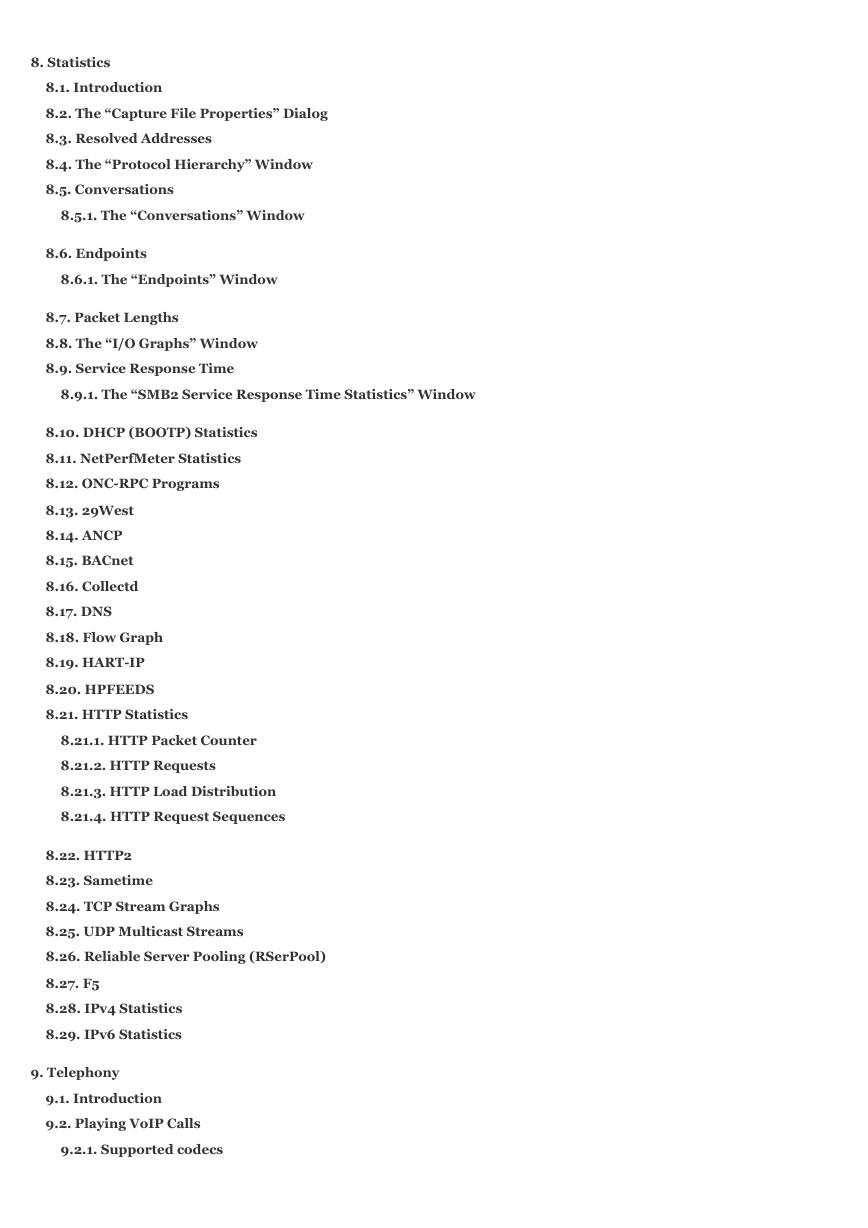
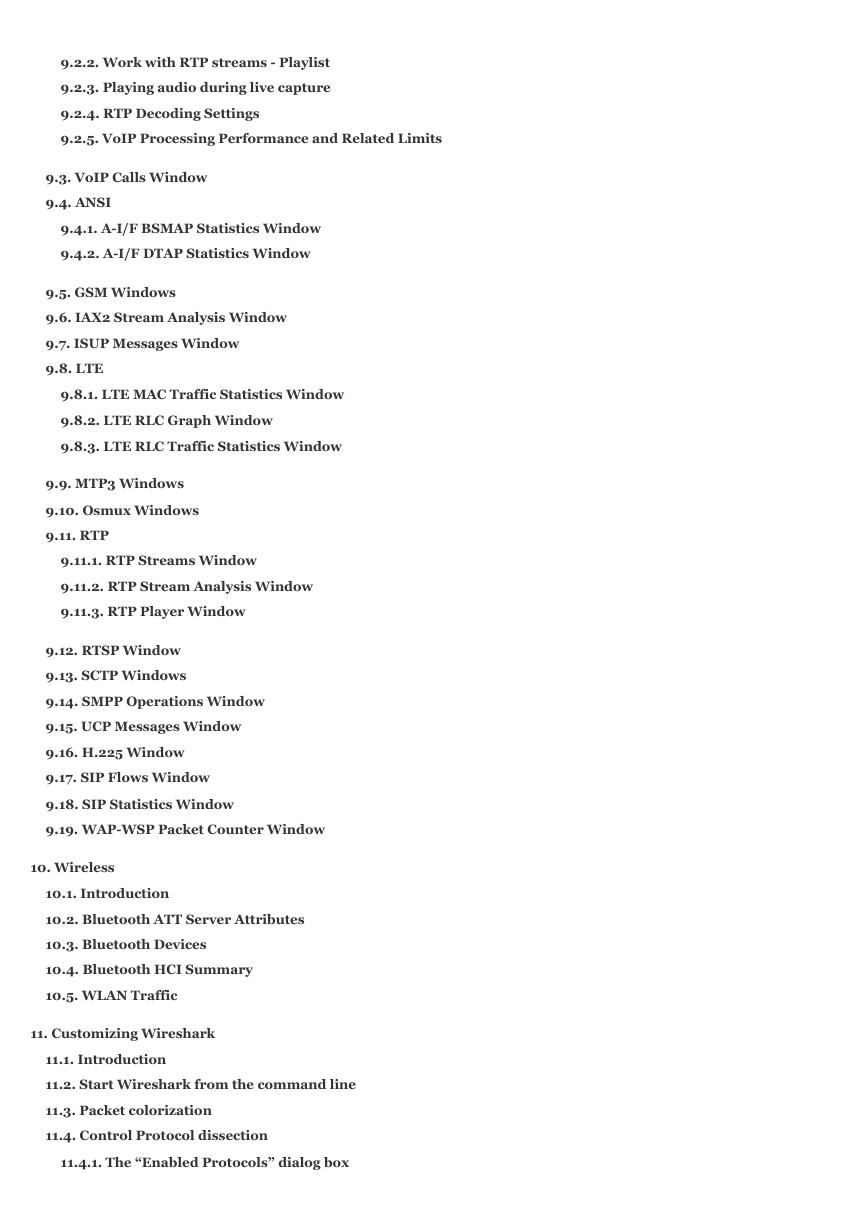
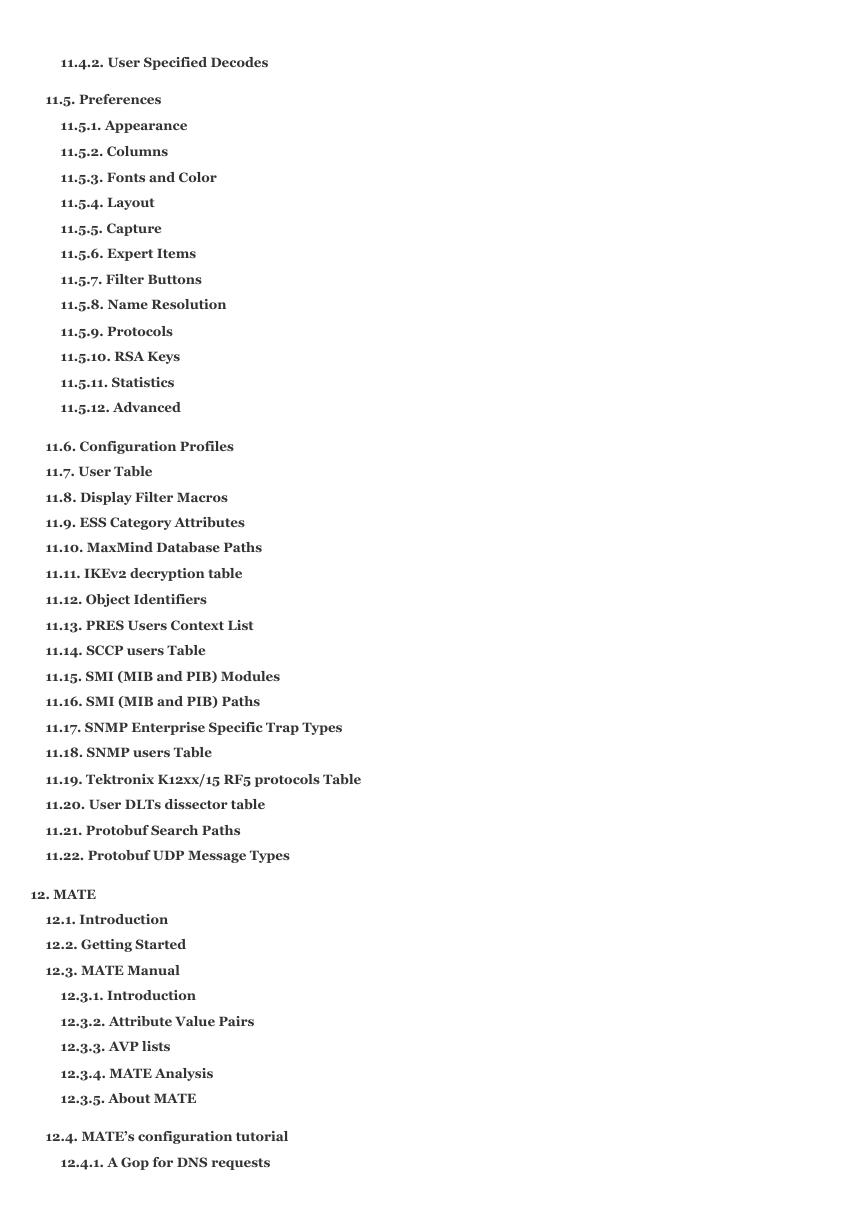
Table of Contents
Preface
1. Foreword
2. Who should read this document?
3. Acknowledgements
4. About this document
5. Where to get the latest copy of this document?
6. Providing feedback about this document
7. Typographic Conventions
7.1. Admonitions
7.2. Shell Prompt and Source Code Examples
1. Introduction
1.1. What is Wireshark?
1.1.1. Some intended purposes
1.1.2. Features
1.1.3. Live capture from many different network media
1.1.4. Import files from many other capture programs
1.1.5. Export files for many other capture programs
1.1.6. Many protocol dissectors
1.1.7. Open Source Software
1.1.8. What Wireshark is not
1.2. System Requirements
1.2.1. Microsoft Windows
1.2.2. macOS
1.2.3. UNIX, Linux, and BSD
1.3. Where To Get Wireshark
1.4. A Brief History Of Wireshark
1.5. Development And Maintenance Of Wireshark
1.6. Reporting Problems And Getting Help
1.6.1. Website
1.6.2. Wiki
1.6.3. Q&A Site
1.6.4. FAQ
1.6.5. Mailing Lists
W
i
r
e
s
h
a
r
k
U
s
e
r
ʼ
s
G
u
i
d
e
V
e
r
s
i
o
n
4
.
2
.
0
R
i
c
h
a
r
d
S
h
a
r
p
e
,
E
d
W
a
r
n
i
c
k
e
,
U
l
f
L
a
m
p
i
n
g
�
1.6.6. Reporting Problems
1.6.7. Reporting Crashes on UNIX/Linux platforms
1.6.8. Reporting Crashes on Windows platforms
2. Building and Installing Wireshark
2.1. Introduction
2.2. Obtaining the source and binary distributions
2.3. Installing Wireshark under Windows
2.3.1. Installation Components
2.3.2. Additional Tasks
2.3.3. Install Location
2.3.4. Installing Npcap
2.3.5. Windows installer command line options
2.3.6. Manual Npcap Installation
2.3.7. Update Npcap
2.3.8. Uninstall Wireshark
2.3.9. Uninstall Npcap
2.4. Building from source under Windows
2.5. Installing Wireshark under macOS
2.6. Installing the binaries under UNIX
2.6.1. Installing from RPMs under Red Hat and alike
2.6.2. Installing from debs under Debian, Ubuntu and other Debian derivatives
2.6.3. Installing from portage under Gentoo Linux
2.6.4. Installing from packages under FreeBSD
2.7. Building from source under UNIX or Linux
2.8. Updating Wireshark
3. User Interface
3.1. Introduction
3.2. Start Wireshark
3.3. The Main window
3.3.1. Main Window Navigation
3.4. The Menu
3.5. The “File” Menu
3.6. The “Edit” Menu
3.7. The “View” Menu
3.8. The “Go” Menu
3.9. The “Capture” Menu
3.10. The “Analyze” Menu
3.11. The “Statistics” Menu
3.12. The “Telephony” Menu
3.13. The “Wireless” Menu
3.14. The “Tools” Menu
�
3.15. The “Help” Menu
3.16. The “Main” Toolbar
3.17. The “Filter” Toolbar
3.18. The “Packet List” Pane
3.19. The “Packet Details” Pane
3.20. The “Packet Bytes” Pane
3.21. The “Packet Diagram” Pane
3.22. The Statusbar
4. Capturing Live Network Data
4.1. Introduction
4.2. Prerequisites
4.3. Start Capturing
4.4. The “Capture” Section Of The Welcome Screen
4.5. The “Capture Options” Dialog Box
4.6. The “Manage Interfaces” Dialog Box
4.7. The “Compiled Filter Output” Dialog Box
4.8. Capture files and file modes
4.9. Link-layer header type
4.10. Filtering while capturing
4.10.1. Automatic Remote Traffic Filtering
4.11. While a Capture is running …
4.11.1. Stop the running capture
4.11.2. Restart a running capture
5. File Input, Output, And Printing
5.1. Introduction
5.2. Open Capture Files
5.2.1. The “Open Capture File” Dialog Box
5.2.2. Input File Formats
5.3. Saving Captured Packets
5.3.1. The “Save Capture File As” Dialog Box
5.3.2. Output File Formats
5.4. Merging Capture Files
5.4.1. The “Merge With Capture File” Dialog Box
5.5. Import Hex Dump
5.5.1. Standard ASCII Hexdumps
5.5.2. Regular Text Dumps
5.5.3. The “Import From Hex Dump” Dialog Box
5.5.4. File source
5.5.5. Input Format
5.5.6. Encapsulation
�
5.6. File Sets
5.6.1. The “List Files” Dialog Box
5.7. Exporting Data
5.7.1. The “Export Specified Packets” Dialog Box
5.7.2. The “Export Packet Dissections” Dialog Box
5.7.3. The “Export Selected Packet Bytes” Dialog Box
5.7.4. The “Export PDUs to File… ” Dialog Box
5.7.5. The “Strip Headers… ” Dialog Box
5.7.6. The “Export TLS Session Keys… ” Dialog Box
5.7.7. The “Export Objects” Dialog Box
5.8. Printing Packets
5.8.1. The “Print” Dialog Box
5.9. The “Packet Range” Frame
5.10. The Packet Format Frame
6. Working With Captured Packets
6.1. Viewing Packets You Have Captured
6.2. Pop-up Menus
6.2.1. Pop-up Menu Of The “Packet List” Column Header
6.2.2. Pop-up Menu Of The “Packet List” Pane
6.2.3. Pop-up Menu Of The “Packet Details” Pane
6.2.4. Pop-up Menu Of The “Packet Bytes” Pane
6.2.5. Pop-up Menu Of The “Packet Diagram” Pane
6.3. Filtering Packets While Viewing
6.4. Building Display Filter Expressions
6.4.1. Display Filter Fields
6.4.2. Comparing Values
6.4.3. Combining Expressions
6.4.4. Slice Operator
6.4.5. The Layer Operator
6.4.6. Membership Operator
6.4.7. Arithmetic operators
6.4.8. Functions
6.4.9. Sometimes Fields Change Names
6.4.10. Some protocol names can be ambiguous
6.5. The “Display Filter Expression” Dialog Box
6.6. Defining And Saving Filters
6.7. Defining And Saving Filter Macros
6.8. Finding Packets
6.8.1. The “Find Packet” Toolbar
6.9. Go To A Specific Packet
�
6.9.1. The “Go Back” Command
6.9.2. The “Go Forward” Command
6.9.3. The “Go to Packet” Toolbar
6.9.4. The “Go to Corresponding Packet” Command
6.9.5. The “Go to First Packet” Command
6.9.6. The “Go to Last Packet” Command
6.10. Marking Packets
6.11. Ignoring Packets
6.12. Time Display Formats And Time References
6.12.1. Packet Time Referencing
7. Advanced Topics
7.1. Introduction
7.2. Following Protocol Streams
7.3. Show Packet Bytes
7.4. Expert Information
7.4.1. Expert Information Entries
7.4.2. The “Expert Information” Dialog
7.4.3. “Colorized” Protocol Details Tree
7.4.4. “Expert” Packet List Column (Optional)
7.5. TCP Analysis
7.6. Time Stamps
7.6.1. Wireshark Internals
7.6.2. Capture File Formats
7.6.3. Accuracy
7.7. Time Zones
7.7.1. Wireshark and Time Zones
7.8. Packet Reassembly
7.8.1. What Is It?
7.8.2. How Wireshark Handles It
7.8.3. TCP Reassembly
7.9. Name Resolution
7.9.1. Name Resolution Drawbacks
7.9.2. Ethernet Name Resolution (MAC Layer)
7.9.3. IP Name Resolution (Network Layer)
7.9.4. TCP/UDP Port Name Resolution (Transport Layer)
7.9.5. VLAN ID Resolution
7.9.6. SS7 Point Code Resolution
7.10. Checksums
7.10.1. Wireshark Checksum Validation
7.10.2. Checksum Offloading
�
8. Statistics
8.1. Introduction
8.2. The “Capture File Properties” Dialog
8.3. Resolved Addresses
8.4. The “Protocol Hierarchy” Window
8.5. Conversations
8.5.1. The “Conversations” Window
8.6. Endpoints
8.6.1. The “Endpoints” Window
8.7. Packet Lengths
8.8. The “I/O Graphs” Window
8.9. Service Response Time
8.9.1. The “SMB2 Service Response Time Statistics” Window
8.10. DHCP (BOOTP) Statistics
8.11. NetPerfMeter Statistics
8.12. ONC-RPC Programs
8.13. 29West
8.14. ANCP
8.15. BACnet
8.16. Collectd
8.17. DNS
8.18. Flow Graph
8.19. HART-IP
8.20. HPFEEDS
8.21. HTTP Statistics
8.21.1. HTTP Packet Counter
8.21.2. HTTP Requests
8.21.3. HTTP Load Distribution
8.21.4. HTTP Request Sequences
8.22. HTTP2
8.23. Sametime
8.24. TCP Stream Graphs
8.25. UDP Multicast Streams
8.26. Reliable Server Pooling (RSerPool)
8.27. F5
8.28. IPv4 Statistics
8.29. IPv6 Statistics
9. Telephony
9.1. Introduction
9.2. Playing VoIP Calls
9.2.1. Supported codecs
�
9.2.2. Work with RTP streams - Playlist
9.2.3. Playing audio during live capture
9.2.4. RTP Decoding Settings
9.2.5. VoIP Processing Performance and Related Limits
9.3. VoIP Calls Window
9.4. ANSI
9.4.1. A-I/F BSMAP Statistics Window
9.4.2. A-I/F DTAP Statistics Window
9.5. GSM Windows
9.6. IAX2 Stream Analysis Window
9.7. ISUP Messages Window
9.8. LTE
9.8.1. LTE MAC Traffic Statistics Window
9.8.2. LTE RLC Graph Window
9.8.3. LTE RLC Traffic Statistics Window
9.9. MTP3 Windows
9.10. Osmux Windows
9.11. RTP
9.11.1. RTP Streams Window
9.11.2. RTP Stream Analysis Window
9.11.3. RTP Player Window
9.12. RTSP Window
9.13. SCTP Windows
9.14. SMPP Operations Window
9.15. UCP Messages Window
9.16. H.225 Window
9.17. SIP Flows Window
9.18. SIP Statistics Window
9.19. WAP-WSP Packet Counter Window
10. Wireless
10.1. Introduction
10.2. Bluetooth ATT Server Attributes
10.3. Bluetooth Devices
10.4. Bluetooth HCI Summary
10.5. WLAN Traffic
11. Customizing Wireshark
11.1. Introduction
11.2. Start Wireshark from the command line
11.3. Packet colorization
11.4. Control Protocol dissection
11.4.1. The “Enabled Protocols” dialog box
�
11.4.2. User Specified Decodes
11.5. Preferences
11.5.1. Appearance
11.5.2. Columns
11.5.3. Fonts and Color
11.5.4. Layout
11.5.5. Capture
11.5.6. Expert Items
11.5.7. Filter Buttons
11.5.8. Name Resolution
11.5.9. Protocols
11.5.10. RSA Keys
11.5.11. Statistics
11.5.12. Advanced
11.6. Configuration Profiles
11.7. User Table
11.8. Display Filter Macros
11.9. ESS Category Attributes
11.10. MaxMind Database Paths
11.11. IKEv2 decryption table
11.12. Object Identifiers
11.13. PRES Users Context List
11.14. SCCP users Table
11.15. SMI (MIB and PIB) Modules
11.16. SMI (MIB and PIB) Paths
11.17. SNMP Enterprise Specific Trap Types
11.18. SNMP users Table
11.19. Tektronix K12xx/15 RF5 protocols Table
11.20. User DLTs dissector table
11.21. Protobuf Search Paths
11.22. Protobuf UDP Message Types
12. MATE
12.1. Introduction
12.2. Getting Started
12.3. MATE Manual
12.3.1. Introduction
12.3.2. Attribute Value Pairs
12.3.3. AVP lists
12.3.4. MATE Analysis
12.3.5. About MATE
12.4. MATE’s configuration tutorial
12.4.1. A Gop for DNS requests
�