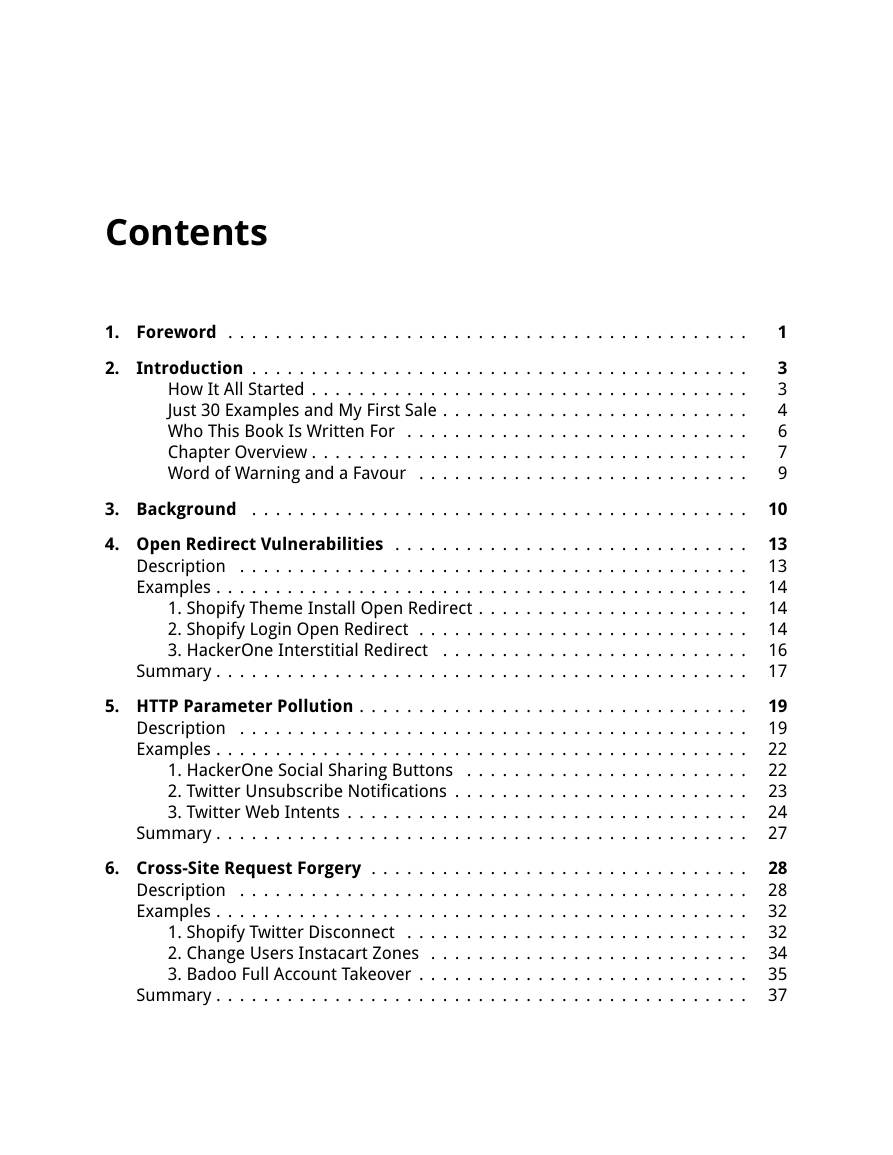
Table of Contents
Foreword
Introduction
How It All Started
Just 30 Examples and My First Sale
Who This Book Is Written For
Chapter Overview
Word of Warning and a Favour
Background
Open Redirect Vulnerabilities
Description
Examples
1. Shopify Theme Install Open Redirect
2. Shopify Login Open Redirect
3. HackerOne Interstitial Redirect
Summary
HTTP Parameter Pollution
Description
Examples
1. HackerOne Social Sharing Buttons
2. Twitter Unsubscribe Notifications
3. Twitter Web Intents
Summary
Cross-Site Request Forgery
Description
Examples
1. Shopify Twitter Disconnect
2. Change Users Instacart Zones
3. Badoo Full Account Takeover
Summary
HTML Injection
Description
Examples
1. Coinbase Comments
2. HackerOne Unintended HTML Inclusion
3. Within Security Content Spoofing
Summary
CRLF Injection
Description
1. Twitter HTTP Response Splitting
2. v.shopify.com Response Splitting
Summary
Cross-Site Scripting
Description
Examples
1. Shopify Wholesale
2. Shopify Giftcard Cart
3. Shopify Currency Formatting
4. Yahoo Mail Stored XSS
5. Google Image Search
6. Google Tagmanager Stored XSS
7. United Airlines XSS
Summary
Template Injection
Description
Server Side Template Injections
Client Side Template Injections
Examples
1. Uber Angular Template Injection
2. Uber Template Injection
3. Rails Dynamic Render
Summary
SQL Injection
Description
SQL Databases
Countermeasures Against SQLi
Examples
1. Drupal SQL Injection
2. Yahoo Sports Blind SQL
3. Uber Blind SQLi
Summary
Server Side Request Forgery
Description
HTTP Request Location
Invoking GET Versus POST Requests
Blind SSRFs
Leveraging SSRF
Examples
1. ESEA SSRF and Querying AWS Metadata
2. Google Internal DNS SSRF
3. Internal Port Scanning
Summary
XML External Entity Vulnerability
Description
Examples
1. Read Access to Google
2. Facebook XXE with Word
3. Wikiloc XXE
Summary
Remote Code Execution
Description
Examples
1. Polyvore ImageMagick
2. Algolia RCE on facebooksearch.algolia.com
3. Foobar Smarty Template Injection RCE
Summary
Memory
Description
Buffer Overflow
Read out of Bounds
Memory Corruption
Examples
1. PHP ftp_genlist()
2. Python Hotshot Module
3. Libcurl Read Out of Bounds
4. PHP Memory Corruption
Summary
Sub Domain Takeover
Description
Examples
1. Ubiquiti Sub Domain Takeover
2. Scan.me Pointing to Zendesk
3. Shopify Windsor Sub Domain Takeover
4. Snapchat Fastly Takeover
5. api.legalrobot.com
6. Uber SendGrid Mail Takeover
Summary
Race Conditions
Description
Examples
1. Starbucks Race Conditions
2. Accepting HackerOne Invites Multiple Times
3. Exceeding Keybase Invitation Limits
4. HackerOne Payments
Summary
Insecure Direct Object References
Description
Examples
1. Binary.com Privilege Escalation
2. Moneybird App Creation
3. Twitter Mopub API Token Stealing
Summary
OAuth
Description
Examples
1. Swiping Facebook Official Access Tokens
2. Stealing Slack OAuth Tokens
3. Stealing Google Drive Spreadsheets
Summary
Application Logic Vulnerabilities
Description
Examples
1. Shopify Administrator Privilege Bypass
2. HackerOne Signal Manipulation
3. Shopify S3 Buckets Open
4. HackerOne S3 Buckets Open
5. Bypassing GitLab Two Factor Authentication
6. Yahoo PHP Info Disclosure
7. HackerOne Hacktivity Voting
8. Accessing PornHub's Memcache Installation
9. Bypassing Twitter Account Protections
Summary
Getting Started
Reconnaissance
Subdomain Enumeration
Port Scanning
Screenshotting
Content Discovery
Previous Bugs
Testing the Application
The Technology Stack
Functionality Mapping
Finding Vulnerabilities
Going Further
Summary
Vulnerability Reports
Read the disclosure guidelines.
Include Details. Then Include More.
Confirm the Vulnerability
Show Respect for the Company
Bounties
Don't Shout Hello Before Crossing the Pond
Parting Words
Tools
Burp Suite
ZAP Proxy
Knockpy
HostileSubBruteforcer
Sublist3r
crt.sh
IPV4info.com
SecLists
XSSHunter
sqlmap
Nmap
Eyewitness
Gowitness
Gobuster
Meg
Shodan
Censys
What CMS
BuiltWith
Nikto
Recon-ng
GitRob
CyberChef
OnlineHashCrack.com
idb
Wireshark
Bucket Finder
Race the Web
Google Dorks
JD GUI
Mobile Security Framework
Ysoserial
Firefox Plugins
FoxyProxy
User Agent Switcher
Firebug
Hackbar
Websecurify
Cookie Manager+
XSS Me
Offsec Exploit-db Search
Wappalyzer
Resources
Online Training
Web Application Exploits and Defenses
The Exploit Database
Udacity
Bug Bounty Platforms
Hackerone.com
Bugcrowd.com
Synack.com
Cobalt.io
Video Tutorials
youtube.com/yaworsk1
Seccasts.com
How to Shot Web
Further Reading
OWASP.com
Hackerone.com/hacktivity
https://bugzilla.mozilla.org
Twitter #infosec and #bugbounty
Twitter @disclosedh1
Web Application Hackers Handbook
Bug Hunters Methodology
Recommended Blogs
philippeharewood.com
Philippe's Facebook Page - www.facebook.com/phwd-113702895386410
fin1te.net
NahamSec.com
blog.it-securityguard.com
blog.innerht.ml
blog.orange.tw
Portswigger Blog
Nvisium Blog
blog.zsec.uk
brutelogic.com.br
lcamtuf.blogspot.ca
Bug Crowd Blog
HackerOne Blog
Cheatsheets
Glossary
Black Hat Hacker
Buffer Overflow
Bug Bounty Program
Bug Report
CRLF Injection
Cross Site Request Forgery
Cross Site Scripting
HTML Injection
HTTP Parameter Pollution
HTTP Response Splitting
Memory Corruption
Open Redirect
Penetration Testing
Researchers
Response Team
Responsible Disclosure
Vulnerability
Vulnerability Coordination
Vulnerability Disclosure
White Hat Hacker
Appendix A - Take Aways
Open Redirects
HTTP Parameter Pollution
Cross Site Request Forgery
HTML Injection
CRLF Injections
Cross-Site Scripting
SSTI
SQL Injection
Server Side Request Forgery
XML External Entity Vulnerability
Remote Code Execution
Memory
Sub Domain Takeover
Race Conditions
Insecure Direct Object References
OAuth
Application Logic Vulnerabilities
Appendix B - Web Hacking 101 Changelog




 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc