The Rootkit Arsenal
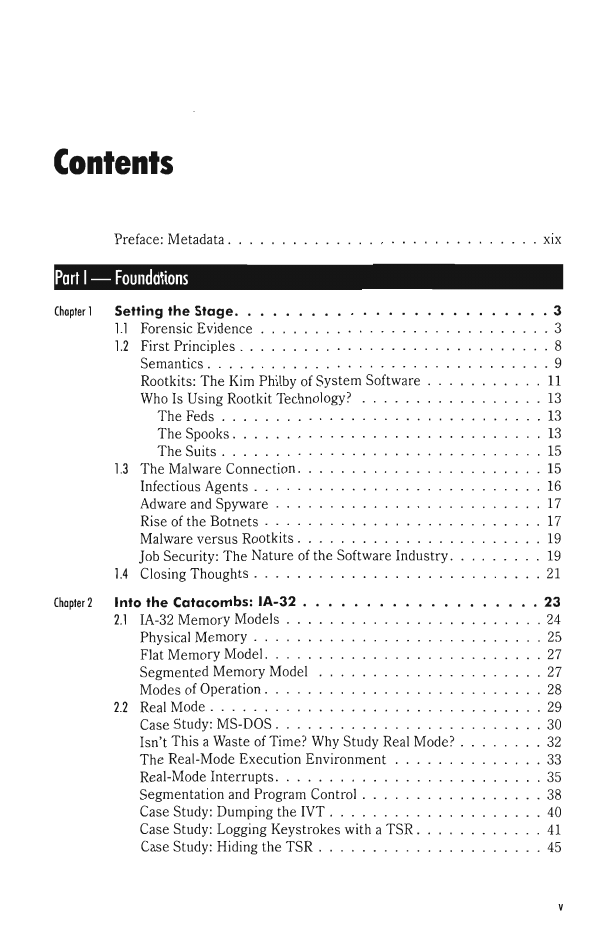
Table of Contents
Preface
Part I - Foundations
Setting the Stage
Forensic Evidence
First Principles
The Malware
Connection
Closing Thoughts
Into the Catacombs: IA-32
IA-32 Memory Models
Real Mode
Protected Mode
Windows System Architecture
Physical Memory
Memory Protection
Virtual Memory
User Mode and Kernel Mode
The Native API
The Boot Process
Design Decisions
Rootkit Basics
Rootkit Tools
Debuggers
A Rootkit Skeleton
Loading a KMD
Installing and Launching a Rootkit
Self-Healing Rootkits
Windows Kernel-Mode Security
Synchronization
Commentary
Part II - System Modification
Hooking Call Tables
Hooking in User Space: The IAT
Hooking in Kernel Space
Hooking Countermeasures
Counter-Countermeasures
Patching System Routines
Run-time Patching
Binary Patching
Instruction Patching Countermeasures
Altering Kernel Objects
The Cost of Invisibility
Revisiting the EPROCESS Object
The DRIVER_SECTION Object
The TOKEN Object
Hiding a Process
Hiding a Driver
Manipulating the Access Token
Using No-FU
Countermeasures
Commentary: Limits of the Two-Ring Model
The Last Lines of Defense
Deploying Filter Drivers
Filter Driver Theory
An Example: Logging Keystrokes
Adding Functionality: Dealing with IRQLs
Key Logging: Alternative Techniques
Other Ways to Use Filter Drivers
Part III - Anti-Forensics
Defeating Live Response
The Live Incident Response Process
RAM Acquisition
Defeating File System Analysis
File System Analysis
Countermeasures: Overview
Countermeasures: Forensic Duplication
Countermeasures: Deleted File Recovery
Countermeasures: Acquiring Metadata
Countermeasures: Removing Known Files
Countermeasures: File Signature Analysis
Countermeasures: Executable Analysis
Borrowing Other Malware Tactics
Defeating Network Analysis
Worst-Case Scenario: Full Content Data Capture
Tunneling: An Overview
The Windows TCP/IP Stack
DNS Tunneling
DNS Tunneling: User Mode
DNS Tunneling: WSK Implementation
NDIS Protocol Drivers
Countermeasure Summary
Live Incident Response
File System Analysis
Network Traffic Analysis
Why Anti-Forensics?
Part IV - End Material
The Tao of Rootkits
Closing Thoughts
Appendix (Code)
Chapter 2
Chapter 3
Chapter 4
Chapter 5
Chapter 6
Chapter 7
Chapter 8
Chapter 10
Chapter 11
Index






 2023年江西萍乡中考道德与法治真题及答案.doc
2023年江西萍乡中考道德与法治真题及答案.doc 2012年重庆南川中考生物真题及答案.doc
2012年重庆南川中考生物真题及答案.doc 2013年江西师范大学地理学综合及文艺理论基础考研真题.doc
2013年江西师范大学地理学综合及文艺理论基础考研真题.doc 2020年四川甘孜小升初语文真题及答案I卷.doc
2020年四川甘孜小升初语文真题及答案I卷.doc 2020年注册岩土工程师专业基础考试真题及答案.doc
2020年注册岩土工程师专业基础考试真题及答案.doc 2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc
2023-2024学年福建省厦门市九年级上学期数学月考试题及答案.doc 2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc
2021-2022学年辽宁省沈阳市大东区九年级上学期语文期末试题及答案.doc 2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc
2022-2023学年北京东城区初三第一学期物理期末试卷及答案.doc 2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc
2018上半年江西教师资格初中地理学科知识与教学能力真题及答案.doc 2012年河北国家公务员申论考试真题及答案-省级.doc
2012年河北国家公务员申论考试真题及答案-省级.doc 2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc
2020-2021学年江苏省扬州市江都区邵樊片九年级上学期数学第一次质量检测试题及答案.doc 2022下半年黑龙江教师资格证中学综合素质真题及答案.doc
2022下半年黑龙江教师资格证中学综合素质真题及答案.doc