1.Basic Feature
Why is Software Secure Boot?
Device requirements of Widevine level 3 security for DRM contents’ protection.
(https://en.wikipedia.org/wiki/Digital_rights_management)
– Device manufacturers must provide a Boot Loader that loads signed system images only.
For devices that allow users to load a custom operating system or gain root privileges on the device by
unlocking the Boot Loader, device manufacturers must support the following:
• Device manufacturers must provide a Boot Loader that allows a Widevine key-box to be written only
when the Boot Loader is in a locked state.
• Device manufacturers must ensure that the Widevine key-box is not readable when the Boot Loader is
unlocked.
• The Widevine key-box must be stored in a region of memory that is erased or is inaccessible when the
device Boot Loader is in an unlocked state.
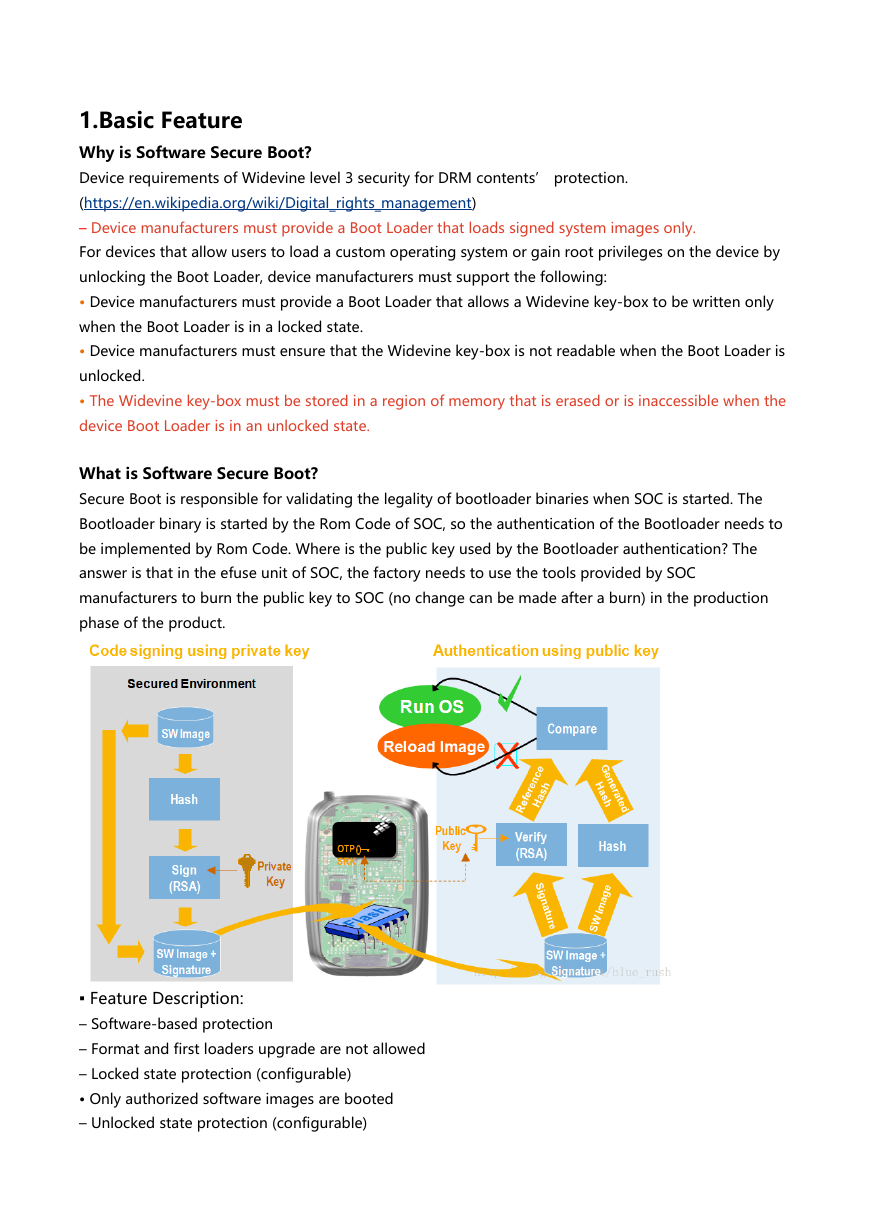
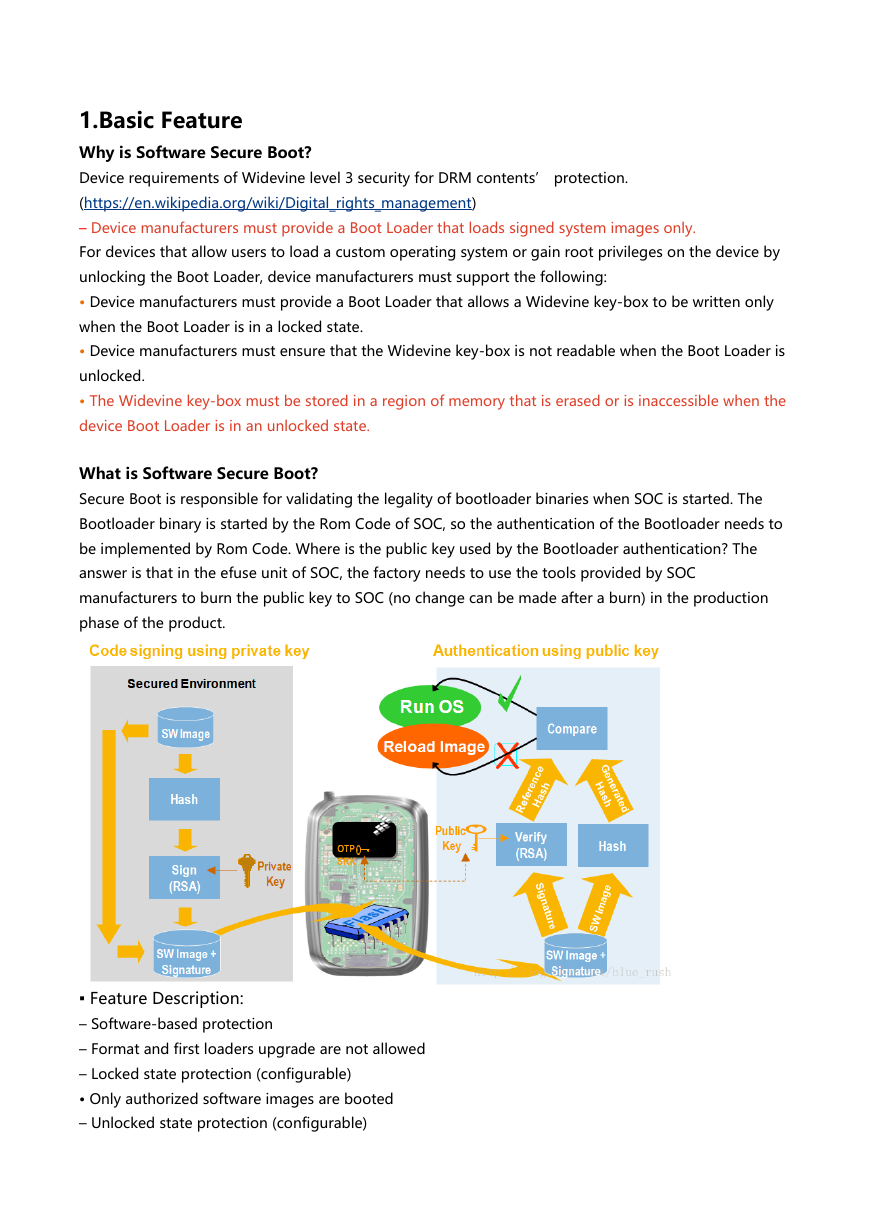
What is Software Secure Boot?
Secure Boot is responsible for validating the legality of bootloader binaries when SOC is started. The
Bootloader binary is started by the Rom Code of SOC, so the authentication of the Bootloader needs to
be implemented by Rom Code. Where is the public key used by the Bootloader authentication? The
answer is that in the efuse unit of SOC, the factory needs to use the tools provided by SOC
manufacturers to burn the public key to SOC (no change can be made after a burn) in the production
phase of the product.
▪ Feature Description:
– Software-based protection
– Format and first loaders upgrade are not allowed
– Locked state protection (configurable)
• Only authorized software images are booted
– Unlocked state protection (configurable)
�
• Non-authorized software images are booted
• Key-box should be cleaned
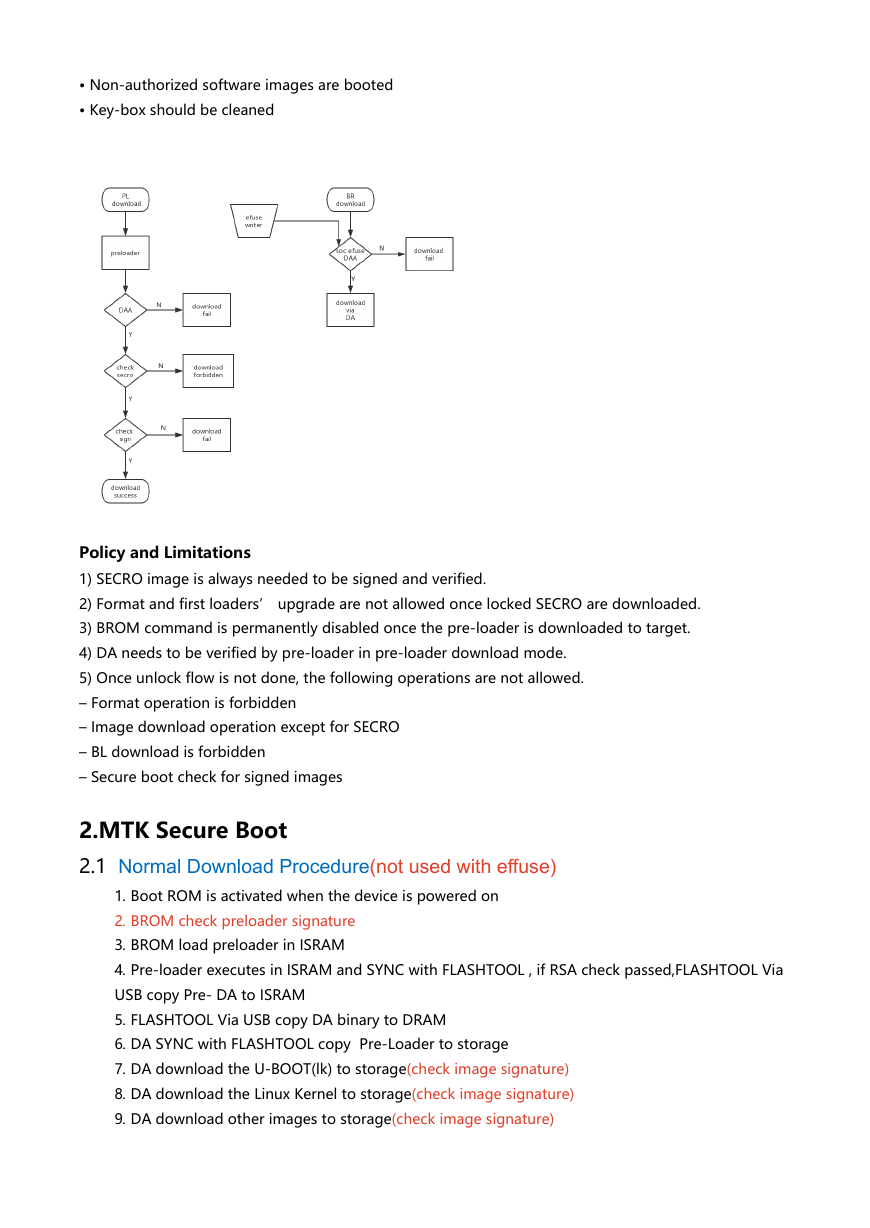
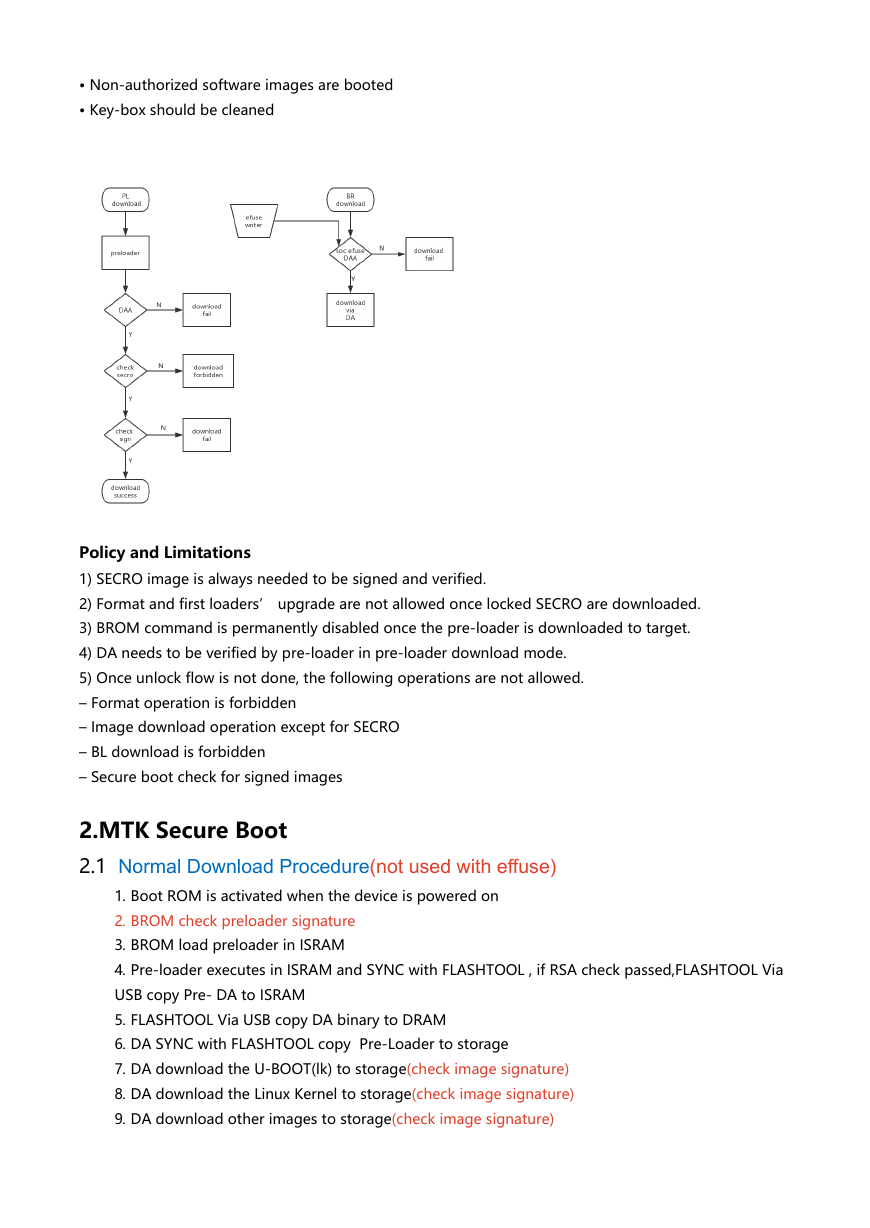
Policy and Limitations
1) SECRO image is always needed to be signed and verified.
2) Format and first loaders’ upgrade are not allowed once locked SECRO are downloaded.
3) BROM command is permanently disabled once the pre-loader is downloaded to target.
4) DA needs to be verified by pre-loader in pre-loader download mode.
5) Once unlock flow is not done, the following operations are not allowed.
– Format operation is forbidden
– Image download operation except for SECRO
– BL download is forbidden
– Secure boot check for signed images
2.MTK Secure Boot
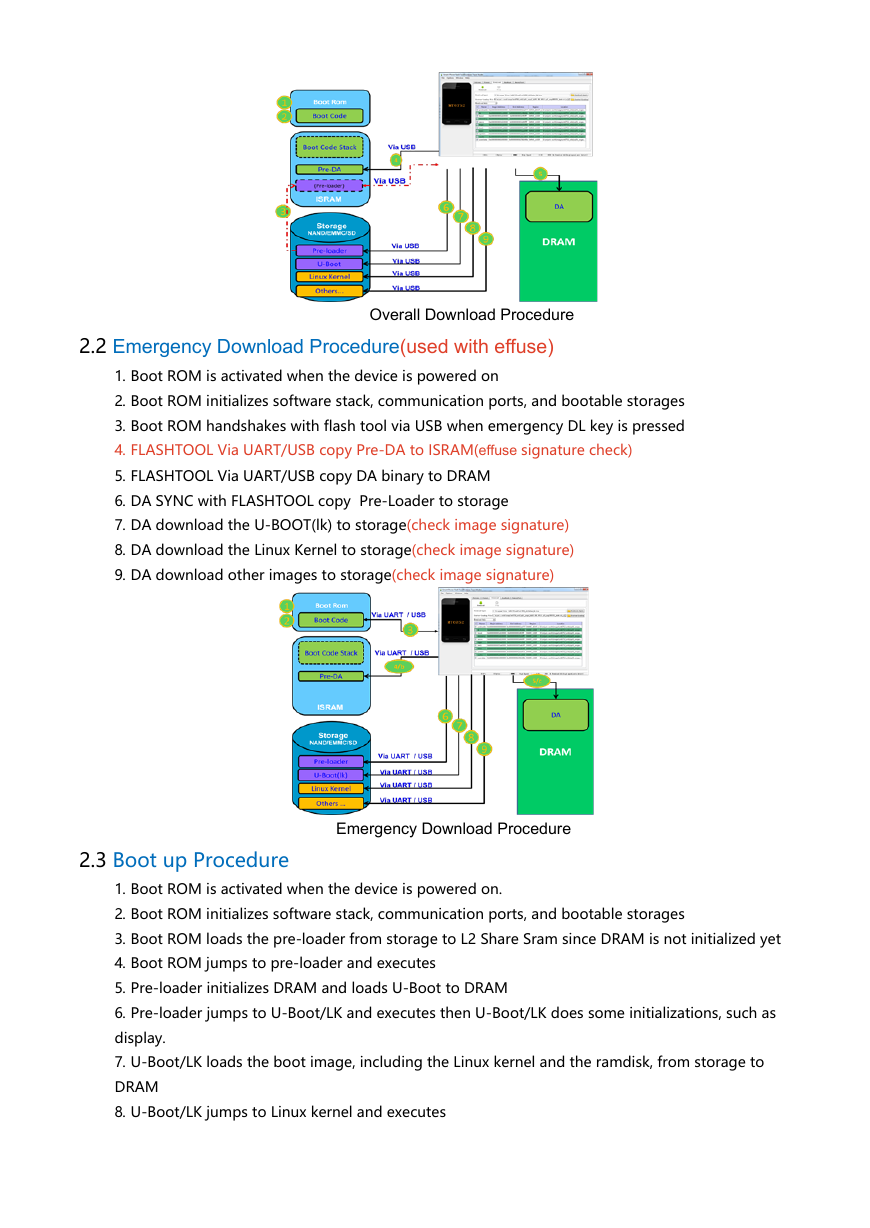
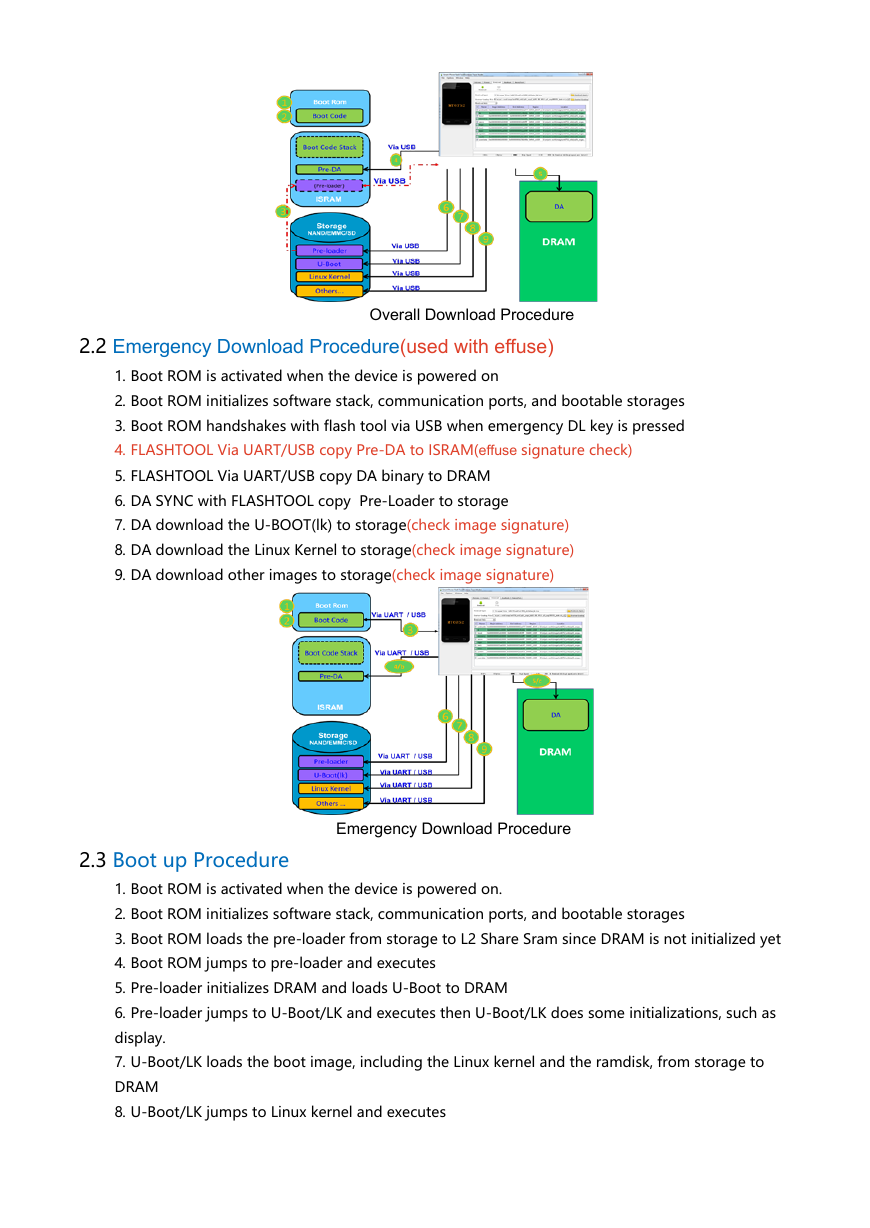
2.1 Normal Download Procedure(not used with effuse)
1. Boot ROM is activated when the device is powered on
2. BROM check preloader signature
3. BROM load preloader in ISRAM
4. Pre-loader executes in ISRAM and SYNC with FLASHTOOL , if RSA check passed,FLASHTOOL Via
USB copy Pre- DA to ISRAM
5. FLASHTOOL Via USB copy DA binary to DRAM
6. DA SYNC with FLASHTOOL copy Pre-Loader to storage
7. DA download the U-BOOT(lk) to storage(check image signature)
8. DA download the Linux Kernel to storage(check image signature)
9. DA download other images to storage(check image signature)
�
2.2 Emergency Download Procedure(used with effuse)
Overall Download Procedure
1. Boot ROM is activated when the device is powered on
2. Boot ROM initializes software stack, communication ports, and bootable storages
3. Boot ROM handshakes with flash tool via USB when emergency DL key is pressed
4. FLASHTOOL Via UART/USB copy Pre-DA to ISRAM(effuse signature check)
5. FLASHTOOL Via UART/USB copy DA binary to DRAM
6. DA SYNC with FLASHTOOL copy Pre-Loader to storage
7. DA download the U-BOOT(lk) to storage(check image signature)
8. DA download the Linux Kernel to storage(check image signature)
9. DA download other images to storage(check image signature)
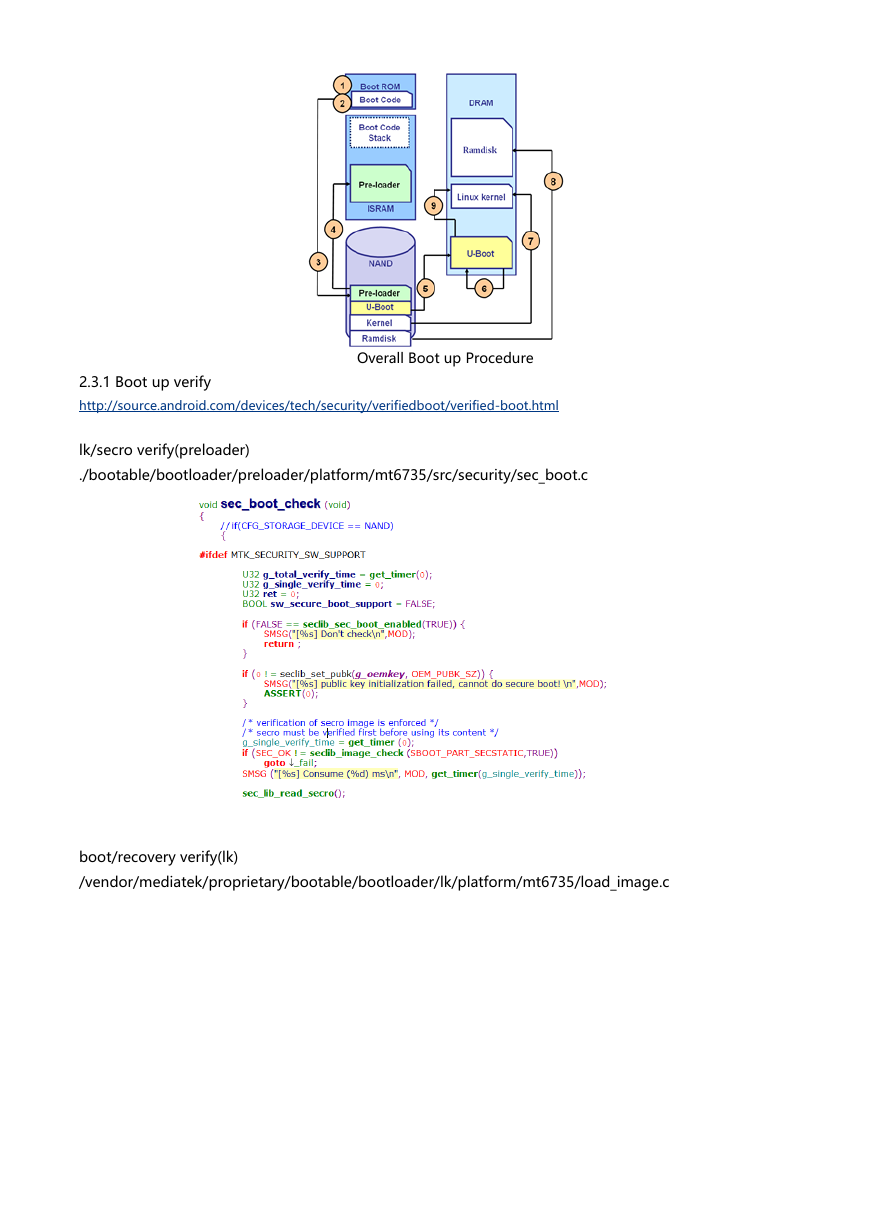
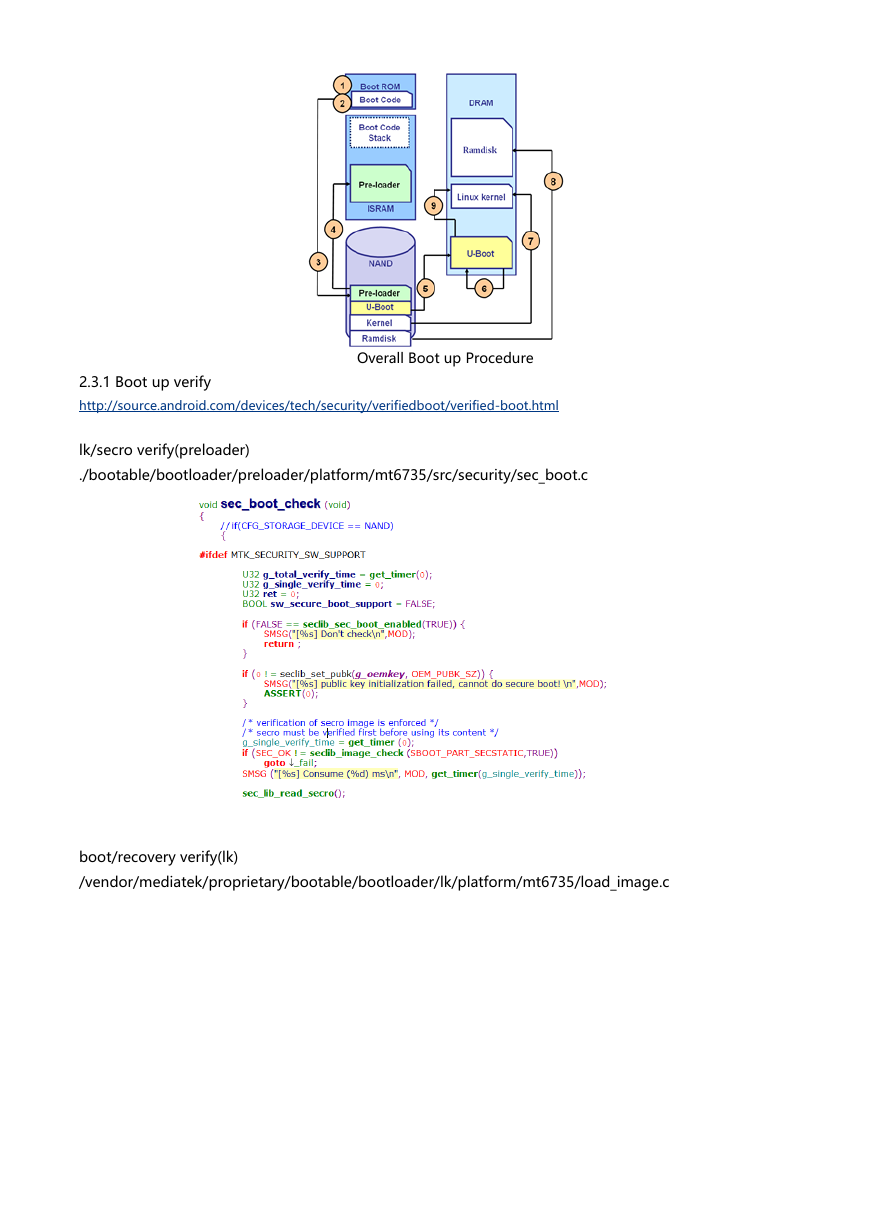
2.3 Boot up Procedure
Emergency Download Procedure
1. Boot ROM is activated when the device is powered on.
2. Boot ROM initializes software stack, communication ports, and bootable storages
3. Boot ROM loads the pre-loader from storage to L2 Share Sram since DRAM is not initialized yet
4. Boot ROM jumps to pre-loader and executes
5. Pre-loader initializes DRAM and loads U-Boot to DRAM
6. Pre-loader jumps to U-Boot/LK and executes then U-Boot/LK does some initializations, such as
display.
7. U-Boot/LK loads the boot image, including the Linux kernel and the ramdisk, from storage to
DRAM
8. U-Boot/LK jumps to Linux kernel and executes
�
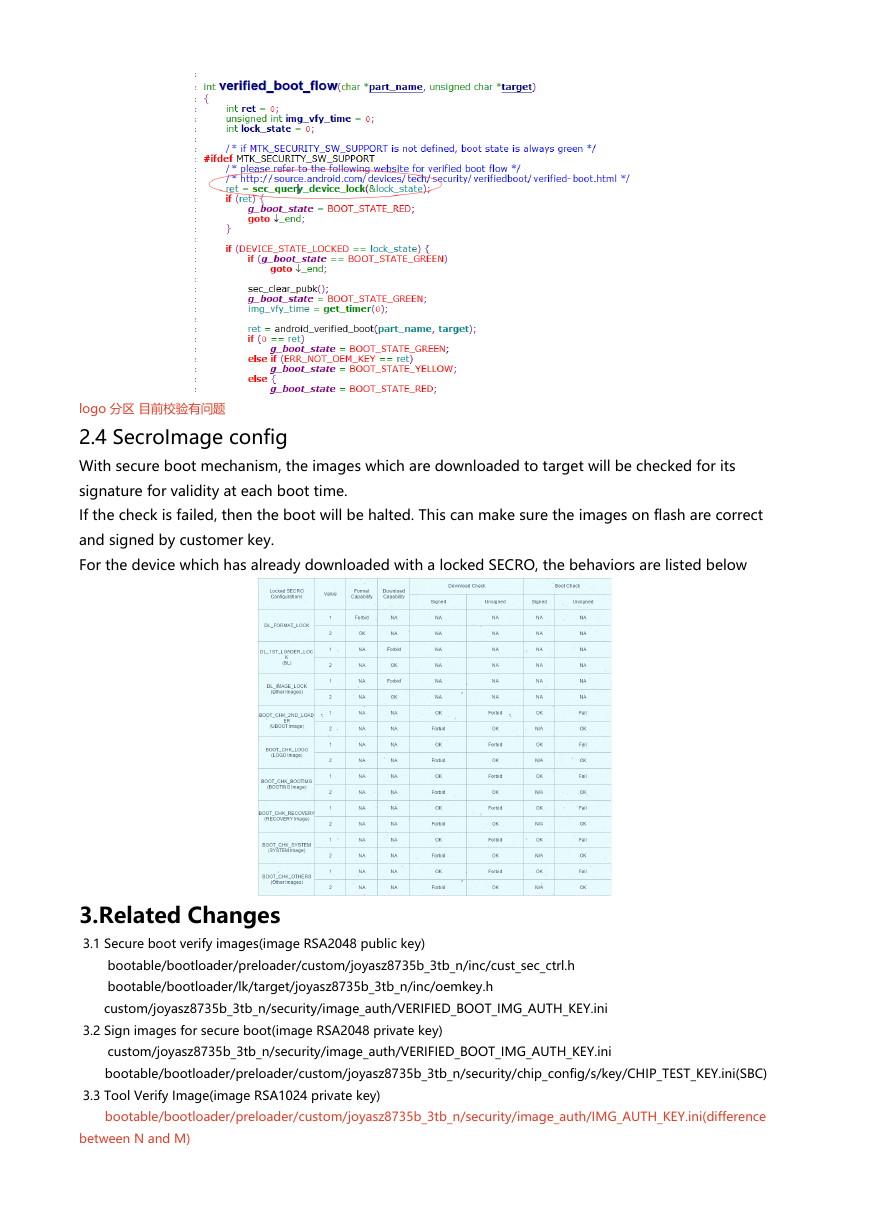
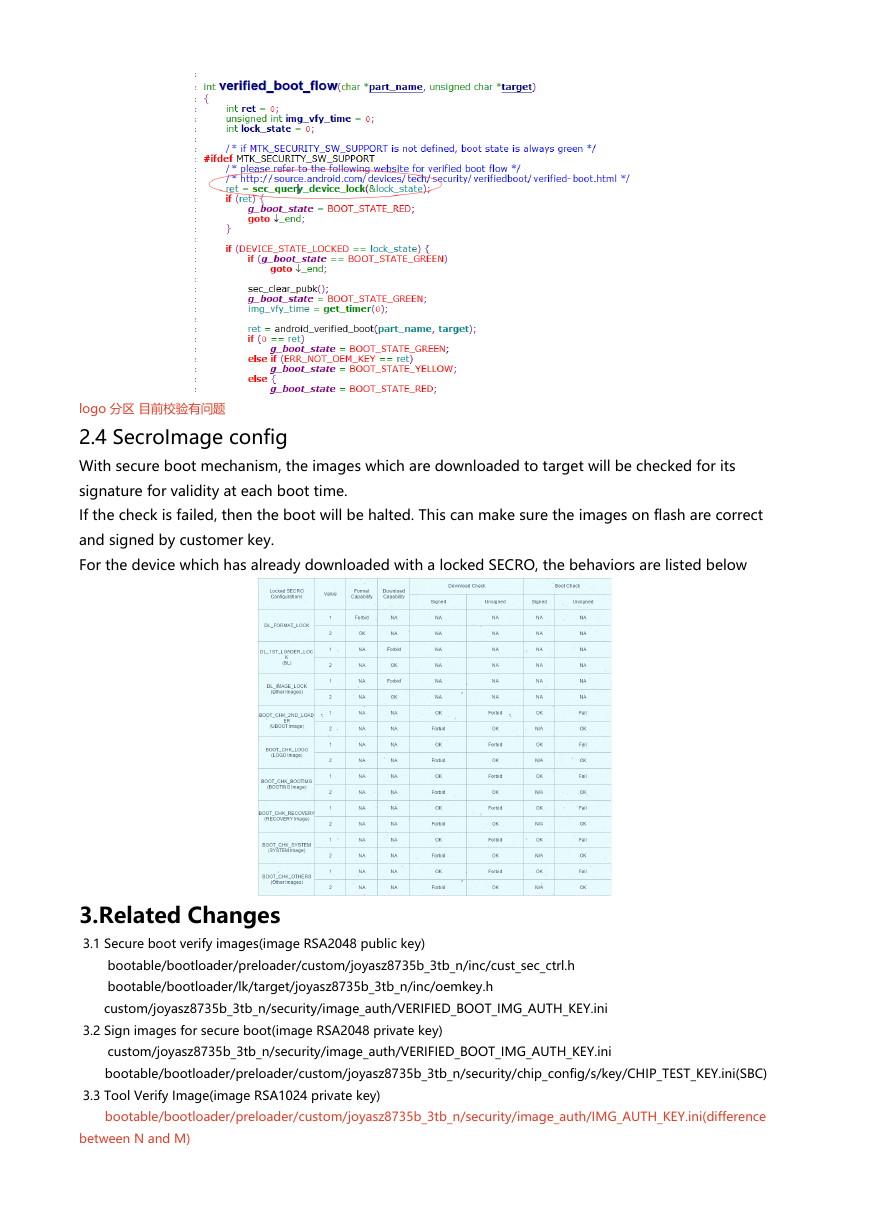
2.3.1 Boot up verify
http://source.android.com/devices/tech/security/verifiedboot/verified-boot.html
Overall Boot up Procedure
lk/secro verify(preloader)
./bootable/bootloader/preloader/platform/mt6735/src/security/sec_boot.c
boot/recovery verify(lk)
/vendor/mediatek/proprietary/bootable/bootloader/lk/platform/mt6735/load_image.c
�
logo 分区 目前校验有问题
2.4 SecroImage config
With secure boot mechanism, the images which are downloaded to target will be checked for its
signature for validity at each boot time.
If the check is failed, then the boot will be halted. This can make sure the images on flash are correct
and signed by customer key.
For the device which has already downloaded with a locked SECRO, the behaviors are listed below
3.Related Changes
3.1 Secure boot verify images(image RSA2048 public key)
bootable/bootloader/preloader/custom/joyasz8735b_3tb_n/inc/cust_sec_ctrl.h
bootable/bootloader/lk/target/joyasz8735b_3tb_n/inc/oemkey.h
custom/joyasz8735b_3tb_n/security/image_auth/VERIFIED_BOOT_IMG_AUTH_KEY.ini
3.2 Sign images for secure boot(image RSA2048 private key)
custom/joyasz8735b_3tb_n/security/image_auth/VERIFIED_BOOT_IMG_AUTH_KEY.ini
bootable/bootloader/preloader/custom/joyasz8735b_3tb_n/security/chip_config/s/key/CHIP_TEST_KEY.ini(SBC)
3.3 Tool Verify Image(image RSA1024 private key)
bootable/bootloader/preloader/custom/joyasz8735b_3tb_n/security/image_auth/IMG_AUTH_KEY.ini(difference
between N and M)
�
custom/joyasz8735b_3tb_n/security/image_auth/IMG_AUTH_KEY.ini
3.4 Preloader verify DA_PL(DA RSA2048 public key)
bootable/bootloader/preloader/custom/joyasz8735b_3tb_n/inc/cust_sec_ctrl.h
3.5 Sign DA
DA_Kit\build\tools\SignDA_SV5.ini(RSA2048)
Customization_Kit_buildspec\custom\security\usbdl4enduser_dummy\VERIFIED_BOOT_IMG_AUTH_KEY.ini(RSA2048)
Customization_Kit_buildspec\custom\security\usbdl4enduser_dummy\dummy_k2.bin(RSA1024)
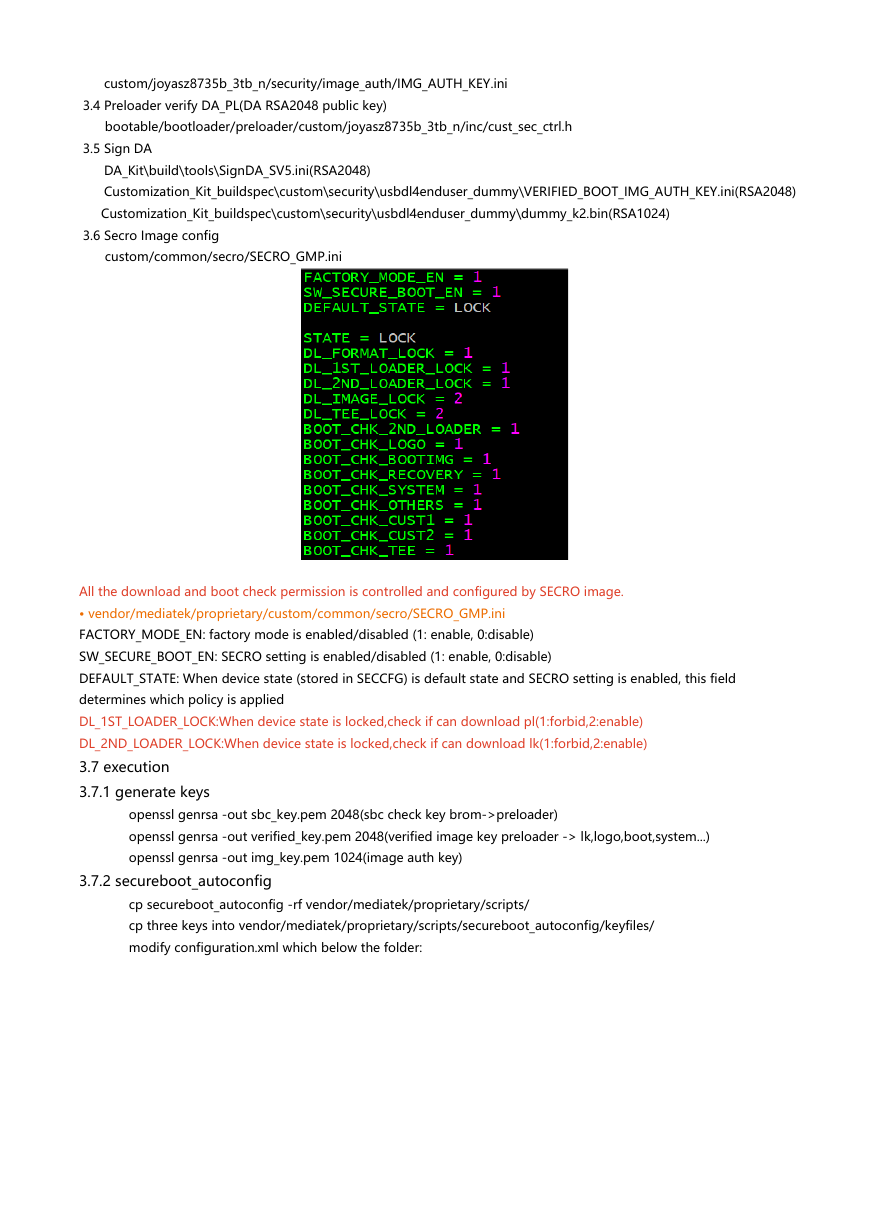
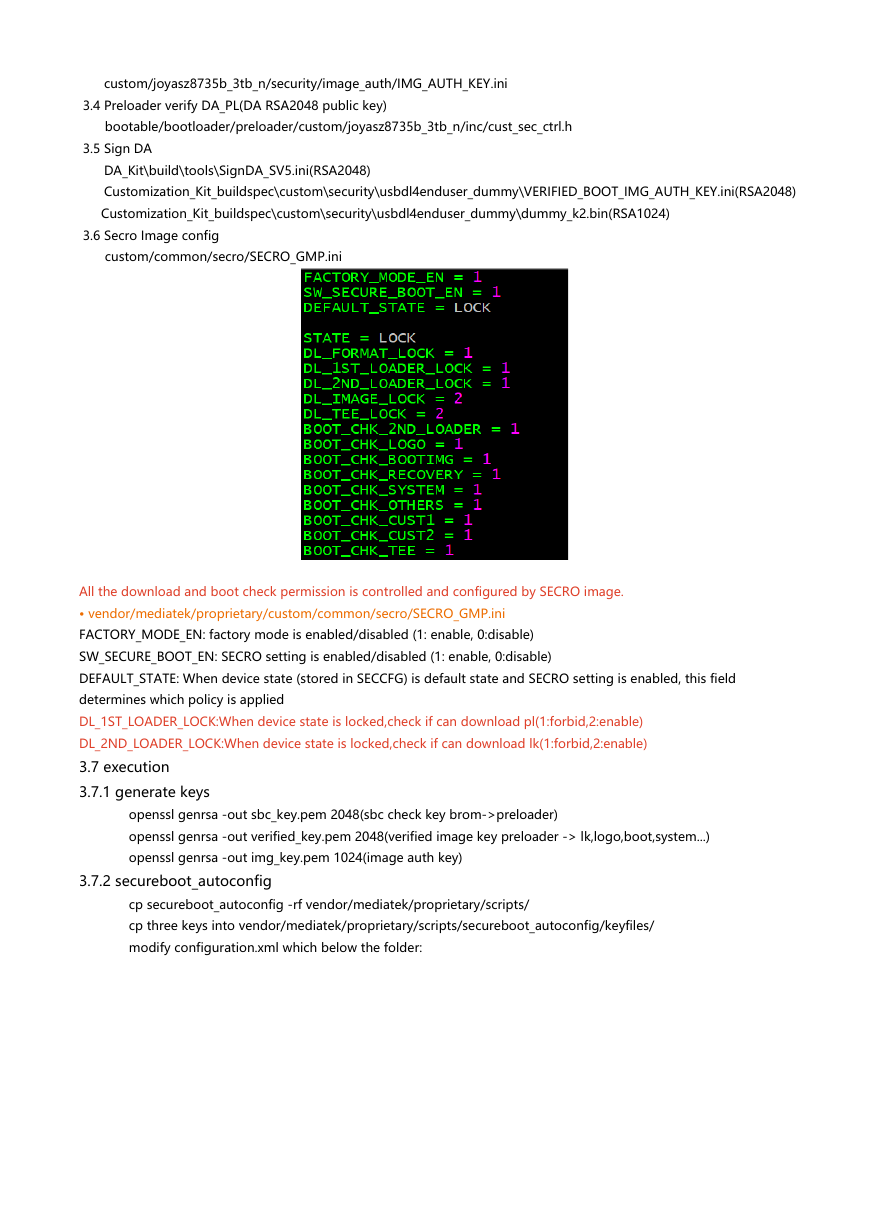
3.6 Secro Image config
custom/common/secro/SECRO_GMP.ini
All the download and boot check permission is controlled and configured by SECRO image.
• vendor/mediatek/proprietary/custom/common/secro/SECRO_GMP.ini
FACTORY_MODE_EN: factory mode is enabled/disabled (1: enable, 0:disable)
SW_SECURE_BOOT_EN: SECRO setting is enabled/disabled (1: enable, 0:disable)
DEFAULT_STATE: When device state (stored in SECCFG) is default state and SECRO setting is enabled, this field
determines which policy is applied
DL_1ST_LOADER_LOCK:When device state is locked,check if can download pl(1:forbid,2:enable)
DL_2ND_LOADER_LOCK:When device state is locked,check if can download lk(1:forbid,2:enable)
3.7 execution
3.7.1 generate keys
openssl genrsa -out sbc_key.pem 2048(sbc check key brom->preloader)
openssl genrsa -out verified_key.pem 2048(verified image key preloader -> lk,logo,boot,system...)
openssl genrsa -out img_key.pem 1024(image auth key)
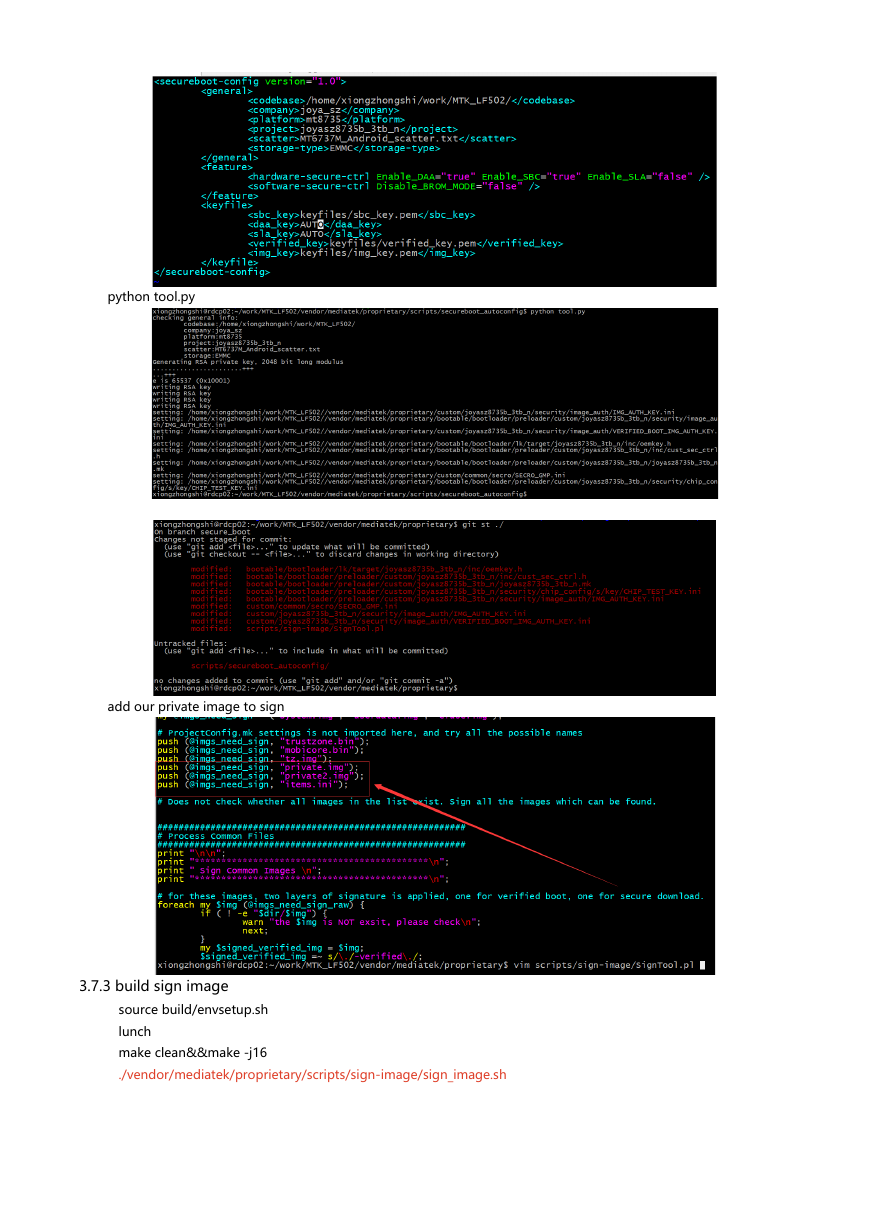
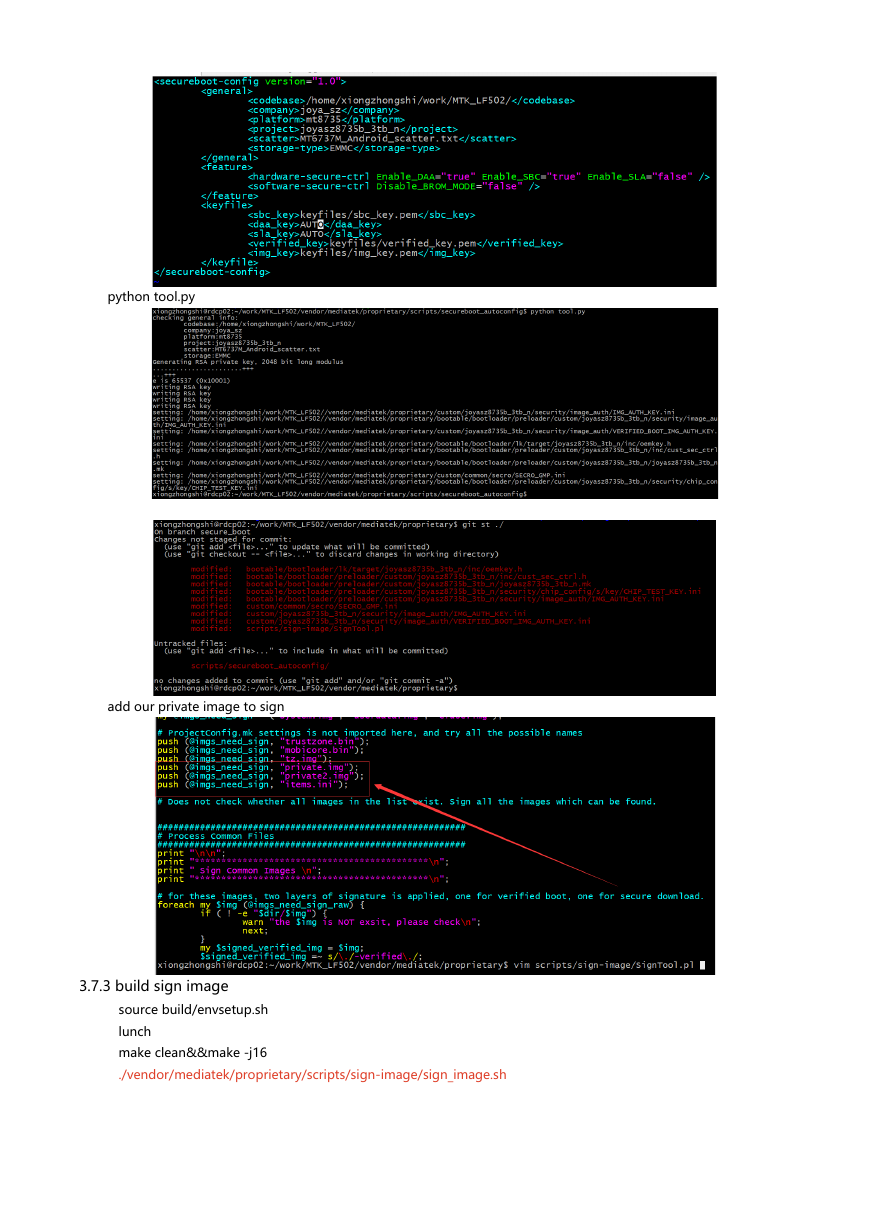
3.7.2 secureboot_autoconfig
cp secureboot_autoconfig -rf vendor/mediatek/proprietary/scripts/
cp three keys into vendor/mediatek/proprietary/scripts/secureboot_autoconfig/keyfiles/
modify configuration.xml which below the folder:
�
python tool.py
add our private image to sign
3.7.3 build sign image
source build/envsetup.sh
lunch
make clean&&make -j16
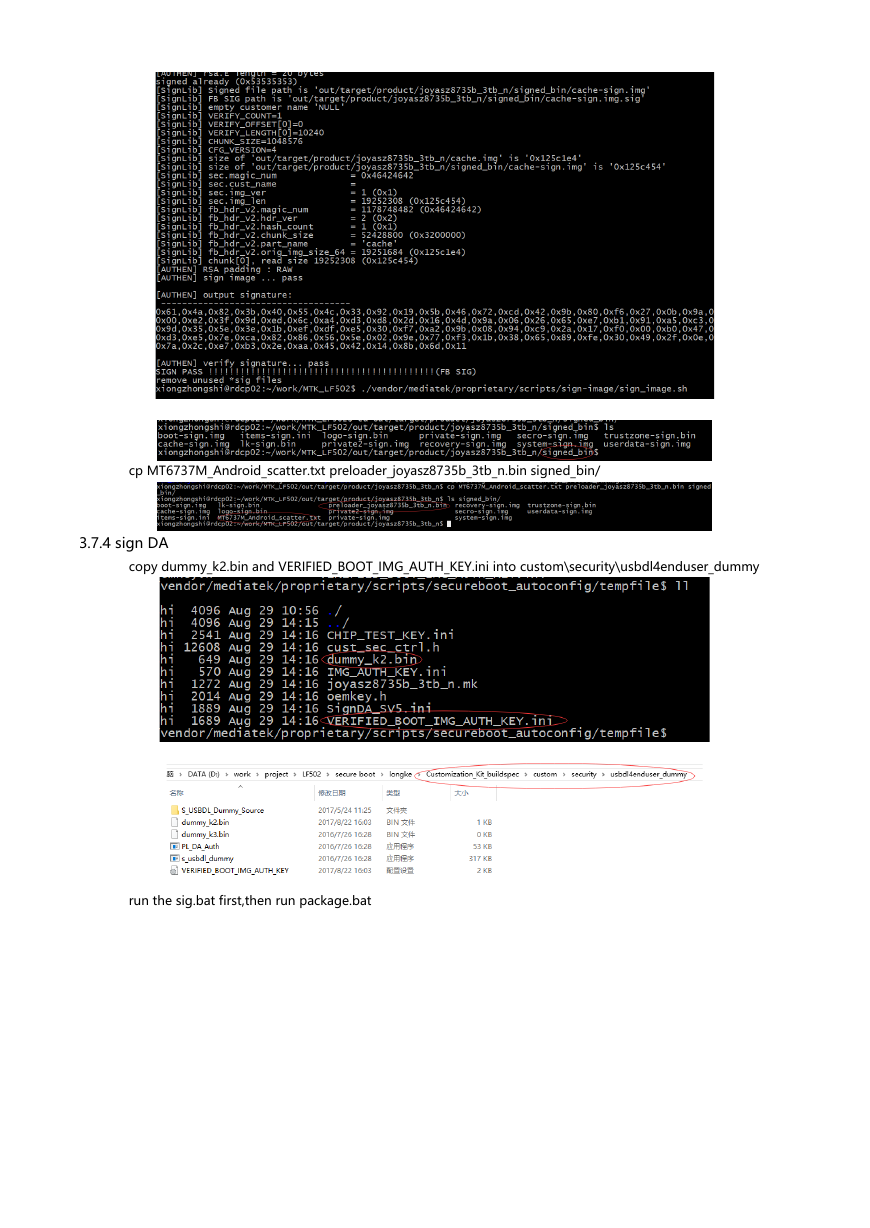
./vendor/mediatek/proprietary/scripts/sign-image/sign_image.sh
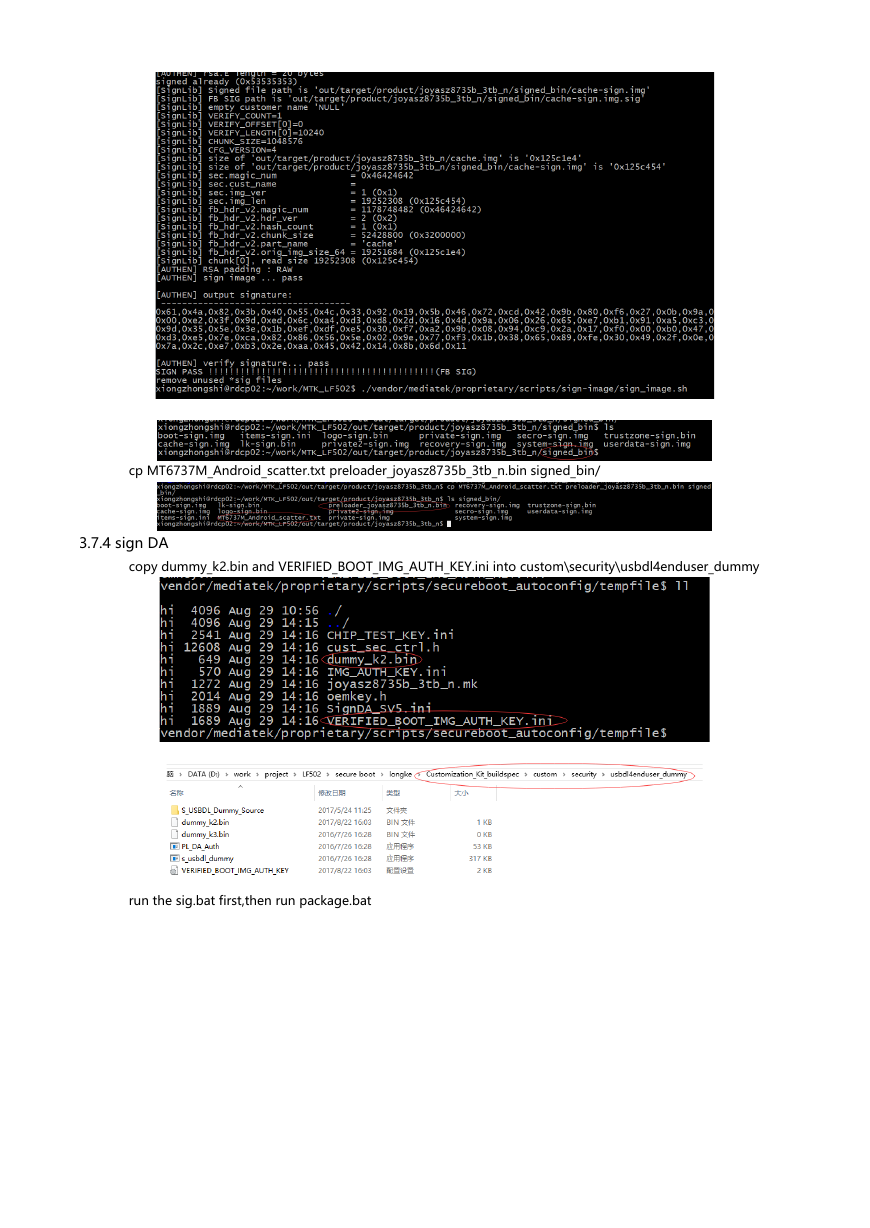
�
cp MT6737M_Android_scatter.txt preloader_joyasz8735b_3tb_n.bin signed_bin/
3.7.4 sign DA
copy dummy_k2.bin and VERIFIED_BOOT_IMG_AUTH_KEY.ini into custom\security\usbdl4enduser_dummy
run the sig.bat first,then run package.bat
�
 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc