Computer Networking: A Top-Down Approach
Featuring the Internet, 5th Edition
Solutions to Review Questions and Problems
Version Date: 1 September 2009
This document contains the solutions to review questions and problems for the 5th
edition of Computer Networking: A Top-Down Approach Featuring the Internet by Jim
Kurose and Keith Ross. These solutions are being made available to instructors ONLY.
Please do NOT copy or distribute this document to others (even other instructors). Please
do not post any solutions on a publicly-available Web site. We’ll be happy to provide a
copy (up-to-date) of this solution manual ourselves to anyone who asks.
Acknowledgments: Over the years, several students and colleagues have helped us
prepare this solutions manual. Special thanks goes to Honggang Zhang, Rakesh Kumar,
and Prithula Dunghel.
All material © copyright 1996-2009 by J.F. Kurose and K.W. Ross. All rights reserved
�
Chapter 1 Review Questions
1. There is no difference. Throughout this text, the words “host” and “end system” are
used interchangeably. End systems include PCs, workstations, Web servers, mail
servers, Internet-connected PDAs, WebTVs, etc.
2. Suppose Alice, an ambassador of country A wants to invite Bob, an ambassador of
country B, over for dinner. Alice doesn’t simply just call Bob on the phone and say,
“come to our dinner table now”. Instead, she calls Bob and suggests a date and time.
Bob may respond by saying he’s not available that particular date, but he is available
another date. Alice and Bob continue to send “messages” back and forth until they
agree on a date and time. Bob then shows up at the embassy on the agreed date,
hopefully not more than 15 minutes before or after the agreed time. Diplomatic
protocols also allow for either Alice or Bob to politely cancel the engagement if they
have reasonable excuses.
3. A networking program usually has two programs, each running on a different host,
communicating with each other. The program that initiates the communication is the
client. Typically, the client program requests and receives services from the server
program.
4. 1. Dial-up modem over telephone line: residential; 2. DSL over telephone line:
residential or small office; 3. Cable to HFC: residential; 4. 100 Mbps switched
Etherent: company; 5. Wireless LAN: mobile; 6. Cellular mobile access (for example,
WAP): mobile
5. HFC bandwidth is shared among the users. On the downstream channel, all packets
emanate from a single source, namely, the head end. Thus, there are no collisions in
the downstream channel.
6. Current possibilities include: dial-up; DSL; cable modem; fiber-to-the-home.
7. Ethernet LANs have transmission rates of 10 Mbps, 100 Mbps, 1 Gbps and 10 Gbps.
For an X Mbps Ethernet (where X = 10, 100, 1,000 or 10,000), a user can
continuously transmit at the rate X Mbps if that user is the only person sending data.
If there are more than one active user, then each user cannot continuously transmit at
X Mbps.
8. Ethernet most commonly runs over twisted-pair copper wire and “thin” coaxial cable.
It also can run over fibers optic links and thick coaxial cable.
9. Dial up modems: up to 56 Kbps, bandwidth is dedicated; ISDN: up to 128 kbps,
bandwidth is dedicated; ADSL: downstream channel is .5-8 Mbps, upstream channel
is up to 1 Mbps, bandwidth is dedicated; HFC, downstream channel is 10-30 Mbps
and upstream channel is usually less than a few Mbps, bandwidth is shared. FTTH: 2-
10Mbps upload; 10-20 Mbps download; bandwidth is not shared.
�
10. There are two most popular wireless Internet access technologies today:
In a wireless LAN, wireless users transmit/receive packets to/from a base station
(wireless access point) within a radius of few tens of meters. The base station is
typically connected to the wired Internet and thus serves to connect wireless users
to the wired network.
a) Wireless LAN
b) Wide-area wireless access network
In these systems, packets are transmitted over the same wireless infrastructure
used for cellular telephony, with the base station thus being managed by a
telecommunications provider. This provides wireless access to users within a
radius of tens of kilometers of the base station.
11. A circuit-switched network can guarantee a certain amount of end-to-end bandwidth
for the duration of a call. Most packet-switched networks today (including the
Internet) cannot make any end-to-end guarantees for bandwidth.
12. In a packet switched network, the packets from different sources flowing on a link do
not follow any fixed, pre-defined pattern. In TDM circuit switching, each host gets
the same slot in a revolving TDM frame.
13. At time t0 the sending host begins to transmit. At time t1 = L/R1, the sending host
completes transmission and the entire packet is received at the router (no propagation
delay). Because the router has the entire packet at time t1, it can begin to transmit the
packet to the receiving host at time t1. At time t2 = t1 + L/R2, the router completes
transmission and the entire packet is received at the receiving host (again, no
propagation delay). Thus, the end-to-end delay is L/R1 + L/R2.
14. A tier-1 ISP connects to all other tier-1 ISPs; a tier-2 ISP connects to only a few of
the tier-1 ISPs. Also, a tier-2 ISP is a customer of one or more tier-1.
15. a) 2 users can be supported because each user requires half of the link bandwidth.
b) Since each user requires 1Mbps when transmitting, if two or fewer users transmit
simultaneously, a maximum of 2Mbps will be required. Since the available
bandwidth of the shared link is 2Mbps, there will be no queuing delay before the
link. Whereas, if three users transmit simultaneously, the bandwidth required
will be 3Mbps which is more than the available bandwidth of the shared link. In
this case, there will be queuing delay before the link.
c) Probability that a given user is transmitting = 0.2
d) Probability that all three users are transmitting simultaneously =
⎛
⎜⎜
⎝
3
3
p
(
3 1
−
p
−
) 33
⎞
⎟⎟
⎠
�
= (0.2)3 = 0.008. Since the queue grows when all the users are transmitting, the
fraction of time during which the queue grows (which is equal to the probability
that all three users are transmitting simultaneously) is 0.008.
16. The delay components are processing delays, transmission delays, propagation
delays, and queuing delays. All of these delays are fixed, except for the queuing
delays, which are variable.
17. Java Applet
18. 10msec; d/s; no; no
19. a) 500 kbps
b) 64 seconds
c) 100kbps; 320 seconds
20. End system A breaks the large file into chunks. To each chunk, it adds header
generating multiple packets from the file. The header in each packet includes the
address of the destination: end system B. The packet switch uses the destination
address to determine the outgoing link. Asking which road to take is analogous to a
packet asking which outgoing link it should be forwarded on, given the packet’s
address.
21. Java Applet
22. Five generic tasks are error control, flow control, segmentation and reassembly,
multiplexing, and connection setup. Yes, these tasks can be duplicated at different
layers. For example, error control is often provided at more than one layer.
23. The five layers in the Internet protocol stack are – from top to bottom – the
application layer, the transport layer, the network layer, the link layer, and the
physical layer. The principal responsibilities are outlined in Section 1.5.1.
24. Application-layer message: data which an application wants to send and passed onto
the transport layer; transport-layer segment: generated by the transport layer and
encapsulates application-layer message with transport layer header; network-layer
datagram: encapsulates transport-layer segment with a network-layer header; link-
layer frame: encapsulates network-layer datagram with a link-layer header.
25. Routers process layers 1 through 3. (This is a little bit of a white lie, as modern
routers sometimes act as firewalls or caching components, and process layer four as
well.) Link layer switches process layers 1 through 2. Hosts process all five layers.
26. a) Virus
Requires some form of human interaction to spread. Classic example: E-mail
viruses.
�
numbers, looking for vulnerable processes to infect.
b)Worms
No user replication needed. Worm in infected host scans IP addresses and port
c) Trojan horse
Hidden, devious part of some otherwise useful software.
27. Creation of a botnet requires an attacker to find vulnerability in some application or
system (e.g. exploiting the buffer overflow vulnerability that might exist in an
application). After finding the vulnerability, the attacker needs to scan for hosts that
are vulnerable. The target is basically to compromise a series of systems by
exploiting that particular vulnerability. Any system that is part of the botnet can
automatically scan its environment and propagate by exploiting the vulnerability. An
important property of such botnets is that the originator of the botnet can remotely
control and issue commands to all the nodes in the botnet. Hence, it becomes
possible for the attacker to issue a command to all the nodes, that target a single
node (for example, all nodes in the botnet might be commanded by the attacker to
send a TCP SYN message to the target, which might result in a TCP SYN flood
attack at the target).
28. Trudy can pretend to be Bob to Alice (and vice-versa) and partially or completely
modify the message(s) being sent from Bob to Alice. For example, she can easily
change the phrase “Alice, I owe you $1000” to “Alice, I owe you $10,000”.
Furthermore, Trudy can even drop the packets that are being sent by Bob to Alice
(and vise-versa), even if the packets from Bob to Alice are encrypted.
Chapter 1 Problems
Problem 1
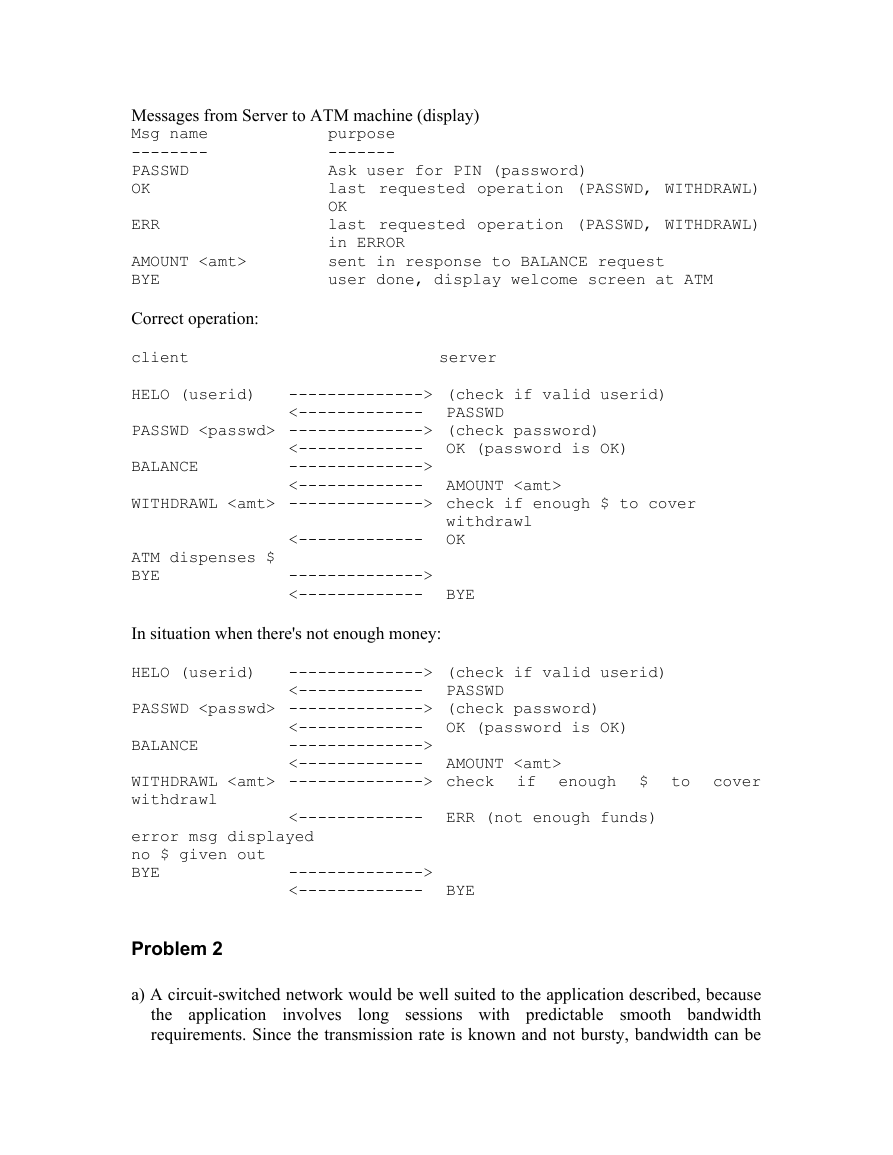
There is no single right answer to this question. Many protocols would do the trick.
Here's a simple answer below:
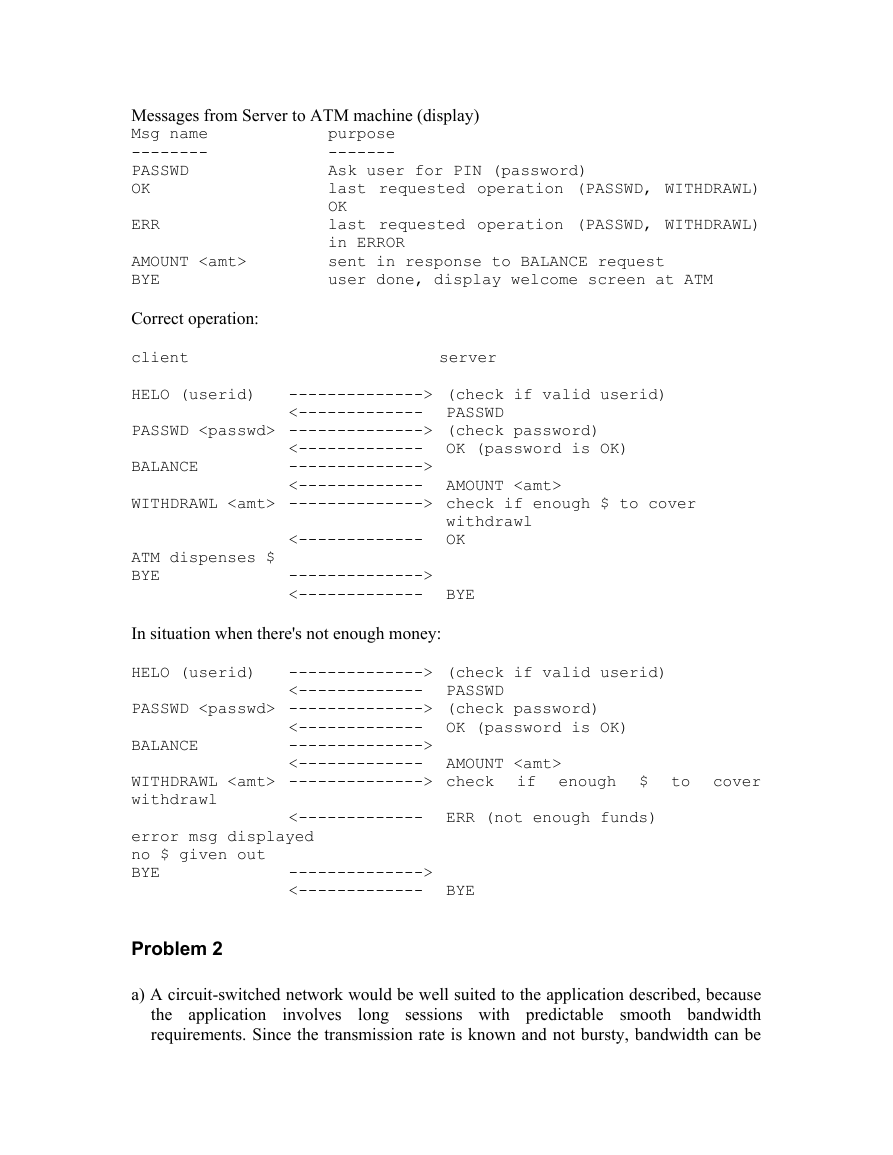
Messages from ATM machine to Server
purpose
Msg name
-------
--------
Let server know that there is a card in the
HELO
ATM machine
ATM card transmits user ID to Server
User enters PIN, which is sent to server
PASSWD
BALANCE
User requests balance
WITHDRAWL User asks to withdraw money
BYE
user all done
�purpose
-------
Ask user for PIN (password)
last requested operation (PASSWD, WITHDRAWL)
OK
last requested operation (PASSWD, WITHDRAWL)
in ERROR
sent in response to BALANCE request
user done, display welcome screen at ATM
Messages from Server to ATM machine (display)
Msg name
--------
PASSWD
OK
ERR
AMOUNT
BYE
Correct operation:
client server
HELO (userid)
PASSWD --------------> (check password)
BALANCE
WITHDRAWL --------------> check if enough $ to cover
ATM dispenses $
BYE
In situation when there's not enough money:
HELO (userid)
PASSWD --------------> (check password)
BALANCE
WITHDRAWL --------------> check if enough $ to cover
withdrawl
error msg displayed
no $ given out
BYE
--------------> (check if valid userid)
<------------- PASSWD
<------------- OK (password is OK)
-------------->
<------------- AMOUNT
<------------- OK
-------------->
<------------- BYE
--------------> (check if valid userid)
<------------- PASSWD
<------------- OK (password is OK)
-------------->
<------------- AMOUNT
withdrawl
<------------- ERR (not enough funds)
-------------->
<------------- BYE
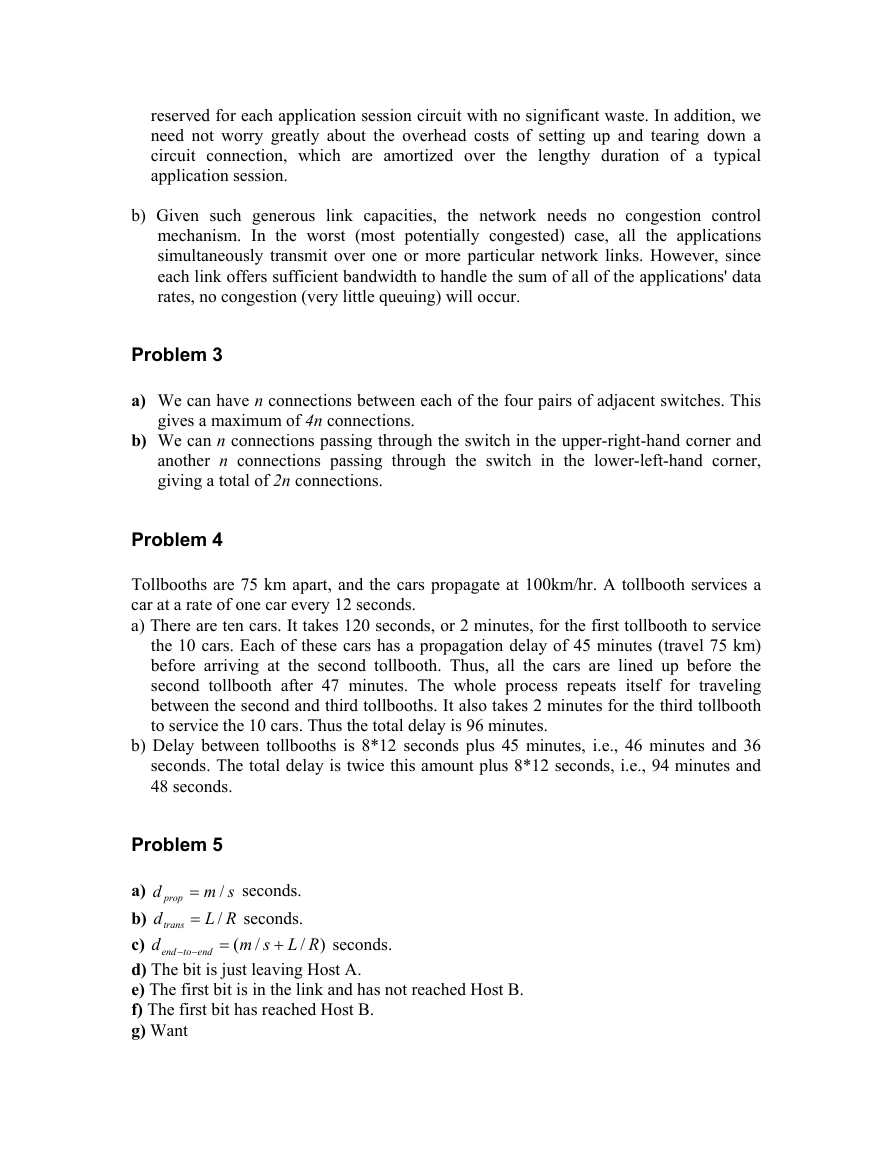
Problem 2
a) A circuit-switched network would be well suited to the application described, because
the application
long sessions with predictable smooth bandwidth
requirements. Since the transmission rate is known and not bursty, bandwidth can be
involves
�reserved for each application session circuit with no significant waste. In addition, we
need not worry greatly about the overhead costs of setting up and tearing down a
circuit connection, which are amortized over the lengthy duration of a typical
application session.
b) Given such generous link capacities, the network needs no congestion control
mechanism. In the worst (most potentially congested) case, all the applications
simultaneously transmit over one or more particular network links. However, since
each link offers sufficient bandwidth to handle the sum of all of the applications' data
rates, no congestion (very little queuing) will occur.
Problem 3
a) We can have n connections between each of the four pairs of adjacent switches. This
gives a maximum of 4n connections.
b) We can n connections passing through the switch in the upper-right-hand corner and
another n connections passing through the switch in the lower-left-hand corner,
giving a total of 2n connections.
Problem 4
Tollbooths are 75 km apart, and the cars propagate at 100km/hr. A tollbooth services a
car at a rate of one car every 12 seconds.
a) There are ten cars. It takes 120 seconds, or 2 minutes, for the first tollbooth to service
the 10 cars. Each of these cars has a propagation delay of 45 minutes (travel 75 km)
before arriving at the second tollbooth. Thus, all the cars are lined up before the
second tollbooth after 47 minutes. The whole process repeats itself for traveling
between the second and third tollbooths. It also takes 2 minutes for the third tollbooth
to service the 10 cars. Thus the total delay is 96 minutes.
b) Delay between tollbooths is 8*12 seconds plus 45 minutes, i.e., 46 minutes and 36
seconds. The total delay is twice this amount plus 8*12 seconds, i.e., 94 minutes and
48 seconds.
d prop
dtrans
d
to
end
−−
sm
/
=
RL
/=
(
=
seconds.
seconds.
RLsm
/
Problem 5
a)
b)
c)
d) The bit is just leaving Host A.
e) The first bit is in the link and has not reached Host B.
f) The first bit has reached Host B.
g) Want
seconds.
end
/
+
)
�
Lm
=
R
s
=
120
10
×
56
(
5.2
3
×
10
8
) 536
=
km.
Problem 6
Consider the first bit in a packet. Before this bit can be transmitted, all of the bits in the
packet must be generated. This requires
The time required to transmit the packet is
856
⋅
310
64
×
sec=7msec.
856
⋅
610
2
×
sec= μ224 sec.
Propagation delay = 10 msec.
The delay until decoding is
7msec + μ224 sec + 10msec = 17.224msec
A similar analysis shows that all bits experience a delay of 17.224 msec.
Problem 7
a) 20 users can be supported.
b)
n
p
. 1.0=p
120
⎛
⎞
(
1
⎜⎜
⎟⎟
n
⎝
⎠
20
∑
−
1
120
n
⎛
⎜⎜
⎝
n
=
0
⎞
⎟⎟
⎠
c)
d)
−
p
120
)
−
n
.
n
p
(
1
−
p
120
)
−
n
.
We use the central limit theorem to approximate this probability. Let
random variables such that
.
p
=
(
XP
)
= 1
j
jX
be independent
(P “21 or more users”
)
−=
1
P
⎛
⎜⎜
⎝
120
∑
1j
=
jX
≤
21
⎞
⎟⎟
⎠
∑
120
X
12
j
1
=
9.01.0
120
⋅
−
⋅
j
X
j
≤
21
⎞
=⎟⎟
⎠
P
⎛
⎜
⎜⎜
⎝
P
⎛
⎜⎜
⎝
120
∑
j
1
=
≤
9
9.01.0
⋅
120
⋅
⎞
⎟
⎟⎟
⎠
�






 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc