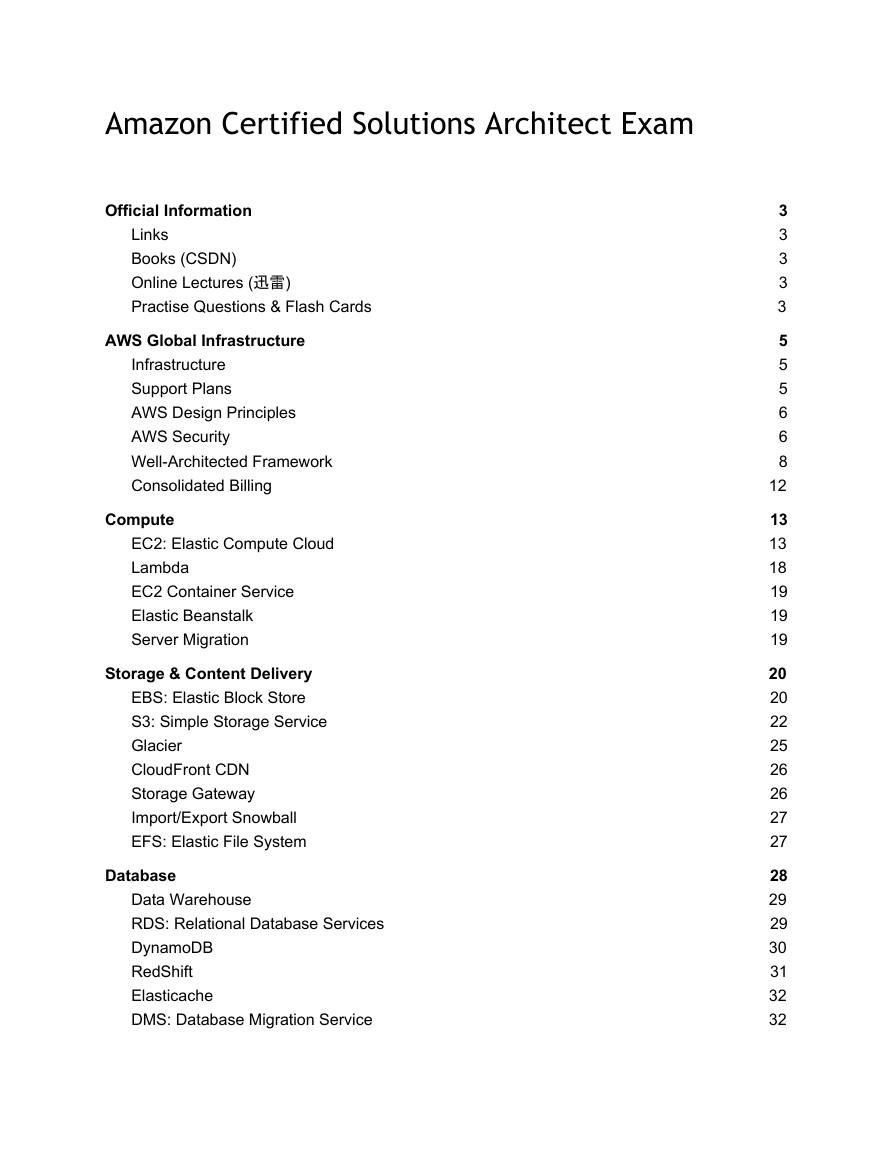
Amazon Certified Solutions Architect Exam
Official Information
Links
Books (CSDN)
Online Lectures (迅雷)
Practise Questions & Flash Cards
AWS Global Infrastructure
Infrastructure
Support Plans
AWS Design Principles
AWS Security
Well-Architected Framework
Consolidated Billing
Compute
EC2: Elastic Compute Cloud
Lambda
EC2 Container Service
Elastic Beanstalk
Server Migration
Storage & Content Delivery
EBS: Elastic Block Store
S3: Simple Storage Service
Glacier
CloudFront CDN
Storage Gateway
Import/Export Snowball
EFS: Elastic File System
Database
Data Warehouse
RDS: Relational Database Services
DynamoDB
RedShift
Elasticache
DMS: Database Migration Service
3
3
3
3
3
5
5
5
6
6
8
12
13
13
18
19
19
19
20
20
22
25
26
26
27
27
28
29
29
30
31
32
32
�
Aurora
Networking
DNS: Domain Name Service
Route53 (DNS)
VPC: Virtual Private Cloud
Direct Connect
ELB: Elastic Load Balancer
Developer Tools
CodeCommit
CodePipeline
CodeDeploy
Management Tools
CloudFormation
CloudWatch
CloudTrail
Auto Scaling
Config
Service Catalog
Trusted Advisor
Resource Groups
OpsWorks
Security & Identity
IAM: Identity & Access Management
WAF: Web Application Firewall
Inspector
Directory Service
Analytics
EMR
Kinesis
Data Pipeline
Machine Learning
Internet Of Things
AWS IoT
Mobile Services
Cognito
Device Farm
32
33
34
34
35
41
41
43
44
44
44
45
45
45
45
46
46
46
46
46
47
47
48
49
49
49
49
49
50
50
50
51
51
52
52
52
�
Mobile Hub
Mobile Analytics
SNS: Simple Notification Service
Application Services
API Gateway
SQS: Simple Queue Service
SWF: Simple Workflow Service
AppStream
Elastic Transcoder
SES
CloudSearch
Game Development
Enterprise Applications
WorkSpaces (VDI)
WorkDocs
WorkMail
Questions & Answers
Official Information
Links
52
52
52
54
54
54
54
54
54
55
55
56
57
57
57
57
58
-
-
https://aws.amazon.com/certification/certification-prep/
http://awstrainingandcertification.s3.amazonaws.com/production/AWS_certified_solution
s_architect_associate_blueprint.pdf
Books (CSDN)
- AWS Certified Solutions Architect Official Study Guide: Associate Exam (2016, Sybex)
- www.wiley.com/go/sybextestprep (questions: 368, flashcards: 100)
Online Lectures (迅雷)
- ACloudGuru AWS Solutions Architect Exam Prep Course (udemy)
-
Linuxacademy AWS Solutions Architect
- CBTNugggets AWS Solutions Architect
Practise Questions & Flash Cards
- www.wiley.com/go/sybextestprep (questions: 368, flashcards: 100)
�
-
-
-
-
-
-
http://thecertschool.com/category/aws/
http://www.dennyzhang.com/aws_associate_cert/
http://blog.flux7.com/blogs/quizzes/cloud-computing-quiz-1-check-your-knowledge-on-a
ws
http://searchaws.techtarget.com/quiz/Amazon-Web-Services-Security-Quiz
http://searchaws.techtarget.com/quiz/Test-your-knowledge-Amazon-Simple-Storage-Ser
vice-quiz
http://searchaws.techtarget.com/quiz/Take-our-quiz-to-find-out-what-you-know-about-A
WS-IaaS
http://www.silicon.co.uk/quiz/amazon-web-services-145-1
http://searchaws.techtarget.com/quiz/Test-your-knowledge-Amazon-Redshift-quiz
http://www.awsomeblog.com/aws-certified-solutions-architect-exam-sample-quiz/
http://www.cloudsolutionsbook.com/amazon-cloud-solutions/june-20th-2015
http://www.huangbowen.net/blog/2014/10/22/aws-cert-sample-question/
http://quizlet.com/35935418/detailed-questions-flash-cards/
-
-
-
-
-
-
- CramFLASH Study Flashcards for AWS Developer Associate Exam: 60 “cards” are
included
- CramFLASH Study Flashcards for AWS SysOps Admin Associate Exam: 50 flashcards
included
- AWS Solutions Architect Apps on Android
�
AWS Global Infrastructure
Infrastructure
-
>16 Regions:
-
-
a region is a geographical area consisting 2 or more availability zones
complete independent and isolated from other regions
-
-
-
-
-
-
-
resources aren't replicated across regions unless organizations choose to
do so
data locality
sovereignty concerns
located close to end users, minimize latency
far from primary facilities to satisfy disaster recovery and compliance
needs
foundation for meeting location dependent privacy and compliance
requirements
customer has full control - AWS does not move customer’s resources
-
>42 Availability Zones
-
-
-
simply a data center
connected via an inexpensive, low latency network
distinct locations engineered to be insulated from failures in other availability
zones
isolated, but AZs in a region are connected through low-latency links
-
- AZs in a region are physically separated within a typical metropolitan region
-
-
-
- HA: deploy across multiple AZs
located in lower-risk flood plains
uses UPS and on-site backup generators
redundantly connected to multiple tier-1 transit providers
-
>54 Edge Locations
- CDN endpoints for CloudFront
- many more than regions
- AWS cloud service model: IaaS (infrastructure-as-a-service)
-
other models:PaaS, SaaS
- AWS access:
- Management Console
- CLI
- SDK (API)
Support Plans
- Basic, Developer, Business, Enterprise
- Response Times:
-
-
general guidance: <24h
system impaired: <12h
�
-
-
-
production system impaired: <4h (business, enterprise)
production system down: <1h (business, enterprise)
business-critical system down: <15min (enterprise)
-
Trusted Advisor: basic+developer: 4 core set of checks only
AWS Design Principles
- Deployment Models:
-
-
all-in cloud-based application: fully deployed in the cloud
-
-
public
private
hybrid deployment: connects infrastructure between cloud-based resources and
existing data center. leverage dedicated connectivity, identity federation, and
integrated tools
- Design for failure:
-
-
-
assume things will fail
recovery strategies during design time:
-
-
design automated recovery from failure
assume more than the expected number of requests per second some
day
decouple components
-
Implement Elasticity:
-
-
-
proactive cyclic scaling: periodic scaling at fixed interval (daily, weekly, …)
proactive event-based scaling: scaling when expecting a big surge of traffic due
to a scheduled business event (e.g. new product launch, marketing campaigns)
auto-scaling based on demand: take actions to scale up or down based on
metrics (e.g. cpu load, network I/O)
- Advantages of Cloud:
-
almost zero upfront infrastructure investment: trade capital expense for “variable
expense”
benefit from massive “economies of scale”
-
- more efficient resource utilization: stop guessing about capacity
-
-
-
just-in-time infrastructure: increase speed and agility
usage-based costing: stop spending money running and maintaining data centers
reduced time-to-market: go global in minutes
-
Technical benefits:
automation: scriptable infrastructure
automated elasticity and scalability
proactive scaling
-
-
-
- more efficient development lifecycle
-
-
improved testability
disaster recovery and business continuity
�
AWS Security
-
-
-
-
electronic surveillance and multi-factor access control systems
24x7 staffed by security guards
access is authorised on a “least privilege basis”
shared security model:
- AWS: responsible for securing the underlying infrastructure
-
-
-
global infrastructure
services offered in the cloud
security configuration, patches, antivirus etc. of managed services (e.g.
DynamoDB, RDS, Redshift, EMR, WorkSpaces)
- Customer: responsible for anything you put on the cloud or connect to the cloud
-
full root access on guest operating system
- AWS does not have any access rights to the guest OS
-
available on instance types from M3, C3, R3 and G2: encrypted
EBS volumes and snapshots with AES-256
-
IAAS: security configuration and management tasks on EC2, VPC, S3
- managed services: account management and user access control (e.g.
MFA, SSL/TLS, user activity logging with CloudTrail)
- Physical and environmental security:
fire detection and suppression
redundant and maintainable power systems
climate and temperature control
preventive monitoring
-
-
-
-
- Storage Decommissioning:
-
-
prevents customer data from being exposed to unauthorized individuals
all decommissioned magnetic storage devices are degaussed and
physically destroyed
- DoD 5220.22-M (national industrial security program operating manual)
- NIST 800-88: guidelines for media sanitization
- Business continuity management
-
-
-
availability: data centers built in clusters in various global regions
incident response: 7x24h coverage to detect incidents and to manage the impact
and resolution
communication: training programs, service health dashboard
- Network security:
- Secure network architecture
-
network ACLs
- Secure access points:
- monitored HTTP/HTTPS API endpoints
-
redundant ISP connections
-
Transmission protection:
- HTTPS using SSL
�
- VPC: private subnet
- ELB: SSL termination on the load balancer is supported
- Monitoring and protection:
- DDoS (Distributed denial of service) attacks
- MITM: man in the middle attacks
-
IP spoofing: firewall denials instance sending traffic with a source IP or
MAC address other than its own
- Port scanning: attacks such as ARP cache poisoning do not work within
EC2 and VPC
- Packet Sniffing by other tenants: it is not possible for a virtual instance
running in promiscuous mode to receive or sniff traffic that is intended for
a different virtual instance
- AWS regularly scans all internet facing IP addresses for vulnerabilities
(not include customer instances)
regular vulnerability threat assessments by independent security firms
-
-
-
IPsec VPN: encrypted tunnel between VPC and your data center
Logically the AWS production network is segregated from the Amazon Corporate
network
- AWS acceptable use policy:
-
you must request a vulnerability scan in advance
- Direct Connect: dedicated connection using 802.1q VLAN
-
Trusted Advisor:
- makes recommendations to save money, improve performance and close
security gaps, e.g.
open ports
public access to S3 buckets
enable user activity logging (CloudTrail)
-
-
-
- MFA on root account
- VPC security:
- API access encrypted with SSL and signed by secret access key
-
-
-
-
-
-
subnets and route tables
firewall (security groups)
network ACLs
virtual private gateway: private connectivity between VPC and another network
internet gateway
dedicated instances: physically isolated
- EC2 security:
- multiple levels of security: OS of host platform, guest OS, firewall and signed API
calls
hypervisor: highly customized Xen hypervisor
Instances Isolation:
-
-
-
customers’ instances → hypervisor → virtual interfaces → security groups
→ firewall → physical interfaces
�


 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc